A newly uncovered malware campaign is exploiting adult themed phishing sites and deceptive ClickFix style lures to trick users into executing malicious Windows commands disguised as urgent security updates. Cybersecurity researchers from Acronis have identified the activity, warning that the threat actors are using highly convincing fake Windows update screens to distribute multiple information stealers.
According to the report, attackers are deploying cloned adult sites resembling platforms like xHamster and PornHub. These sites are likely reached through malvertising and immediately push victims toward running a so called “critical Windows update.” The psychological pressure associated with accessing such websites increases the likelihood of user compliance.
Fake Update Screens Drive ClickFix Attacks
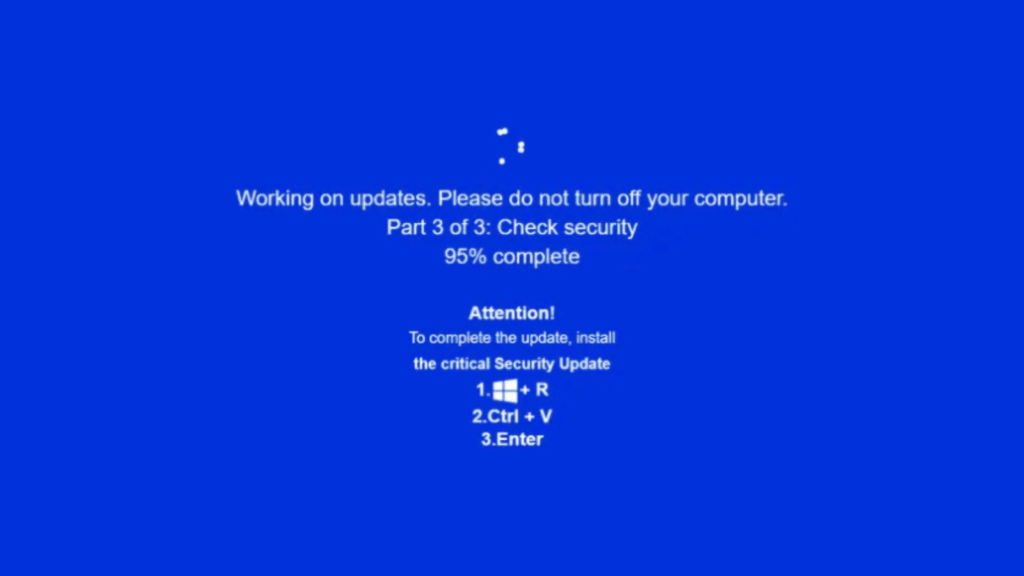
ClickFix attacks have surged over the past year. Microsoft estimates that this technique now accounts for nearly half of all initial access methods. Instead of traditional bot check prompts, the JackFix campaign forces a full screen fake Windows Update alert that instructs victims to open the Run dialog, paste a command, and press Enter. This action triggers the malware deployment chain.
Acronis researchers noted that several versions of the phishing sites include developer comments written in Russian, indicating a possible Russian speaking operator.
The deceptive update window is crafted entirely with HTML and JavaScript, creating an interface that mimics Windows’ blue error screen. While attackers attempt to disable common escape keys like Escape, F11, F5, and F12, flaws in their code still allow victims to exit the screen under certain circumstances.
Malware Delivery Process Uses Obfuscated PowerShell Commands
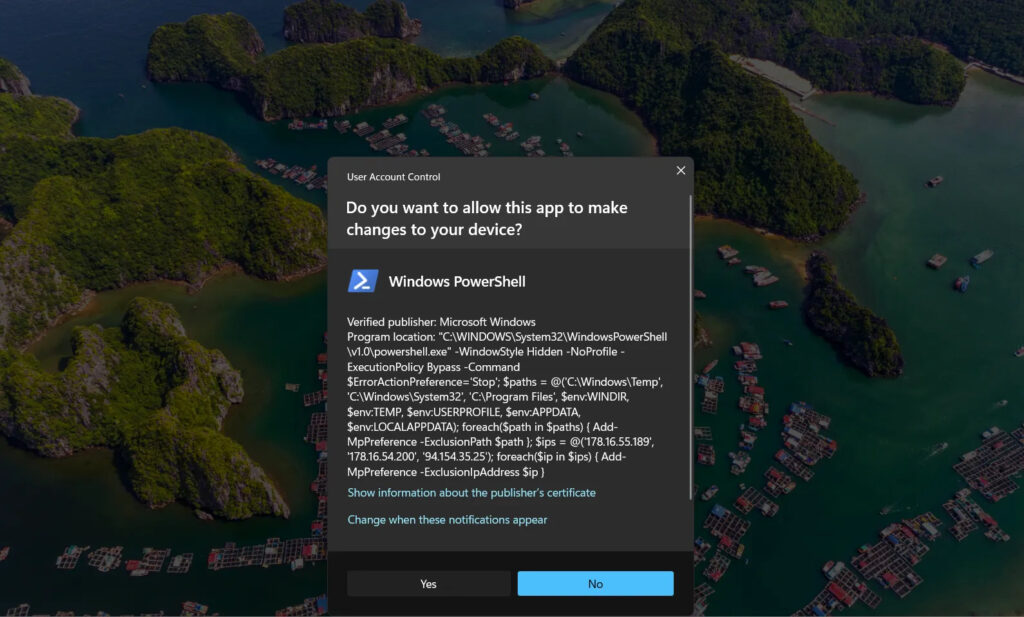
The infection begins with an MSHTA payload launched through the legitimate Windows binary mshta.exe. This payload retrieves a remote PowerShell script containing multiple layers of obfuscation, analysis evasion techniques, and privilege escalation attempts.
