Cybersecurity researchers have identified four separate threat clusters using a malware loader called CastleLoader, reinforcing earlier assessments that this tool operates under a malware-as-a-service (MaaS) model, providing capabilities to multiple cybercriminal groups.
The operator behind CastleLoader has been designated GrayBravo by Recorded Future’s Insikt Group, previously tracked as TAG-150.
According to an analysis published by the Mastercard-owned company, GrayBravo “demonstrates rapid development cycles, technical sophistication, responsiveness to public disclosures, and a large, evolving infrastructure.” Key tools in GrayBravo’s arsenal include a remote access trojan named CastleRAT and a malware framework called CastleBot. CastleBot consists of three components: a shellcode stager/downloader, a loader, and a core backdoor.
The CastleBot loader injects the core module, which can communicate with its command-and-control (C2) server to fetch tasks and execute DLL, EXE, and PE (portable executable) payloads. Several malware families are distributed through this framework, including DeerStealer, RedLine Stealer, StealC Stealer, NetSupport RAT, SectopRAT, MonsterV2, WARMCOOKIE, and other loaders such as Hijack Loader.
Recorded Future’s investigation uncovered four operational clusters, each employing unique techniques:
- Cluster 1 (TAG-160): Targets the logistics industry through phishing and ClickFix campaigns to deliver CastleLoader (active since March 2025)
- Cluster 2 (TAG-161): Uses Booking.com-themed ClickFix campaigns to distribute CastleLoader and Matanbuchus 3.0 (active since June 2025)
- Cluster 3: Impersonates Booking.com infrastructure along with ClickFix and Steam Community pages as dead-drop resolvers to deliver CastleRAT via CastleLoader (active since March 2025)
- Cluster 4: Employs malvertising and fake software update lures resembling Zabbix and RVTools to distribute CastleLoader and NetSupport RAT (active since April 2025)
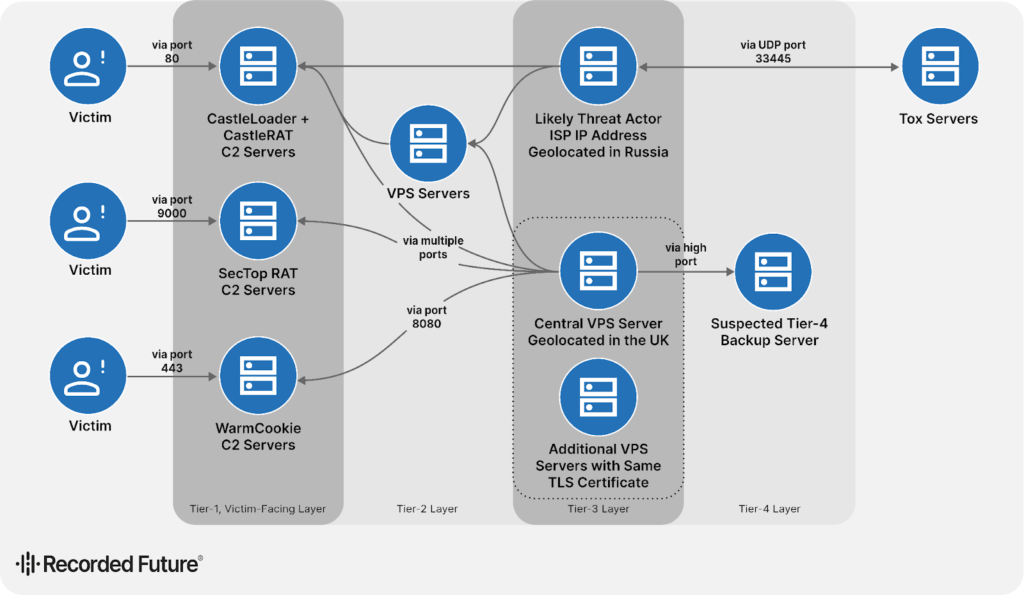
GrayBravo utilizes a multi-tiered infrastructure to support these operations. Tier 1 victim-facing C2 servers are associated with malware families like CastleLoader, CastleRAT, SectopRAT, and WARMCOOKIE, while multiple VPS servers appear to serve as backups.
TAG-160’s campaigns stand out for using fraudulent or compromised accounts on freight-matching platforms such as DAT Freight & Analytics and Loadlink Technologies, increasing the credibility of phishing campaigns. The research highlights GrayBravo’s deep understanding of logistics operations, mimicking legitimate firms, exploiting freight-matching platforms, and mirroring authentic communications to maximize deception.
Low-confidence assessments suggest that this activity may be linked to another unidentified cluster that targeted transportation and logistics companies in North America last year to deliver various malware families.
Recorded Future concluded, “The expansion of GrayBravo’s user base and the growing number of clusters using CastleLoader demonstrates how advanced, adaptive malware can quickly spread within the cybercriminal ecosystem once it proves effective.”
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.