A large scale cryptocurrency mining campaign has been detected targeting cloud environments by abusing compromised Identity and Access Management credentials within Amazon Web Services. The operation leverages stolen IAM permissions to rapidly deploy crypto mining infrastructure across multiple AWS services.
The activity was first identified on November 2, 2025, through automated threat detection systems operated by Amazon, including its managed security service GuardDuty. According to a newly released report, the attackers employed previously unseen persistence mechanisms designed to obstruct incident response and maintain uninterrupted mining operations.
Investigators observed that the threat actor operated from external hosting providers and immediately enumerated available cloud resources after gaining access. Within minutes, the attacker assessed permissions and launched cryptocurrency mining workloads across Elastic Container Service (ECS) and Elastic Compute Cloud (EC2). In many cases, mining operations became active within ten minutes of the initial compromise.
The multi stage intrusion begins with the use of compromised IAM credentials that possess administrative level privileges. During the discovery phase, the attacker evaluates EC2 service quotas and validates permissions by invoking the RunInstances API with the DryRun flag enabled. This tactic allows permission testing without deploying actual instances, avoiding costs and significantly reducing forensic artifacts.
Once the environment is deemed suitable, the attacker creates service linked IAM roles for autoscaling groups and AWS Lambda by invoking CreateServiceLinkedRole and CreateRole. The AWSLambdaBasicExecutionRole policy is then attached, allowing execution of malicious Lambda functions.
In several confirmed incidents, the attacker deployed dozens of ECS clusters, sometimes exceeding 50 clusters within a single compromised account. Each cluster was configured using a malicious Docker image previously hosted on DockerHub, which initiated crypto mining workloads on ECS Fargate nodes using the RandomVIREL mining algorithm. Although the image has since been removed, its impact remains evident.
The campaign also aggressively abused EC2 autoscaling groups, configuring them to scale between 20 and 999 instances. This approach maximized resource consumption by exploiting service quotas and targeted high performance GPU, machine learning, compute optimized, memory optimized, and general purpose EC2 instances.
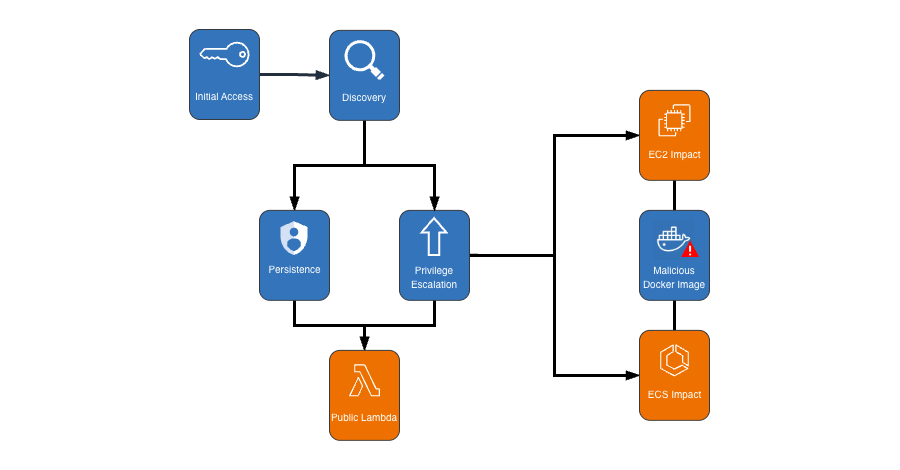
What distinguishes this operation is the use of the ModifyInstanceAttribute action with the disableApiTermination parameter set to True. This prevents instances from being terminated through the console, CLI, or API, forcing victims to manually re enable termination before remediation. Security analysts noted that this technique deliberately delays response efforts and prolongs mining activity.
Similar risks tied to ModifyInstanceAttribute were previously highlighted in April 2024 when security researcher Harsha Koushik demonstrated how the action could be abused to exfiltrate instance credentials and potentially compromise entire AWS accounts.
Additionally, the attackers created publicly invokable Lambda functions and introduced a new IAM user named user-x1x2x3x4. This user was assigned the AmazonSESFullAccess policy, granting unrestricted access to Amazon Simple Email Service and likely enabling phishing campaigns.
To mitigate the threat, AWS customers are advised to enforce strong IAM controls, replace long term access keys with temporary credentials, enable multi factor authentication for all users, apply least privilege principles, scan container images for malicious activity, monitor abnormal CPU allocation in ECS tasks, log events using CloudTrail, and ensure GuardDuty remains enabled for automated detection and response.
Security teams warn that the attacker’s coordinated use of multiple AWS compute services combined with advanced persistence techniques signals a significant evolution in cloud focused crypto mining attacks.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


