The threat group known as ToddyCat has introduced new techniques designed to infiltrate corporate email systems and extract sensitive data from targeted organizations. According to a technical report by Kaspersky, the group is now using a custom tool called TCSectorCopy to obtain access to Microsoft Outlook data and OAuth 2.0 tokens.
Kaspersky noted that this method enables attackers to harvest OAuth tokens from a victim’s browser. These tokens can then be used outside the compromised network to access corporate email accounts and sensitive communication data.
ToddyCat has been active since at least 2020, primarily targeting organizations across Europe and Asia. The group is associated with a set of tools such as Samurai and TomBerBil, which allow persistent access and credential theft from browsers including Google Chrome and Microsoft Edge.
Exploiting Software Flaws and Expanding Capabilities
In April 2024, ToddyCat was linked to the exploitation of a vulnerability in the ESET Command Line Scanner (CVE-2024-11859, CVSS 6.8) to deploy a previously unknown malware family known as TCESB.
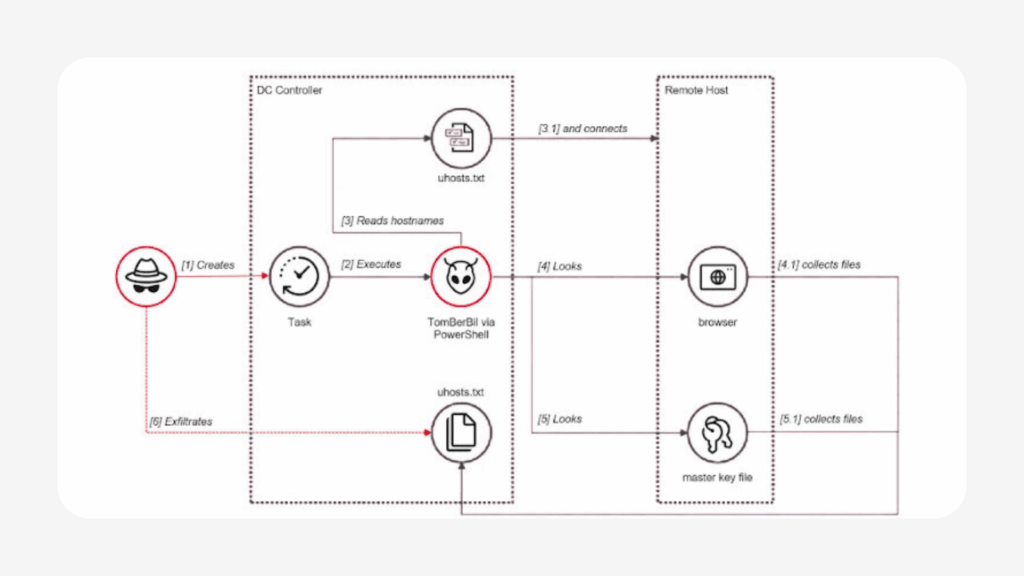
Between May and June 2024, Kaspersky documented a PowerShell version of TomBerBil, expanding on earlier C++ and C# variants. The new version can extract data from Mozilla Firefox and is capable of running on domain controllers with elevated privileges. It accesses browser files stored on remote systems through SMB shared resources.
The malware is launched using a scheduled task that triggers a PowerShell command. Once active, it searches remote hosts for browser histories, saved passwords, cookies, and credential files. Although these files are protected by Windows DPAPI encryption, TomBerBil captures the required master decryption keys.
Kaspersky explained that earlier versions relied on the compromised user’s session token to decrypt DPAPI keys. The new server side variant instead copies the DPAPI encryption keys themselves, which attackers later decrypt using the victim’s SID and password, gaining full access to the extracted files.
Using TCSectorCopy to Steal Outlook OST Files
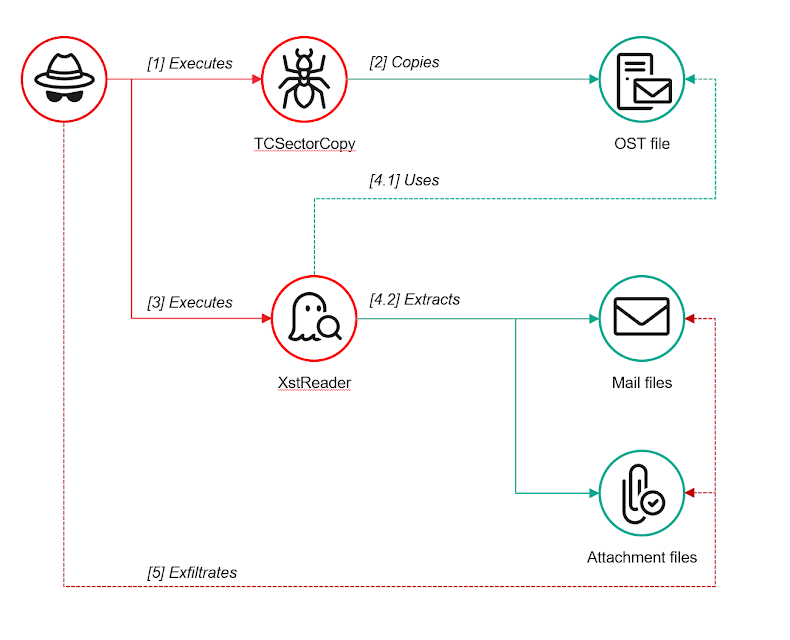
ToddyCat operators have further been observed accessing Outlook data stored locally in OST files using TCSectorCopy, also known as xCopy.exe. This method bypasses restrictions that normally prevent access to OST files while Outlook is running.
Written in C plus plus, TCSectorCopy opens the system disk in read only mode and copies the contents of the OST file sector by sector. Once copied, attackers use XstReader, an open source utility, to extract emails from the stolen files.
Token Theft from Microsoft 365 Environments
The group is also attempting to extract Microsoft 365 tokens directly from memory. For this purpose, ToddyCat uses SharpTokenFinder, an open source C sharp utility that scans for plaintext authentication tokens within Microsoft 365 related processes.
However, in at least one case, endpoint security software blocked their attempt to dump the Outlook.exe process using SharpTokenFinder. To bypass this restriction, the attackers switched to the Sysinternals ProcDump tool, using specific arguments to successfully capture a memory dump of the Outlook process.
Kaspersky stressed that ToddyCat continues to refine its methods to maintain stealth and expand access to corporate email systems within compromised environments.