To elevate privileges, the malware repeatedly prompts users to approve administrative access. Once granted, the script adds Microsoft Defender Antivirus exclusions for its command and control domains and prepares the environment for additional payloads.
Researchers discovered that the campaign delivers as many as eight different malware families in a single operation. These include Rhadamanthys Stealer, Vidar Stealer 2.0, RedLine Stealer, Amadey, and various loaders and remote access trojans. This scattershot approach greatly increases the likelihood of at least one payload successfully infecting the system.
Related Activity Uses Steganography to Hide Final Payloads
In parallel research, Huntress identified a similar ClickFix chain delivering Lumma and Rhadamanthys stealers. The attack uses the same mshta.exe plus PowerShell technique but hides the final payloads inside a PNG image using steganography. A .NET loader named Stego Loader extracts and executes the hidden shellcode.
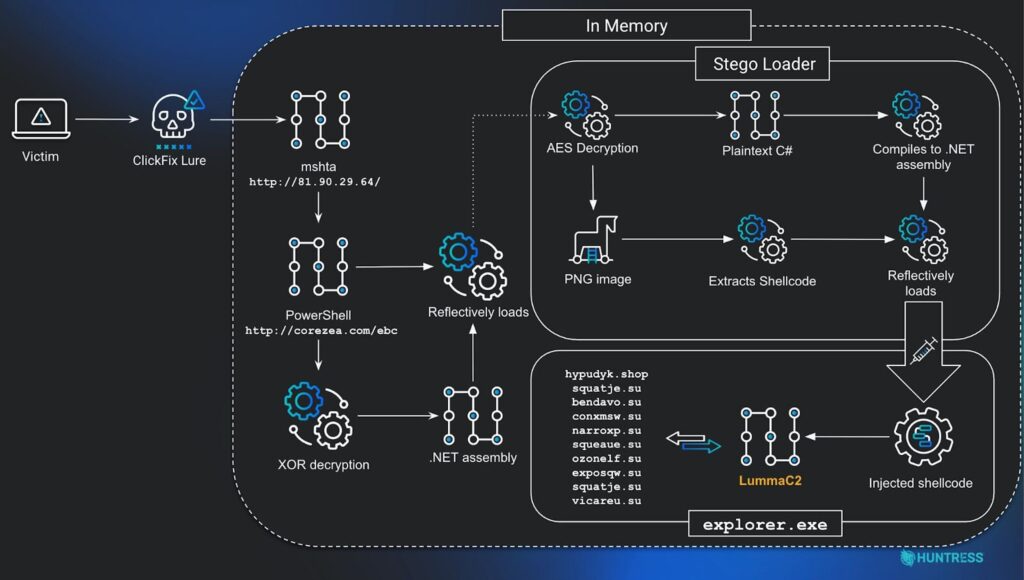
One domain used in both investigations, “securitysettings[.]live,” ties the two clusters together. Acronis also confirmed that several stages of the attack are hosted on domains pointing to the same malicious IP address, strengthening the connection.
Defensive Measures and Mitigation Strategies
ClickFix attacks are dangerous because they rely on users unknowingly helping attackers bypass security controls by running privileged commands. To reduce exposure, organizations should:
• train employees to recognize fake update screens and phishing lures
• block or restrict Windows Run dialog access through Group Policy
• monitor for suspicious mshta.exe and PowerShell activity
• implement browser filtering to reduce exposure to malvertising
• enforce strong endpoint protections and script control policies
These campaigns demonstrate a growing trend in which attackers combine social engineering with system level abuse to deploy large numbers of credential and data stealing malware families. The JackFix operation highlights that fake update screens remain one of the most effective tricks for gaining instant access to a victim’s machine.