Security analysts have revealed new insights about the Tsundere botnet, a rapidly expanding malware operation that targets Windows systems. Active since mid 2025, the threat uses JavaScript based payloads delivered from a remote command and control server, allowing attackers to execute arbitrary commands and flexibly modify botnet behavior.
Propagation and Infection Mechanisms
Although its initial delivery path remains unclear, investigators have reported that attackers used a legitimate Remote Monitoring and Management tool in at least one case to deploy an MSI installer from a compromised website. The malware samples carry names such as Valorant, r6x, and cs2, which suggests that the operation uses gaming themed lures. These filenames indicate that users looking for pirated or modified game installers may be the primary targets.
The fake MSI package installs Node js and then launches a loader script that decrypts and executes the main payload. It sets up the environment by downloading three legitimate libraries with an npm install command. These libraries include ws, ethers, and pm2.
According to Kaspersky researcher Lisandro Ubiedo, the pm2 module is used to keep the bot running and to maintain persistence by writing entries to the registry so that Tsundere automatically restarts whenever a user logs into Windows.
Kaspersky also identified a PowerShell variant of the same malware. This version deploys Node js on the infected device and downloads ws and ethers, but it does not use pm2. Instead, it achieves persistence by creating a registry value that launches the bot on every login.
Ethereum Based Command Retrieval
One of the most notable features of the Tsundere botnet is its use of the Ethereum blockchain to store details about its WebSocket based command server. Examples include ws://193.24.123[.]68:3011 and ws://185.28.119[.]179:1234. The threat actors update server information through a smart contract, making the infrastructure highly resilient and simple to rotate. The smart contract was created on September 23, 2024 and has processed 26 transactions.
Once the malware retrieves a WebSocket address, it validates the URL and connects to the server to receive JavaScript code. During observation, Kaspersky did not see any additional commands, but emphasized that the ability to evaluate JavaScript gives the botnet operators considerable flexibility to deliver new functions at any time.
Botnet Management and Criminal Ecosystem
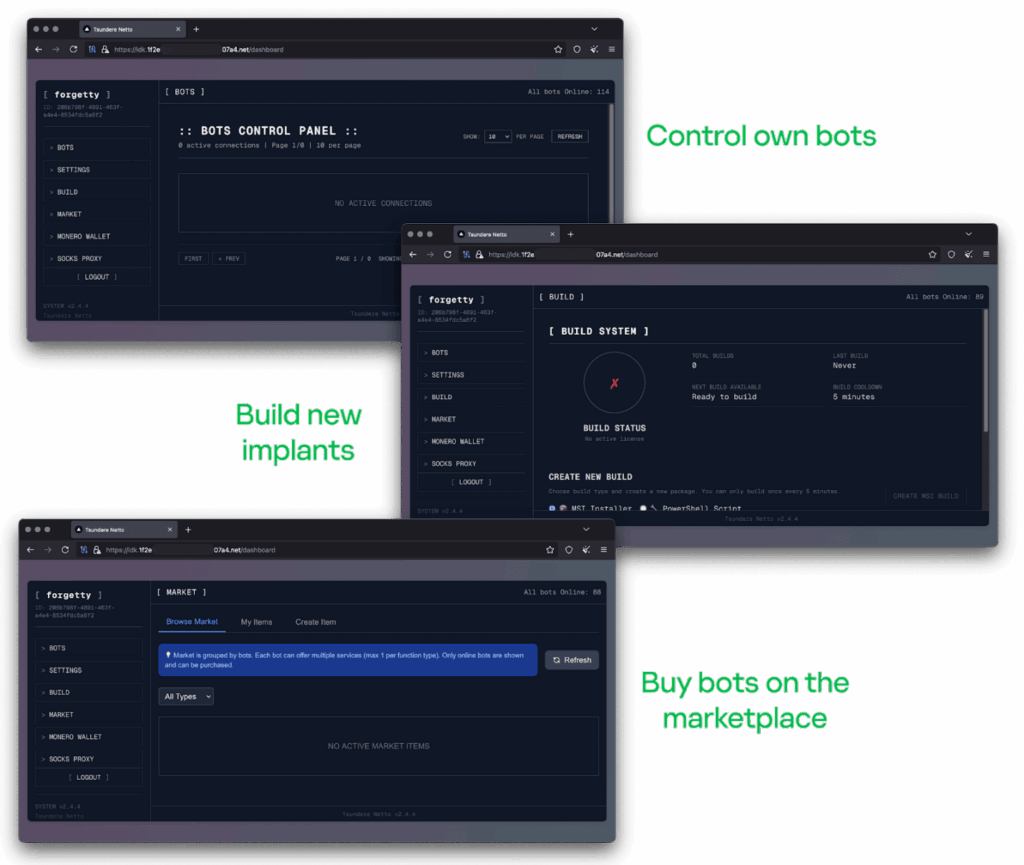
Tsundere is managed through an online control panel where operators can perform multiple tasks. These include generating new botnet installers using PowerShell or MSI, tracking bot counts, enabling proxy usage, and browsing a marketplace where different botnets can be purchased.
The identity of the actors behind this operation remains uncertain. However, Russian language strings found in the code point to a Russian speaking threat group. The botnet shows similarities to malicious npm activity seen by Checkmarx, Phylum, and Socket in late 2024.
Further analysis shows that the same server also hosts the command panel for an information stealing malware known as 123 Stealer, which is sold for 120 dollars per month. The malware was advertised on a dark web forum by a threat actor named koneko on June 17, 2025. Customers are specifically barred from targeting Russia or CIS countries and those who break the rule risk having their accounts terminated immediately.


