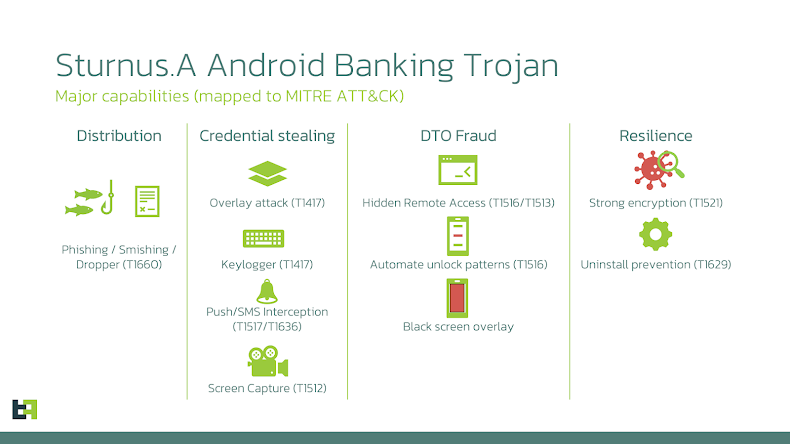
A newly identified Android banking trojan called Sturnus is raising significant concern among security researchers due to its advanced ability to steal credentials, monitor encrypted messaging apps, and take full control of infected devices. According to ThreatFabric, which analyzed the malware, Sturnus is designed for high level financial fraud and advanced surveillance, making it a major threat to users across Southern and Central Europe.
How Sturnus Captures Encrypted Chats
One of the most alarming capabilities of Sturnus is its method of bypassing secure chat encryption. Instead of breaking encryption directly, the trojan captures content from the device screen after decryption occurs on the user side. This tactic allows attackers to monitor communications on apps like WhatsApp, Telegram, and Signal without triggering security alerts.
ThreatFabric notes that this approach gives Sturnus a clear advantage over earlier malware families that relied on less reliable data interception techniques.
Use of Overlay Attacks for Credential Theft
Sturnus can display fake login screens over legitimate banking apps. When users enter their credentials, the malware quietly forwards the information to the attacker. These overlays are customized for specific banks across Southern and Central Europe, making them highly convincing.
ThreatFabric reports two packaging identifiers currently linked to the malware:
• Google Chrome (“com.klivkfbky.izaybebnx”)
• Preemix Box (“com.uvxuthoq.noscjahae”)
This suggests that Sturnus is still under active testing and refinement.
Why the Name Sturnus
The name Sturnus was chosen due to the malware’s mixed communication pattern that blends plaintext, AES, and RSA encryption. Researchers describe this pattern as similar to the European starling, scientifically known as Sturnus vulgaris, which is known for combining different sounds in its vocalizations.
Communication and Remote Access Capabilities
Once installed, the trojan connects to a remote server using WebSocket and HTTP channels to register the compromised device and receive instructions. It sets up a dedicated WebSocket line that allows attackers to operate the device remotely through VNC style sessions.
Through Android accessibility permissions, Sturnus can:
• Capture keystrokes
• Track user interface actions
• Read chat content from encrypted messaging apps
• Identify and log visible screen elements
This allows attackers to recreate the device interface on their own systems. They can then remotely perform actions such as clicking, typing, scrolling, granting permissions, launching applications, and enabling a black screen overlay.
Fake Update Screens and Stealth Mode
Sturnus can also display a full screen fake update panel that completely blocks the user from interacting with the device. While the screen shows a simulated system update, the malware quietly performs malicious activities in the background.
If the user navigates to any settings page that could remove the malware’s administrator privileges, Sturnus immediately detects it and redirects the user away. This prevents the victim from uninstalling the malware or removing it via ADB tools.
Data Collection and Device Profiling
The malware regularly gathers detailed information about the device, including:
• Sensor data
• Hardware specifications
• Network conditions
• A complete list of installed applications
This information helps attackers adjust their tactics and maintain persistence without triggering security defenses.