Cybersecurity researchers have revealed a serious exploitation technique affecting enterprise applications built on the .NET ecosystem, enabling attackers to perform arbitrary file writes and potentially achieve remote code execution.
The research was conducted by WatchTowr Labs, which internally named the issue SOAPwn. According to the researchers, the flaw stems from how certain .NET components process SOAP messages and Web Services Description Language imports. The weakness has been observed in products such as Barracuda Service Center RMM, Ivanti Endpoint Manager, and Umbraco 8. Due to the extensive adoption of .NET across enterprise software, the overall impact is expected to be broader.
The findings were publicly presented by Piotr Bazydlo during the Black Hat Europe security conference held in London.
At a technical level, the issue allows attackers to manipulate HTTP client proxies generated within the .NET Framework by abusing attacker controlled WSDL files. When SOAP clients are dynamically created from untrusted WSDL sources, they may incorrectly handle URLs supplied within SOAP requests. This behavior can be exploited to force the application to write data directly to the file system instead of sending it over HTTP.
By supplying a specially crafted file based URL, attackers can redirect SOAP requests to arbitrary file paths. This enables them to overwrite existing files or place malicious payloads in sensitive directories, ultimately leading to code execution within the affected application context.
In a hypothetical attack scenario, a threat actor could provide a Universal Naming Convention path pointing to an external server under their control. This causes the SOAP request to be written to a remote SMB share, allowing the attacker to intercept NTLM authentication challenges and potentially crack or relay the captured credentials.
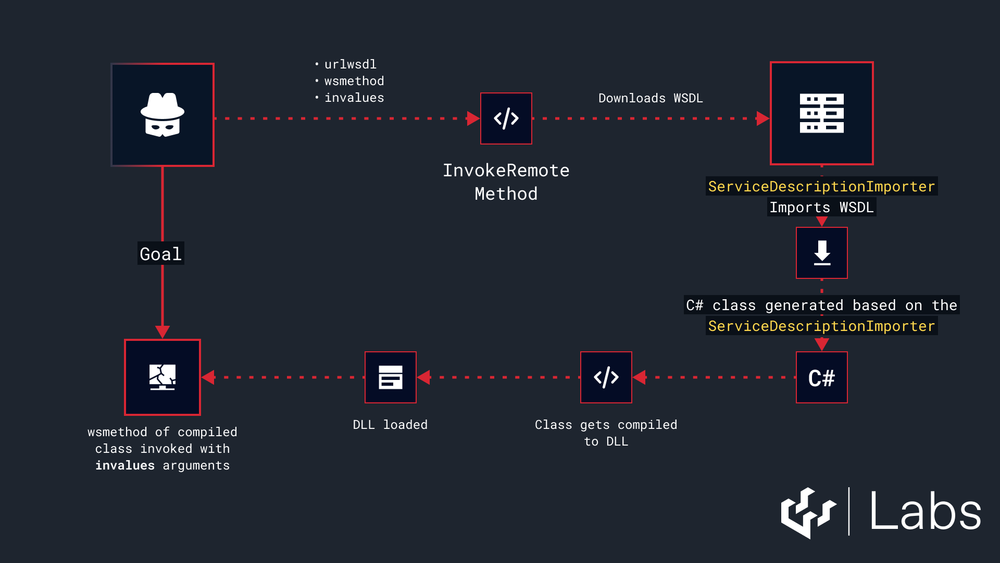
Researchers also identified a more advanced exploitation path involving applications that generate HTTP client proxies using the ServiceDescriptionImporter class. Because this mechanism does not validate the destination URL of the generated proxy, an attacker can supply a malicious WSDL file and gain the ability to drop ASPX web shells, CSHTML payloads, or PowerShell scripts onto the target system, resulting in full remote code execution.
Despite responsible disclosure in March 2024 and again in July 2025, Microsoft declined to release a security fix. The company stated that the behavior originates from application level design choices and emphasized that untrusted input should never be used to generate or execute code.
The issue has since been mitigated in Barracuda Service Center RMM version 2025.1.1 under CVE-2025-34392 with a CVSS score of 9.8, and in Ivanti Endpoint Manager version 2024 SU4 SR1 tracked as CVE-2025-13659 with a CVSS score of 8.8. However, the vulnerability remains unresolved in Umbraco 8, which reached end of life in February 2025.
The research highlights how expected framework behavior, when combined with unsafe design assumptions, can open unexpected attack paths leading to NTLM credential exposure, arbitrary file writes, and remote code execution in enterprise environments.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


