A newly advertised Android malware called Albiriox has surfaced as a powerful malware as a service [MaaS] platform, offering attackers a broad toolkit designed for on device fraud, remote interaction, and advanced screen manipulation. Security analysts report that Albiriox is rapidly gaining traction within cybercrime forums because of its extensive capabilities and its ability to bypass traditional mobile defenses.
Albiriox Distributed Through Social Engineering Lures
Researchers from Cleafy noted that Albiriox is distributed through deceptive dropper applications that are pushed using social engineering tactics. These droppers use packing techniques to bypass static security checks before installing the main payload. The embedded malware contains a hard coded list of more than 400 targeted applications, including banking apps, fintech tools, payment processors, cryptocurrency exchanges, digital wallets, and trading platforms.
Albiriox was initially promoted in a closed recruitment phase in late September 2025, later transitioning into a public MaaS offering. Forum activity, language patterns, and related infrastructure suggest that the operators are Russian speaking.
Customers who purchase access receive a custom builder that integrates with a third party crypting service called Golden Crypt, reportedly used to evade antivirus and mobile security products.
Targeting Austrian Users Through Fake App Stores
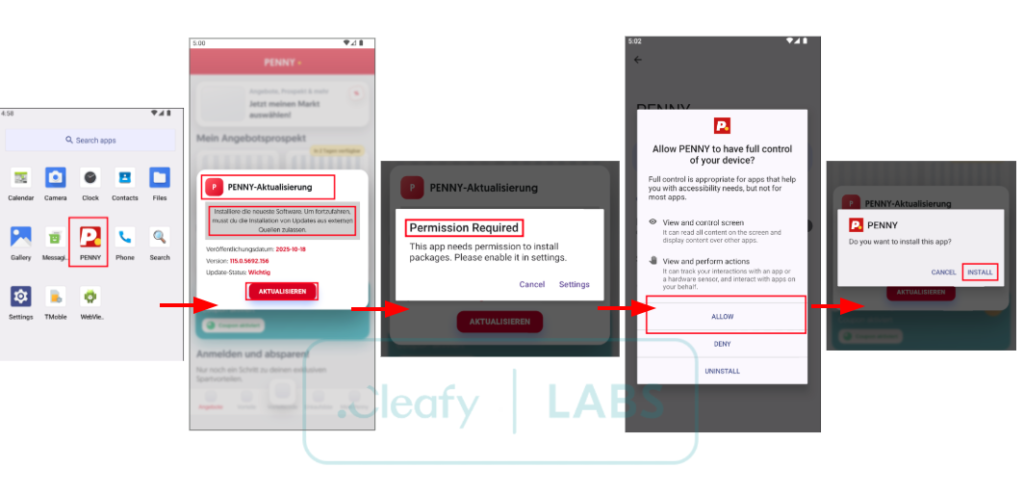
One observed campaign targeted Austrian victims by using German language SMS messages that directed users to imitation Google Play Store pages. These landing pages displayed fake listings for apps such as PENNY Angebote and Coupons. After clicking the Install button, users unknowingly downloaded a dropper APK that pretended to be a software update and requested installation permissions to deploy the main malware.
Once active, Albiriox establishes an unencrypted TCP socket for command and control [C2], enabling attackers to issue commands, operate the device using a Virtual Network Computing [VNC] module, extract sensitive data, display blank or black screens, and adjust volume levels to avoid detection.
Bypassing FLAG_SECURE Using Accessibility Features
One version of the VNC module takes advantage of Android accessibility services to capture all user interface elements on the screen. According to analysts, this method allows Albiriox to bypass the restrictions applied by FLAG_SECURE, a protection commonly used by banking and cryptocurrency applications to block screen recording or screenshots.
Because the malware uses accessibility based streaming rather than direct display capture, it gains complete visibility over sensitive screens without alerting security controls.
Overlays and Credential Theft
Similar to many Android banking trojans, Albiriox supports overlay attacks designed to steal credentials. It can also display fake system update screens or black screens to hide malicious operations and prevent user suspicion.
Cleafy also identified a modified distribution technique. Instead of directing users to fake Google Play pages, certain campaigns redirect victims to a fraudulent PENNY themed website that asks for their phone number. The number is then used to send a download link via WhatsApp, and all submitted numbers are sent to a Telegram bot.

Advanced On Device Fraud Capabilities
Albiriox demonstrates characteristics common to modern on device fraud malware. These include VNC based remote control, automation through accessibility services, targeted overlays, and dynamic credential harvesting. These features allow attackers to conduct fraudulent actions inside legitimate user sessions, making traditional fraud detection systems ineffective.
Emergence of RadzaRat MaaS
The rise of Albiriox coincides with another Android MaaS tool called RadzaRat, which impersonates a legitimate file management app. Once installed, RadzaRat activates extensive surveillance and remote control functions. The malware was first advertised on a cybercrime forum on November 8, 2025.
Certo researcher Sophia Taylor noted that RadzaRat is marketed as a highly accessible tool requiring minimal technical expertise. It gives attackers the ability to search directories, browse files, download data, log keystrokes via accessibility services, and rely on Telegram for C2 communication.
RadzaRat maintains persistence using BOOT_COMPLETED permissions and a dedicated BootReceiver component. It also requests permission to bypass battery optimization restrictions to ensure uninterrupted background activity.
BTMOB and Multi Stage Attack Networks
Researchers have also observed fake Google Play pages promoting an app named GPT Trade [package name com.jxtfkrsl.bjtgsb]. These pages distributed the BTMOB malware and a persistence component called UASecurity Miner. BTMOB was previously documented by Cyble in February 2025 and is known for unlocking devices, logging keystrokes, performing injection based credential theft, and enabling remote access.
In addition, an Android malware distribution network has been seen using adult content lures to push heavily obfuscated malicious APK files. These payloads request sensitive permissions such as screen capture, manipulation of the file system, installation of additional malware, and phishing overlays.
Researchers at Palo Alto Networks Unit 42 reported that the operation uses a resilient multi stage design. The fake lure sites employ commercial grade obfuscation and encryption and connect dynamically to a separate backend infrastructure. The loading mechanism includes deceptive progress screens and timing checks, such as measuring how long it takes to load a test image, to evade analysis.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


