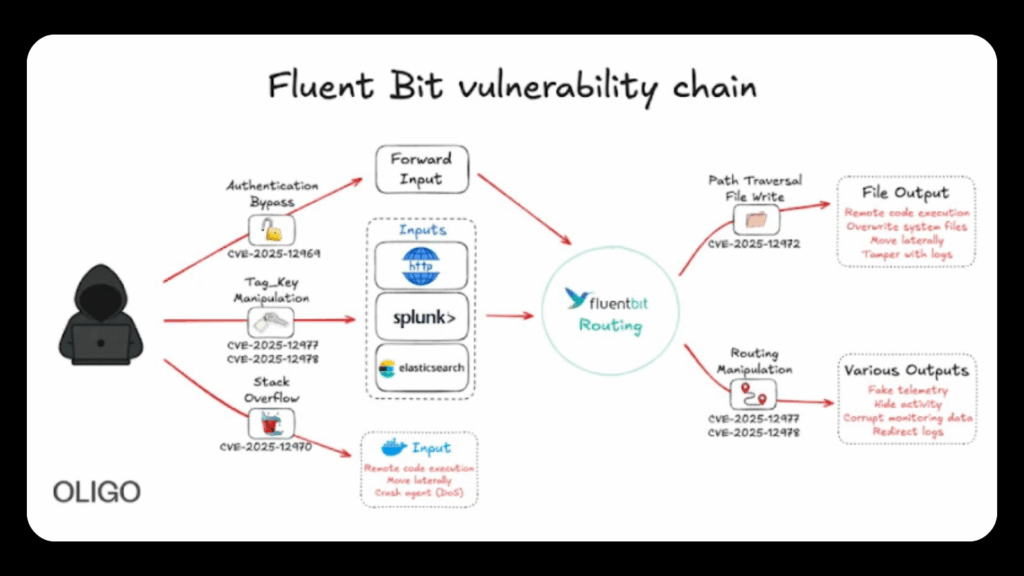
Cybersecurity analysts have identified five significant vulnerabilities in Fluent Bit, a widely used open source telemetry agent. These flaws can be combined to compromise cloud environments and potentially give attackers full control over infrastructure. Oligo Security shared the findings, noting that the weaknesses allow authentication bypass, path traversal, remote code execution, service disruption, and tag manipulation.
Overview of the Threat
Successful exploitation of the flaws can allow attackers to alter logs, inject malicious data, interrupt cloud services, and perform deeper intrusions into containerized and Kubernetes deployments. The vulnerabilities revealed in Fluent Bit include the following:
CVE 2025 12969
A missing authentication requirement in the in_forward plugin. This allows attackers with network access to send false logs, inject harmful telemetry, and overwhelm security monitoring systems with fabricated events.
CVE 2025 12972
A path traversal issue caused by unsanitized tag values that determine output filenames. This allows an attacker to write or overwrite arbitrary files on the target system, enabling log manipulation and remote code execution.
CVE 2025 12970
A stack buffer overflow in the Docker Metrics input plugin (in_docker). By creating containers with very long names, an attacker can trigger a crash or achieve code execution on the agent.
CVE 2025 12978
A weakness in tag matching logic that allows threat actors to spoof trusted tags. By guessing only the first character of a Tag Key, attackers can reroute logs, bypass filters, and introduce falsified or malicious log entries.
CVE 2025 12977
Improper validation of tags derived from user controlled fields. This flaw allows injection of traversal characters, newlines, and control sequences that corrupt downstream logs.
Impact and Research Findings
According to researchers, these vulnerabilities provide attackers with enough control to execute malicious code inside cloud environments using Fluent Bit as the entry point. They can decide which events are logged, hide their own activity by deleting records, inject deceptive telemetry, and mislead incident responders with manufactured events.
An advisory from the CERT Coordination Center confirmed that these vulnerabilities can be abused for authentication bypass, remote code execution, service disruption, and tag manipulation. Many of the attacks require network level access to a Fluent Bit instance.
Patches and Vendor Response
All five vulnerabilities were fixed following responsible disclosure. The patches were included in versions 4.1.1 and 4.0.12, which became available last month. Amazon Web Services also participated in coordinated disclosure and urged all customers using Fluent Bit to update immediately to ensure the highest level of protection.
Fluent Bit is widely deployed in enterprise cloud ecosystems, which increases the potential impact of these flaws, particularly in environments that rely heavily on telemetry pipelines and centralized logging.
Mitigation Guidance
Security teams are advised to implement the following defense measures:
- Update to Fluent Bit version 4.1.1 or 4.0.12.
- Avoid using dynamic tags for routing.
- Restrict output paths and destinations to prevent tag related traversal or path expansion.
- Mount configuration directories, such as /fluent-bit/etc/, as read only to prevent tampering.
- Run Fluent Bit as a non root user whenever possible.
These recommendations aim to limit the attacker’s ability to manipulate logs, escalate privileges, or tamper with configurations.