A new campaign linked to the threat actor Silver Fox is targeting Chinese speaking users through a deceptive installer that pretends to be Microsoft Teams. The operation appears to be a false flag attempt designed to resemble activity from a Russian group, although the final payload is ValleyRAT, a malware family associated with Chinese cybercrime operations.
Security analysts report that the campaign has been active since November 2025 and relies on SEO poisoning to push users toward harmful download links. According to Hayden Evans from ReliaQuest, who shared the findings with The Hacker News, the attackers have modified the ValleyRAT loader by adding Cyrillic elements, possibly to confuse investigators and divert attribution.
ValleyRAT, which stems from the Gh0st RAT family, offers extensive control to attackers. It allows them to take over infected systems, steal sensitive information, run commands remotely, and maintain long term access inside compromised networks. Gh0st RAT itself is widely linked to Chinese threat groups, which adds further complexity to attribution.
Unlike earlier operations that used fake versions of Google Chrome, Telegram, WPS Office, or DeepSeek, this campaign uses a fake Microsoft Teams page created through SEO techniques. Victims who access the site are directed to download a ZIP archive named MSTчamsSetup.zip from an Alibaba Cloud link. Russian language elements inside the archive appear to be part of the false flag strategy.
Once extracted, the included Setup.exe acts as a trojanized Microsoft Teams installer. It checks for security tools such as 360 Total Security, modifies Microsoft Defender exclusions, and writes a tampered installer file named Verifier.exe into the AppData Local directory before executing it.
The malware then writes several files including Profiler.json, GPUCache2.xml, GPUCache.xml, and AutoRecoverDat.dll to AppData locations. After loading data from these files, the malware injects a malicious DLL into rundll32.exe, which helps the attack blend in with normal Windows processes. In the final stage, it connects to a command server and retrieves the remote control payload.
ReliaQuest notes that Silver Fox appears to be pursuing financial motives such as scams, theft, and fraud, while also collecting sensitive intelligence. Targets face immediate dangers including data theft, financial damage, and compromised systems. The false flag design additionally gives the actor plausible deniability.
The report also aligns with new findings from Nextron Systems that describe a different ValleyRAT delivery method. In that case, attackers use a trojanized Telegram installer, followed by multiple stages that include dropping a vulnerable driver called NSecKrnl64.sys. This technique, known as Bring Your Own Vulnerable Driver (BYOVD), helps bypass security tools.
Security researcher Maurice Fielenbach states that the installer sets dangerous Microsoft Defender exclusions, drops a password protected archive and a renamed 7 Zip binary, then extracts the second stage called men.exe. This binary places additional components inside the public user directory, changes file permissions to resist removal, and creates persistence through a scheduled task that runs an encoded VBE script.
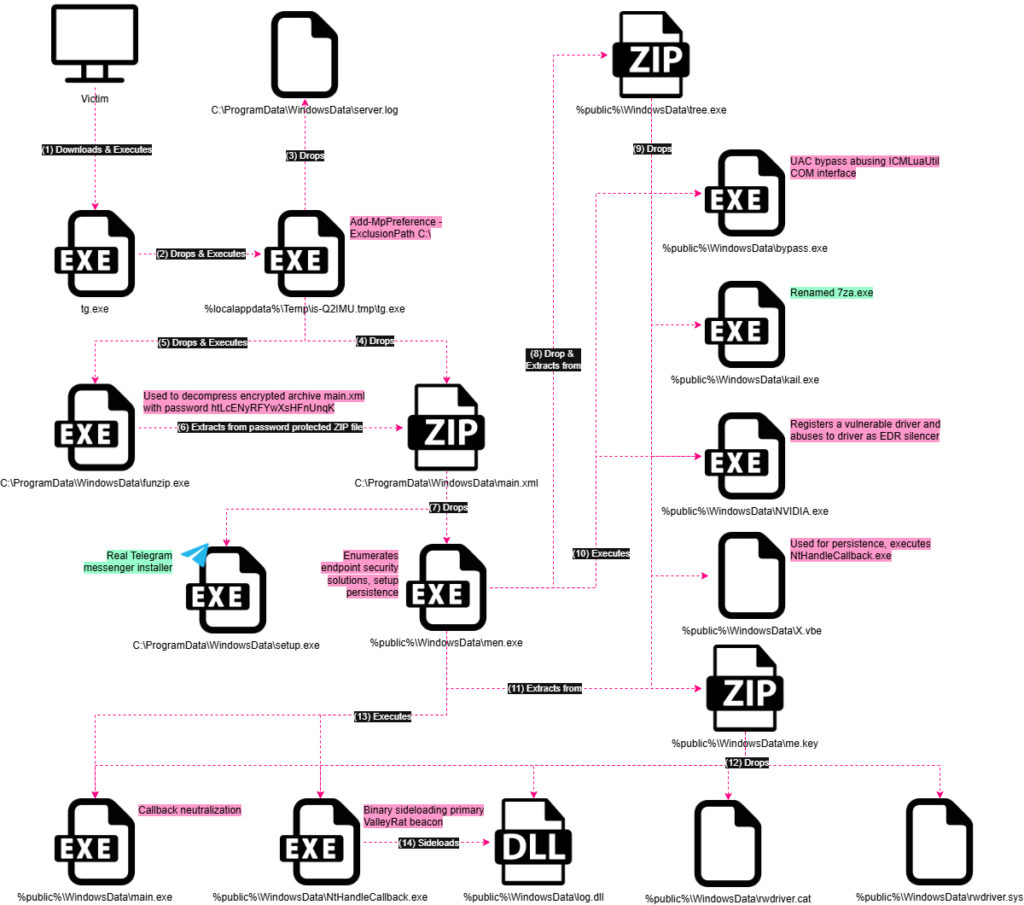
The orchestrator also identifies running security processes, loads the vulnerable NSecKrnl64.sys driver using a file named NVIDIA.exe, and executes ValleyRAT. One of the dropped components, bypass.exe, enables the actor to escalate privileges by bypassing User Account Control.
According to analysts, the victims see what appears to be a normal setup window. In the background, however, the malware silently deploys drivers, modifies system defenses, prepares hidden files, and activates a ValleyRAT beacon that maintains long term access.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


