Canadian organizations have become the primary focus of a targeted cyber campaign led by the threat cluster STAC6565. Cybersecurity company Sophos investigated nearly 40 intrusions linked to the group between February 2024 and August 2025, finding strong overlaps with the hacking group Gold Blade, also tracked under names such as Earth Kapre, RedCurl, and Red Wolf.
Active since late 2018, the financially motivated actor initially targeted Russian entities before expanding to Canada, Germany, Norway, Russia, Slovenia, Ukraine, the U.K., and the U.S. Gold Blade historically employed phishing campaigns for commercial espionage but has recently evolved to conduct ransomware attacks using a custom malware called QWCrypt.
A key tool in its arsenal is RedLoader, which collects data from compromised systems and executes PowerShell scripts to extract details about the Active Directory environment. Sophos researcher Morgan Demboski stated, “Almost 80% of STAC6565’s attacks target Canadian organizations, indicating an unusually narrow geographic focus. Gold Blade now operates as a hybrid threat actor, combining data theft with selective ransomware deployment via QWCrypt.”
Other major targets include the U.S., U.K., and Australia, spanning sectors such as services, manufacturing, retail, technology, NGOs, and transportation. The group is believed to operate under a “hack-for-hire” model, performing tailored intrusions for clients while monetizing access via ransomware. Despite speculation of Russian language origins, there is no confirmed link to any state or political agenda.
Sophos described RedCurl as a “professionalized operation,” noting its ability to refine tradecraft and execute discreet extortion attacks. Operational patterns include periods of dormancy followed by sudden surges of attacks using improved methods, suggesting the group uses downtime to refresh its tools.
The STAC6565 attack chain begins with spear-phishing emails targeting HR personnel. Malicious resumes and cover letters are uploaded to legitimate job platforms like Indeed, JazzHR, and ADP WorkforceNow to bypass security measures and increase the likelihood of being opened.
In one incident, a weaponized resume on Indeed redirected victims to a booby-trapped URL, leading to QWCrypt deployment via RedLoader. Observed delivery chains span September 2024, March/April 2025, and July 2025, with previous analysis by Huntress, eSentire, and Bitdefender documenting aspects of these campaigns.
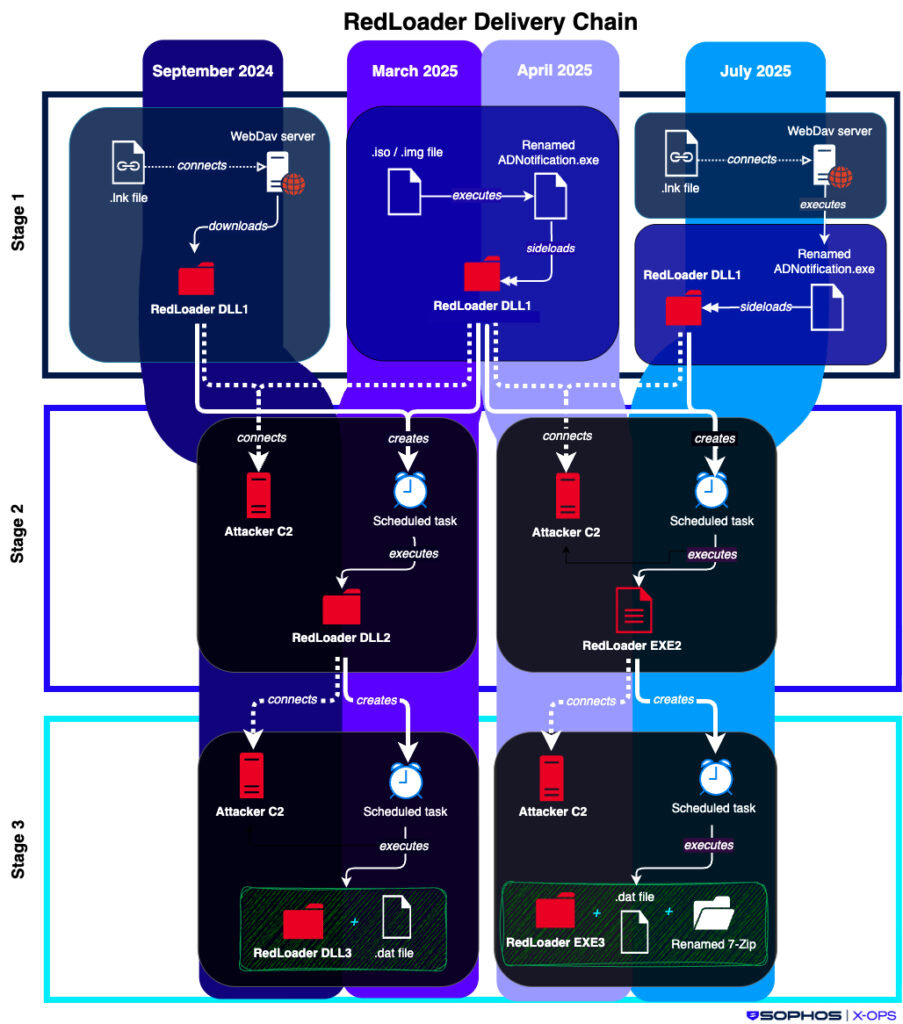
Notably, in July 2025, attackers used ZIP archives containing LNK files disguised as PDFs. These shortcuts leveraged “rundll32.exe” to fetch a renamed executable (“ADNotificationManager.exe”) from a WebDAV server hosted behind Cloudflare Workers. The legitimate Adobe executable then sideloaded the RedLoader DLL (srvcli.dll or netutils.dll), which retrieved and executed subsequent stages, including standalone binaries, malicious DAT files, and renamed 7-Zip archives.
Payloads executed via Microsoft’s Program Compatibility Assistant (“pcalua.exe”) automated system discovery with scripts that unpacked Sysinternals AD Explorer to collect host, disk, process, and antivirus data. The results were encrypted in a password-protected 7-Zip archive and sent to an attacker-controlled WebDAV server. Additional tools included RPivot, Chisel SOCKS5 for C2, and a custom Terminator tool exploiting a signed Zemana AntiMalware driver via BYOVD attacks.
While most attacks were mitigated before QWCrypt installation, three instances in April and July 2025 succeeded in deploying the ransomware. Deployment scripts were tailored to target environments, disabling recovery options and executing ransomware across endpoints, including hypervisors, and running cleanup scripts to remove shadow copies and PowerShell history files.
Sophos emphasized that Gold Blade’s use of recruitment platforms, cycles of dormancy and bursts, and continuous improvement of delivery methods demonstrate operational maturity uncommon among financially motivated actors. Huntress reported a spike in ransomware attacks on hypervisors from 3% in the first half of the year to 25% in the second half, often bypassing traditional endpoint protections using built-in tools like OpenSSL.
Organizations are advised to secure hypervisors by enforcing MFA, strong passwords, isolating management networks, auditing admin access via jump boxes, restricting control plane access, and limiting ESXi interface access to authorized devices.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


