Cybersecurity researchers have uncovered a new malware distribution campaign that abuses GitHub hosted Python repositories to spread a previously undocumented JavaScript based Remote Access Trojan named PyStoreRAT. The operation relies on fake development tools, OSINT utilities, and GPT related projects to trick analysts and developers into executing malicious loader code.
GitHub Repositories Hide Multi Stage Infection Chain
According to research published by Morphisec, the malicious repositories contain only a few lines of code that silently download a remote HTML Application file and execute it using the Windows binary mshta.exe. The findings were shared publicly with The Hacker News.
The PyStoreRAT malware is described as a modular, multi stage implant capable of executing a wide range of payload formats. These include EXE, DLL, PowerShell, MSI, Python, JavaScript, and HTA modules. As part of the attack chain, the malware also deploys an information stealing component known as Rhadamanthys.
Threat actors distribute the malware through Python and JavaScript loader stubs embedded inside GitHub repositories that masquerade as OSINT tools, DeFi bots, GPT wrappers, and security themed utilities. These projects are intentionally designed to appeal to developers, threat researchers, and security professionals.
Social Media Promotion and Fake Popularity Metrics
The earliest traces of this campaign date back to mid June 2025, with a continuous stream of malicious repositories published since then. The tools are promoted aggressively through platforms such as YouTube and X, while repository visibility is artificially boosted by inflating star and fork counts. This technique closely resembles tactics previously observed in the Stargazers Ghost Network.
Attackers rely on either newly created GitHub accounts or accounts that remained inactive for extended periods. Once a repository gains attention and appears in GitHub trending lists, malicious code is quietly introduced through so called maintenance commits during October and November.
In many cases, the advertised tools do not actually function. Some display static menus, while others perform minimal placeholder actions. The goal is to create an illusion of legitimacy and exploit GitHub’s trust model, convincing users to execute the embedded loader that initiates the infection process.
PyStoreRAT Capabilities and Evasion Techniques
Once executed, the loader retrieves a remote HTA payload that delivers PyStoreRAT to the victim system. The malware profiles the host, checks for administrator privileges, and searches for cryptocurrency wallet files linked to Ledger Live, Trezor, Exodus, Atomic, Guarda, and BitBox02.
The loader also collects information about installed antivirus products and looks for indicators related to Falcon, referencing CrowdStrike Falcon, and Reason, linked to Cybereason or ReasonLabs. If such products are detected, execution is routed through cmd.exe to launch mshta.exe, otherwise it proceeds directly.
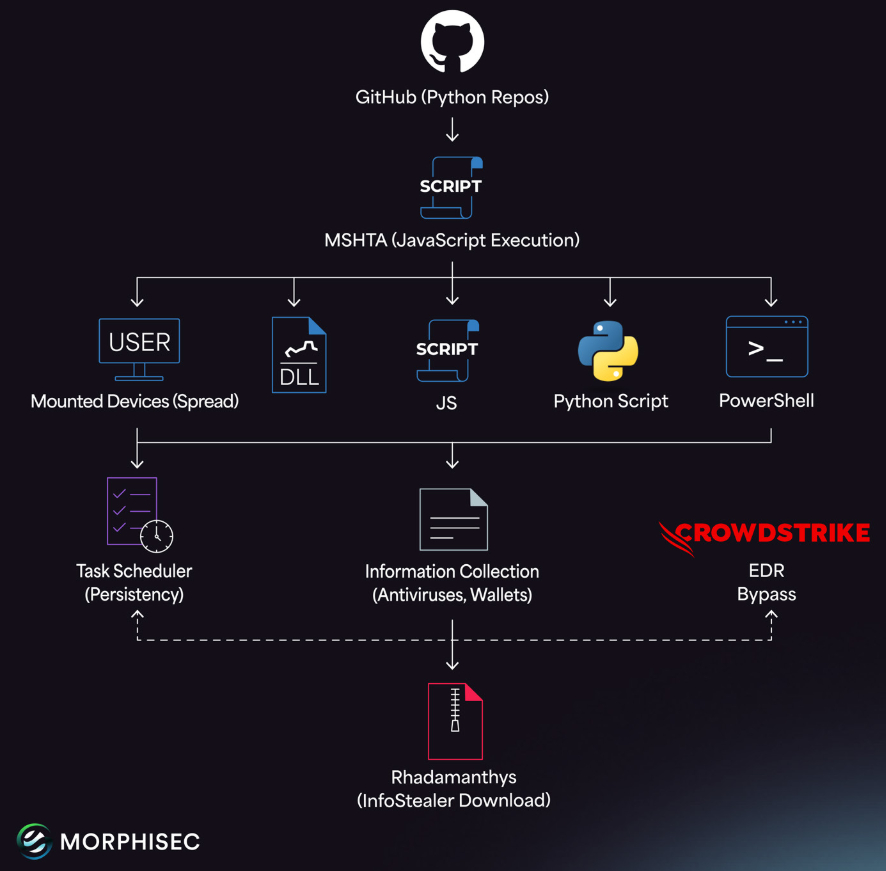
Persistence is established by creating a scheduled task disguised as an NVIDIA application self update. In the final stage, the malware communicates with an external server to receive commands. Supported actions include downloading and executing EXE payloads such as Rhadamanthys, extracting ZIP archives, executing DLL files via rundll32.exe, running JavaScript code in memory, installing MSI packages, spawning additional mshta.exe processes, executing PowerShell commands, spreading via removable drives using malicious shortcut files, and removing scheduled tasks to erase forensic evidence.
While the operators behind the campaign remain unidentified, researchers note the presence of Russian language artifacts and coding patterns, suggesting a likely Eastern European origin.
SetcodeRat Campaign Targets Chinese Speaking Regions
In a related disclosure, Chinese security vendor QiAnXin reported the emergence of another remote access trojan known as SetcodeRat. The malware has reportedly been spreading across China since October 2025 through malvertising campaigns, infecting hundreds of systems belonging to government bodies and enterprises within a single month.
The malicious installers are disguised as legitimate software packages, including Google Chrome. The malware verifies the victim’s system language and exits immediately if it does not match Chinese speaking regions such as Mainland China, Hong Kong, Macao, or Taiwan. It also terminates execution if it cannot reach a specific Bilibili API endpoint.
In subsequent stages, the malware uses an executable named pnm2png.exe to sideload a malicious zlib1.dll file, which decrypts and runs an embedded RAT payload. SetcodeRat is capable of connecting either to Telegram based infrastructure or traditional command and control servers, enabling screenshot capture, keystroke logging, file access, process execution, command shell access, network profiling, and self updates.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


