A human rights lawyer in Pakistan’s Balochistan province received a suspicious WhatsApp link from an unknown sender, marking the first known case of a civil society member in Pakistan being targeted by Intellexa’s Predator spyware, according to Amnesty International.
The link, Amnesty noted, is consistent with a “Predator attack attempt,” based on the technical behavior of the infection server and characteristics of previously documented one-click Predator links. Pakistani authorities have denied the claims, stating there is “not an iota of truth in it.”
The revelations come from a joint investigation with Israeli newspaper Haaretz, Greek news outlet Inside Story, and Swiss tech site Inside IT, based on leaked Intellexa documents, sales and marketing materials, and internal training videos.
Predator Spyware and Its Variants
Intellexa produces Predator, a mercenary spyware tool similar to NSO Group’s Pegasus, capable of extracting sensitive data from Android and iOS devices without the user’s knowledge. Leaked documents indicate Predator has also been marketed under the names Helios, Nova, Green Arrow, and Red Arrow.
Predator typically uses messaging platforms to deliver malicious links, exploiting undisclosed vulnerabilities to infect devices via zero-click or one-click methods. Clicking the link triggers browser exploits in Google Chrome (Android) or Apple Safari (iOS), installing the spyware payload.
Exploited Zero-Day Vulnerabilities
Google Threat Intelligence Group (GTIG) linked Intellexa to multiple zero-day vulnerabilities, including:
- CVE-2025-48543 – Use-after-free in Android Runtime (Google)
- CVE-2025-6554 – Type confusion in V8 (Google Chrome)
- CVE-2023-41993 – WebKit JIT RCE (Apple Safari)
- CVE-2023-41992 – Kernel IPC Use-After-Free (Apple)
- CVE-2023-41991 – Certificate validation bypass in Security framework (Apple)
- CVE-2024-4610 – Use-after-free in Bifrost and Valhall GPU Kernel Driver (Arm)
- CVE-2023-4762 – Type confusion in V8 (Google Chrome)
- CVE-2023-3079 – Type confusion in V8 (Google Chrome)
- CVE-2023-2136 – Integer overflow in Skia (Google Chrome)
- CVE-2023-2033 – Use-after-free in V8 (Google Chrome)
- CVE-2021-38003 – Inappropriate implementation in V8 (Google Chrome)
- CVE-2021-38000 – Insufficient validation of untrusted input in Intents (Google Chrome)
- CVE-2021-37976 – Information leak in memory_instrumentation (Google Chrome)
- CVE-2021-37973 – Use-after-free in Portals (Google Chrome)
- CVE-2021-1048 – Use-after-free in Android Kernel (Google)
An iOS exploit chain using CVE-2023-41993 and JSKit framework was previously deployed in Egypt, and similar techniques appeared in Russian-backed watering hole attacks on Mongolian government websites.

JSKit Framework Capabilities
Google explained that JSKit supports a wide range of iOS versions and can bypass Pointer Authentication Codes (PAC) to execute code directly in memory, allowing Mach-O binaries to be mapped and run without touching the file system.

Exploitation progresses in stages. After CVE-2023-41993 is triggered, the attack breaks out of the Safari sandbox and executes a third-stage payload called PREYHUNTER, leveraging CVE-2023-41991 and CVE-2023-41992. PREYHUNTER has two modules:
- Watcher: Monitors crashes and suspicious behavior, halting exploitation if detected
- Helper: Deploys hooks to record VoIP calls, keylog, and take photos
Intellexa also uses custom frameworks to exploit V8 flaws in Chrome, such as CVE-2021-38003, CVE-2023-2033, CVE-2023-3079, CVE-2023-4762, and CVE-2025-6554, with the latter observed in Saudi Arabia in June 2025.
Data Collection and Surveillance Features
Once installed, Predator gathers data from messaging apps, calls, emails, device locations, screenshots, passwords, and other sensitive information. It can also activate microphones and cameras silently, sending all data to servers in the customer’s country.
Intellexa and several executives were sanctioned by the U.S. for undermining civil liberties. Despite this, Recorded Future’s Insikt Group detected Predator activity in over a dozen countries, mainly in Africa, signaling rising global demand.
Remote Access Concerns
Reports indicate Intellexa employees could remotely access Predator’s customer surveillance logs, raising questions about human rights compliance. Jurre van Bergen of Amnesty International Security Lab noted that direct involvement in spyware operations could expose companies to liability for misuse and human rights violations.
Delivery Vectors and Malicious Ad Exploits
The investigation also uncovered multiple infection vectors:
- Triton, Thor, Oberon: Tactical methods requiring limited user interaction
- Mars, Jupiter: Network injection attacks needing cooperation from ISPs or mobile operators
- Aladdin: Malicious ad system delivering zero-click infections via crafted advertisements
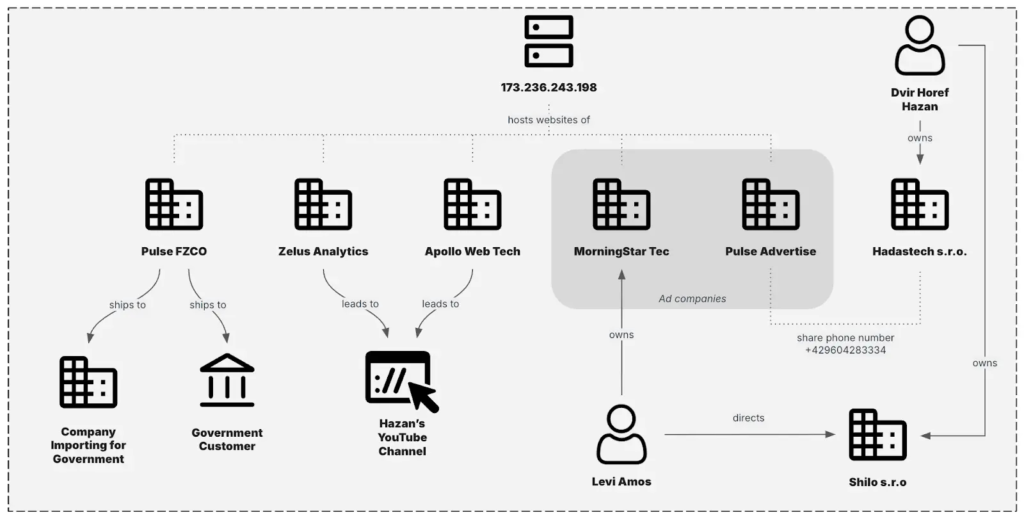
Google confirmed that Aladdin abuses ad networks for user fingerprinting and redirects users to exploit servers. Recorded Future identified companies, Pulse Advertise and MorningStar TEC, likely involved in Aladdin operations. Some Intellexa customers in Saudi Arabia, Kazakhstan, Angola, and Mongolia continue to use Predator’s multi-tiered infrastructure.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


