Cybersecurity researchers have revealed multiple serious security flaws in the open source PBX platform FreePBX, including issues that could allow attackers to bypass authentication and achieve remote code execution under specific configurations.
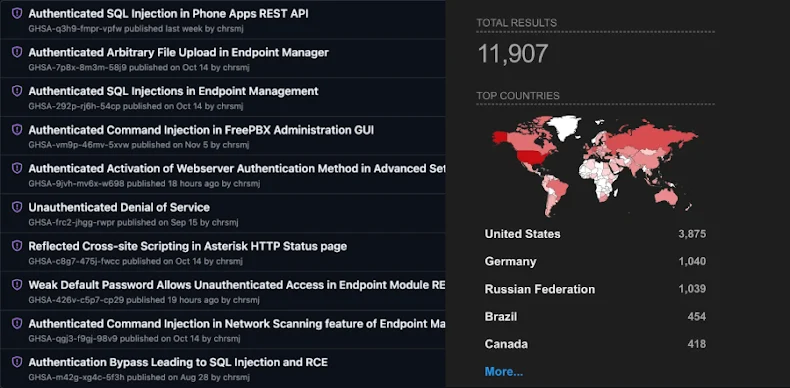
The vulnerabilities were identified by researchers at Horizon3.ai and responsibly disclosed to the FreePBX maintainers on September 15, 2025. According to the findings, the weaknesses span SQL injection, arbitrary file upload, and an authentication bypass tied to a specific authorization setting.
Details of the Disclosed Vulnerabilities
The reported flaws include the following:
- CVE-2025-61675 (CVSS 8.6)
Multiple authenticated SQL injection vulnerabilities affecting several endpoints, including basestation, model, firmware, and custom extension. These flaws allow attackers with valid access to read from and write to the backend SQL database. - CVE-2025-61678 (CVSS 8.6)
An authenticated arbitrary file upload issue that enables attackers to upload malicious PHP files through the firmware upload functionality. Once uploaded, these files can be executed to leak sensitive system data such as/etc/passwd. - CVE-2025-66039 (CVSS 9.3)
A critical authentication bypass vulnerability that occurs when the Authorization Type setting, also known as AUTHTYPE, is configured aswebserver. In this scenario, attackers can forge an Authorization header and gain access to the Administrator Control Panel without valid credentials.
It is important to note that the authentication bypass does not affect default installations. The risk emerges only when several advanced configuration options are manually enabled, exposing legacy authentication logic.
Once exploited, attackers could insert malicious users into the system database, achieving effects similar to a previously exploited FreePBX flaw disclosed earlier in 2025.
In a technical analysis published last week, Noah King from Horizon3.ai stated that these vulnerabilities are straightforward to exploit and can be chained together to gain full remote code execution on affected systems.
Patches and Mitigations
The FreePBX project has released updates addressing these flaws in the following versions:
- CVE-2025-61675 and CVE-2025-61678 fixed in versions 16.0.92 and 17.0.6, released on October 14, 2025
- CVE-2025-66039 fixed in versions 16.0.44 and 17.0.23, released on December 9, 2025
Additionally, the option to select the authentication provider has been removed from the web interface. Administrators must now configure it manually via the command line using fwconsole.
As a temporary mitigation, users are advised to switch the Authorization Type to usermanager, disable Override Readonly Settings, apply the configuration, and reboot the system. Administrators who previously enabled the webserver option are strongly encouraged to perform a full compromise assessment.
FreePBX now displays a warning in the dashboard, cautioning that the webserver authorization method offers reduced security and should be avoided.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


