The United States Cybersecurity and Infrastructure Security Agency (CISA) has officially added a severe security flaw in React Server Components to its Known Exploited Vulnerabilities (KEV) catalog following confirmed exploitation attempts in live environments.
React2Shell Classified as a Maximum Severity Threat
The vulnerability is tracked as CVE-2025-55182 with a CVSS score of 10.0. It involves a remote code execution weakness that an unauthenticated attacker can exploit without any prior configuration. The flaw is widely known as React2Shell.
According to CISA, Meta React Server Components contain a remote code execution issue that arises from a flaw in how payloads for React Server Function endpoints are decoded. This weakness results from insecure deserialization within the Flight protocol. The protocol is responsible for handling communication between the client and server, yet the decoding process makes it possible for attackers to execute arbitrary commands by delivering specially crafted HTTP requests.
Technical expert Martin Zugec from Bitdefender explained that converting text into objects is one of the most dangerous programming categories. He noted that the React2Shell vulnerability exists inside the react server package where object references are improperly parsed during the deserialization process.
Patched Versions Released for Multiple Libraries
The vulnerability has been fixed in versions 19.0.1, 19.1.2, and 19.2.1 across the following libraries:
react server dom webpack
react server dom parcel
react server dom turbopack
A number of frameworks that rely on React Server Components are also affected. These include Next.js, React Router, Waku, Parcel, Vite, and RedwoodSDK.
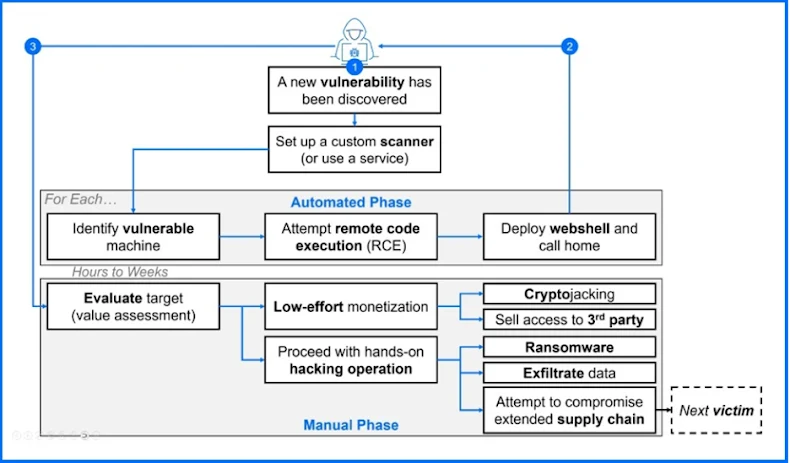
Chinese Linked Groups Spotted Targeting the Flaw
AWS recently reported that multiple threat actors have already attempted to exploit the vulnerability. These attempts originated from infrastructure linked to well known Chinese groups including Earth Lamia and Jackpot Panda. Other cybersecurity firms such as Coalition, Fastly, GreyNoise, VulnCheck, and Wiz have also observed active exploitation attempts.

Some attacks have involved the deployment of cryptocurrency miners. Others used lightweight PowerShell commands to test whether the exploitation attempt succeeded. These were followed by attempts to execute in memory downloaders capable of fetching additional payloads from external servers.
Over Two Million Internet Facing Services Potentially at Risk
Data from Censys indicates that more than 2.15 million exposed services might be vulnerable. These include web services built with React Server Components along with frameworks such as Next.js, Waku, React Router, and RedwoodSDK.
Palo Alto Networks Unit 42 shared findings with The Hacker News showing more than 30 affected organizations across different industries. One activity cluster resembled the behavior of a Chinese linked group known as UNC5174. The attacks involved SNOWLIGHT and VShell.
Unit 42 researcher Justin Moore noted that attackers are scanning for vulnerable systems, performing reconnaissance, attempting to steal AWS configuration files, and deploying downloaders to retrieve payloads from remote command and control servers.
PoC Exploits Released, Urgent Patching Required
Security researcher Lachlan Davidson, who discovered and reported the flaw, has publicly released multiple proof of concept exploits. Another working proof of concept has been published by a researcher from Taiwan using the GitHub ID maple3142.
Federal Civilian Executive Branch agencies are required to apply all necessary updates by December 26, 2025, in accordance with Binding Operational Directive 22 01.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


