A new supply chain attack has been identified across the npm ecosystem, marking a second wave of activity similar to the earlier Shai Hulud incident. Security companies report that thousands of repositories and hundreds of npm packages were compromised between November 21 and 23, 2025. The latest campaign has been named Sha1 Hulud and involves the use of malicious preinstall scripts designed to steal credentials and infiltrate development environments.
Attack Overview
Security researchers from Aikido, HelixGuard, Koi Security, Socket, Step Security, and Wiz confirmed that the attackers uploaded manipulated npm packages that contain a harmful preinstall component. This variant increases exposure by allowing credential theft during the installation phase in both local builds and production environments.
The earlier Shai Hulud attack, disclosed in September 2025, relied on compromised packages that scanned developer systems for secrets using TruffleHog and then sent stolen credentials to an external server. The attackers also created self replicating infections by publishing tampered versions of npm packages owned by compromised maintainers.
In the latest wave, threat actors embedded a new preinstall script named setup_bun.js which attempts to install or detect the Bun runtime. Once active, it launches a bundled script called bun_environment.js that initializes the malicious workflow.
How the Malicious Payload Works
The harmful payload executes two major workflows:
- Self Hosted Runner Abuse
The malware registers the victim machine as a self hosted runner named “SHA1HULUD”. It then creates a workflow file at .github/workflows/discussion.yaml. This workflow contains an injection flaw that allows attackers to run arbitrary commands remotely by simply opening discussions in the repository. - Secret Exfiltration Mechanism
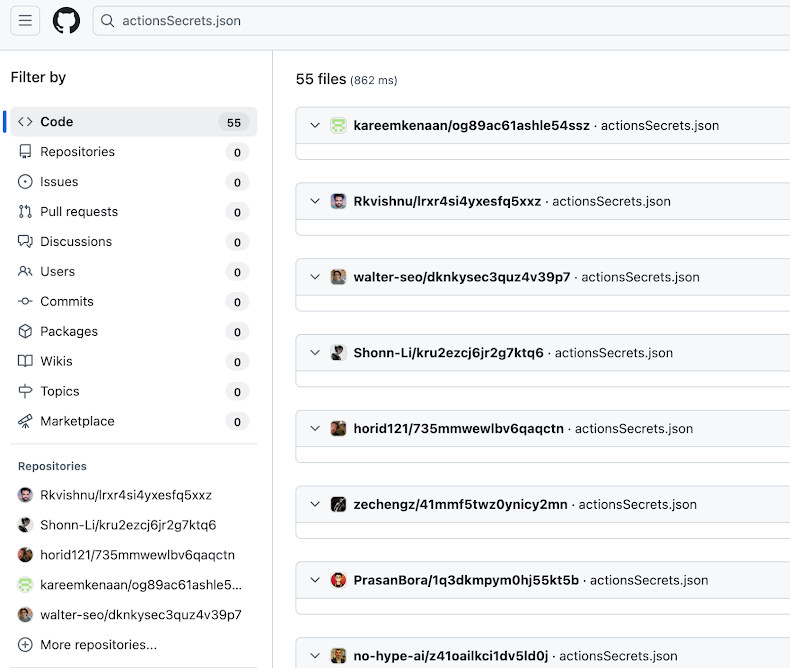
The malware collects secrets stored in the GitHub secrets panel and uploads them as an artifact named actionsSecrets.json to attacker controlled repositories. The file is then downloaded back to the compromised machine, after which the workflow is deleted to erase evidence.
HelixGuard reported that the malware automatically installs and runs TruffleHog to extract sensitive data, which includes npm tokens, AWS and GCP and Azure access credentials, and environment variables.
Scale of the Impact
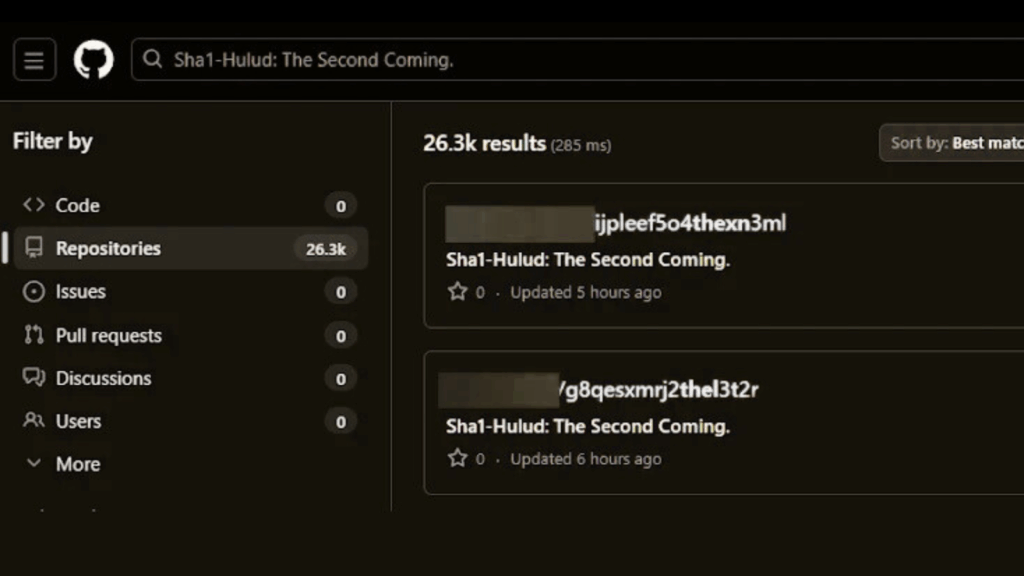
Wiz reported discovering more than 25,000 affected repositories linked to about 350 different users. They also observed that approximately 1,000 new repositories were being added every 30 minutes during peak activity.
According to Wiz, the attackers are using compromised maintainer accounts to publish malicious versions of legitimate npm packages capable of executing credential theft and exfiltration during installation.
Koi Security stated that the second wave is significantly more aggressive than the first one. They found that the malware attempts to wipe the user’s entire home directory if it fails to authenticate or establish persistence. The destructive action deletes every writable file under the user’s home folder, but only when all of the following conditions are met:
- The malware cannot authenticate to GitHub
- It cannot create a GitHub repository
- It cannot access a GitHub token
- It cannot locate an npm token
Researchers Yuval Ronen and Idan Dardikman noted that this shift shows a clear escalation, moving from pure credential theft to punitive sabotage when exfiltration becomes impossible.
The attackers also try to gain root privileges by launching a Docker command that mounts the host’s root filesystem into a privileged container. This allows them to copy a manipulated sudoers file that grants passwordless root access.
Mitigation Recommendations
Security teams are advised to act immediately by taking the following steps:
- Scan all devices for npm packages linked to the Sha1 Hulud campaign.
- Remove affected package versions without delay.
- Rotate all credentials stored locally or in CI/CD environments.
- Audit GitHub repositories for persistence methods, especially workflows such as shai-hulud-workflow.yml or any unexpected branches.
- Monitor for abnormal use of self hosted runners.
- Review Docker usage and privileged container activity on developer systems.