Cybersecurity researchers are warning about a new wave of highly advanced phishing kits that are enabling large scale credential theft by combining automation, artificial intelligence, and multi factor authentication bypass techniques. The newly observed toolkits, known as BlackForce, GhostFrame, InboxPrime AI, and Spiderman, represent a growing shift toward industrialized phishing operations.
BlackForce Targets MFA Using Man in the Browser Techniques
First identified in August 2025, BlackForce is a commercial phishing kit designed to harvest login credentials and intercept one time passwords through Man in the Browser techniques. The toolkit is actively sold on Telegram forums and is under continuous development.
According to researchers from Zscaler ThreatLabz, BlackForce has been used to impersonate more than eleven well known brands, including Disney, Netflix, DHL, and UPS. The kit integrates evasion mechanisms that block security scanners, crawlers, and analysis tools, allowing only real victims to proceed.
The phishing pages rely on dynamically named JavaScript files that force browsers to download fresh malicious code, bypassing cached versions. Once victims enter their credentials, the data is transmitted in real time to attacker controlled Telegram bots and command and control dashboards.
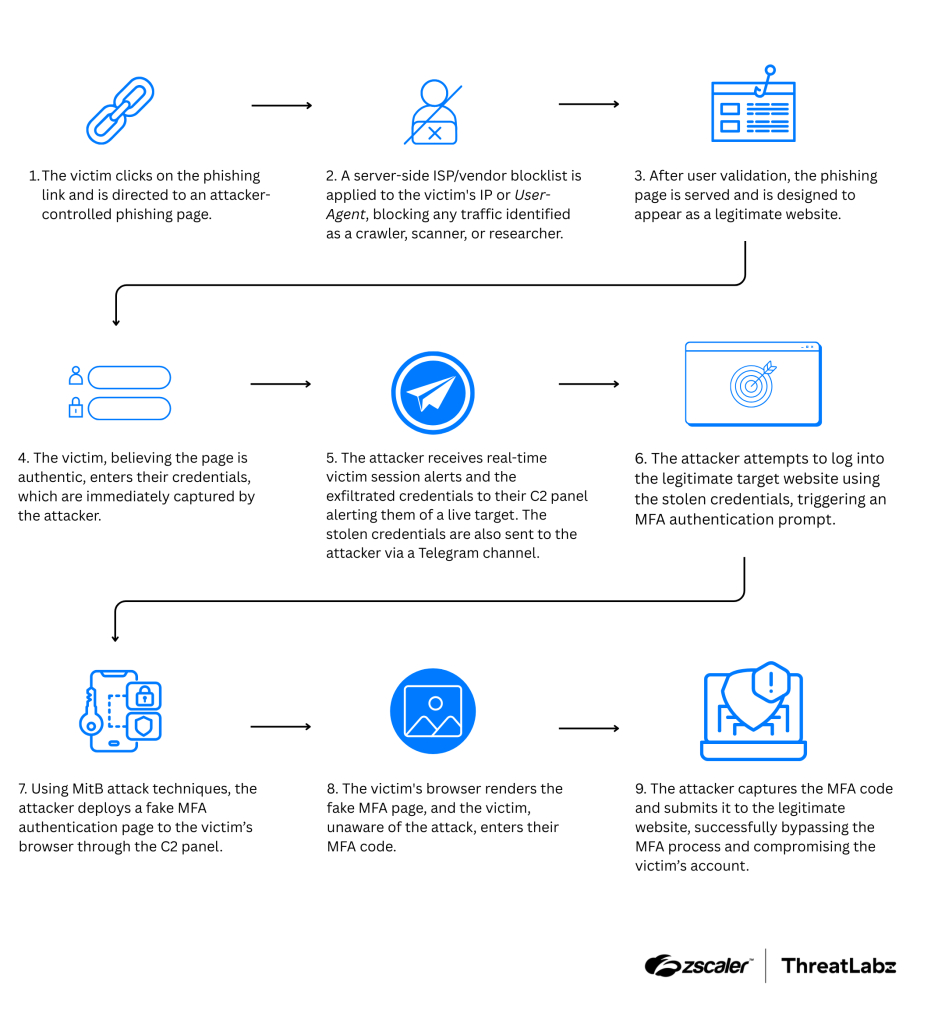
When attackers attempt to access the legitimate service, a real MFA prompt is triggered. At that stage, the kit injects a fake MFA page into the victim’s browser. Any authentication codes entered are captured and immediately reused, after which the victim is silently redirected to the real website to avoid suspicion.
GhostFrame Drives Over One Million Stealth Phishing Attempts
Discovered in September 2025, GhostFrame has quickly gained popularity due to its minimalistic yet flexible design. The kit uses a seemingly benign HTML page that hides malicious activity inside an embedded iframe. This iframe delivers phishing pages targeting Microsoft 365 and Google accounts.
Security researchers at Barracuda note that the iframe architecture allows attackers to swap phishing content, change regions, and evade detection without modifying the visible outer page. Each visit generates a new random subdomain, making blocking efforts significantly harder.
GhostFrame campaigns typically begin with emails referencing invoices, contracts, or password resets. The loader script modifies page titles, favicons, and browser behavior to convincingly mimic trusted services, while anti debugging measures prevent inspection through developer tools.
InboxPrime AI Automates Phishing at Enterprise Scale
InboxPrime AI represents a major leap in phishing automation. Marketed as a malware as a service platform, it uses artificial intelligence to generate and deliver phishing emails that closely resemble legitimate business communication.
Researchers from Abnormal report that the platform mimics human emailing behavior and leverages Gmail’s web interface to bypass traditional spam filters. Users can configure campaign parameters such as industry, tone, language, and email length, allowing the AI engine to generate highly convincing lures.
The dashboard mirrors commercial email marketing tools and includes features such as reusable templates, spintax based message variation, sender identity spoofing, and real time spam diagnostics. This automation significantly lowers the skill barrier for cybercriminals and enables high volume phishing with minimal effort.
Spiderman Focuses on European Banking Fraud
Another emerging toolkit, Spiderman, is specifically designed to target European financial institutions. The kit offers pixel perfect replicas of dozens of banking and payment service portals, including CaixaBank, Commerzbank, Deutsche Bank, ING, Klarna, and PayPal.
According to researchers at Varonis, Spiderman is a full stack phishing framework that allows attackers to manage campaigns, capture credentials, and track sessions in real time. Unlike many other kits, it is marketed through private Signal groups rather than Telegram.
The platform employs geofencing, ISP filtering, and device checks to ensure only intended victims can access phishing pages. It is also capable of stealing OTPs, PhotoTAN codes, credit card details, and cryptocurrency wallet seed phrases, making it particularly effective against European banking security workflows.
Hybrid Salty and Tycoon Attacks Complicate Detection
These four kits join a broader ecosystem of phishing frameworks such as Tycoon 2FA, Salty 2FA, Sneaky 2FA, Whisper 2FA, Cephas, and Astaroth. In a recent analysis, ANY.RUN identified a new hybrid Salty Tycoon campaign that blends components from multiple kits.
The hybrid approach weakens detection rules, complicates attribution, and gives attackers greater flexibility. A single phishing sample may now contain fallback mechanisms that switch execution chains if one infrastructure fails, further challenging defenders.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


