Cybersecurity analysts have shared new details about a cyberattack attempt that targeted a major real estate company in the United States. The attackers used an emerging command and control framework known as Tuoni. Although the intrusion was unsuccessful, the campaign reveals a concerning trend where red team tools are frequently abused for malicious operations.
Tuoni C2 Framework Overview
Tuoni is promoted as an advanced command and control framework built for penetration testers, red teams, and security assessments. A Community Edition can be downloaded freely from GitHub. The framework was first released in early 2024.
According to Morphisec researcher Shmuel Uzan, the attackers used Tuoni to deliver stealthy payloads that run directly in memory without writing files to disk.
Attack Timeline and Initial Access
Morphisec reports that the attack took place in mid October 2025. The threat actor, whose identity remains unknown, likely gained initial access through social engineering on Microsoft Teams.
The attacker pretended to be a trusted vendor or colleague and convinced an employee to run a PowerShell command. This script downloaded a second PowerShell loader from an external domain named kupaoquan[dot]com.
Steganography Based Payload Delivery
The downloaded script used steganographic techniques to hide its next stage payload inside a BMP image. The hidden payload extracted shellcode and executed it directly in memory, avoiding traditional security detection methods.
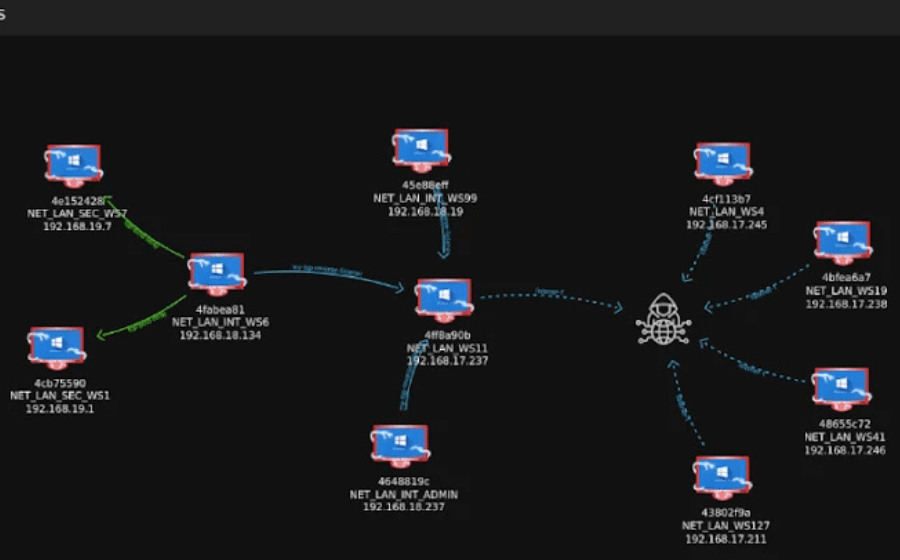
The shellcode then launched TuoniAgent.dll, the Tuoni agent responsible for connecting the compromised machine to its command and control server, which in this case was kupaoquan[dot]com. This connection would have allowed the attacker to control the device remotely.
AI Assisted Attack Components
Morphisec noted that the delivery mechanism showed visible signs of artificial intelligence assistance. This was reflected in scripted comments, a modular loader structure, and code patterns often seen in AI generated scripts.
Although Tuoni itself is a traditional command and control tool, the use of AI in the loading stage made the attack more sophisticated and efficient.
Wider Trend of Red Team Tool Abuse
The attempted attack highlights a growing pattern where red teaming tools are misused for real cybercrime. In September 2025, Check Point researchers revealed the use of an AI powered exploitation assistant called HexStrike AI, which accelerates vulnerability exploitation for threat actors.