A severe security vulnerability affecting the King Addons for Elementor WordPress plugin is currently under active exploitation. The flaw, tracked as CVE-2025-8489 with a CVSS score of 9.8, allows unauthenticated attackers to escalate their privileges by registering directly as administrators.
The issue impacts all plugin versions from 24.12.92 up to 51.1.14. The maintainers issued a fix in version 51.1.35, released on September 25, 2025. Security researcher Peter Thaleikis identified and reported the flaw. The plugin is installed on more than 10,000 active sites.
According to Wordfence, the problem stems from the plugin’s failure to restrict which user roles can be assigned during registration. As a result, attackers can submit a registration request that assigns themselves the administrator role.
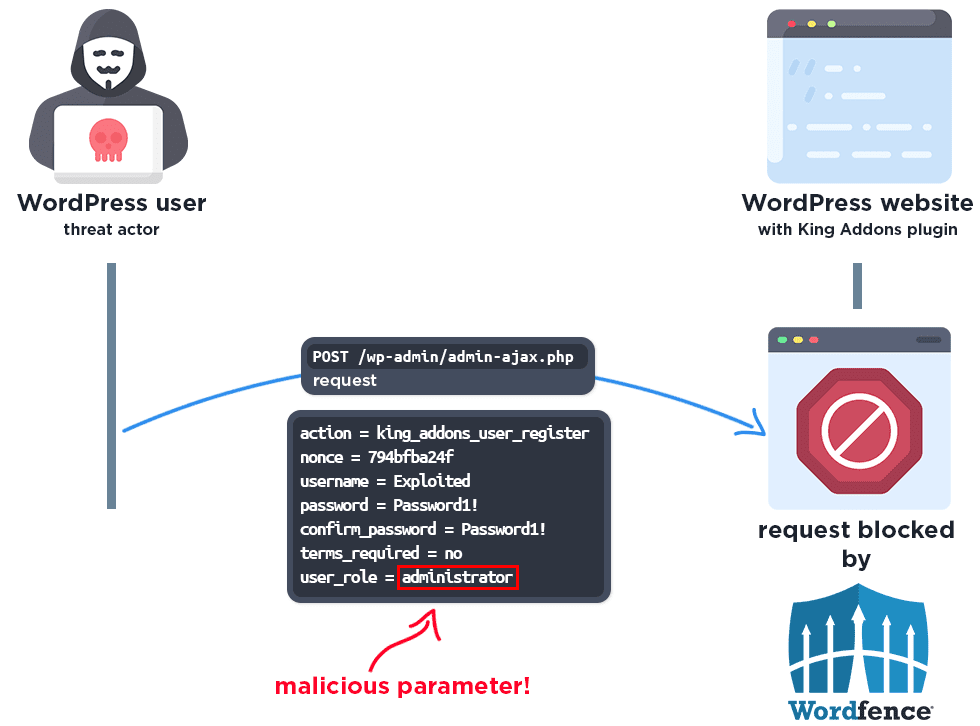
The vulnerability resides in the handle_register_ajax() function. Because of improper validation, attackers can craft a malicious HTTP request to the wp admin admin ajax php endpoint and specify their role as administrator, giving them full control over the targeted site.
Once exploited, attackers can take over the site, upload malicious files, inject harmful redirects, spread malware, or deliver spam through the compromised environment.
Wordfence reported blocking more than 48,400 exploit attempts since the vulnerability became public in late October 2025. Within the most recent 24 hour period, 75 attempts were intercepted. The attacks were traced to the following IP addresses:
45.61.157.120
182.8.226.228
138.199.21.230
206.238.221.25
2602:fa59:3:424::1
Wordfence noted that attackers may have begun probing this flaw as early as October 31, 2025, with large scale exploitation beginning on November 9, 2025.
Administrators are strongly advised to update the plugin to the latest version, review their user accounts for any unauthorized admin profiles, and monitor their systems for unusual activity.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


