Cybersecurity researchers are warning about a rapidly evolving Android malware ecosystem where threat actors are combining malicious droppers, SMS stealing functions, and full remote access capabilities to target users at scale. Recent investigations show that users in Uzbekistan are being actively targeted through fake applications that silently deploy advanced malware once installed.
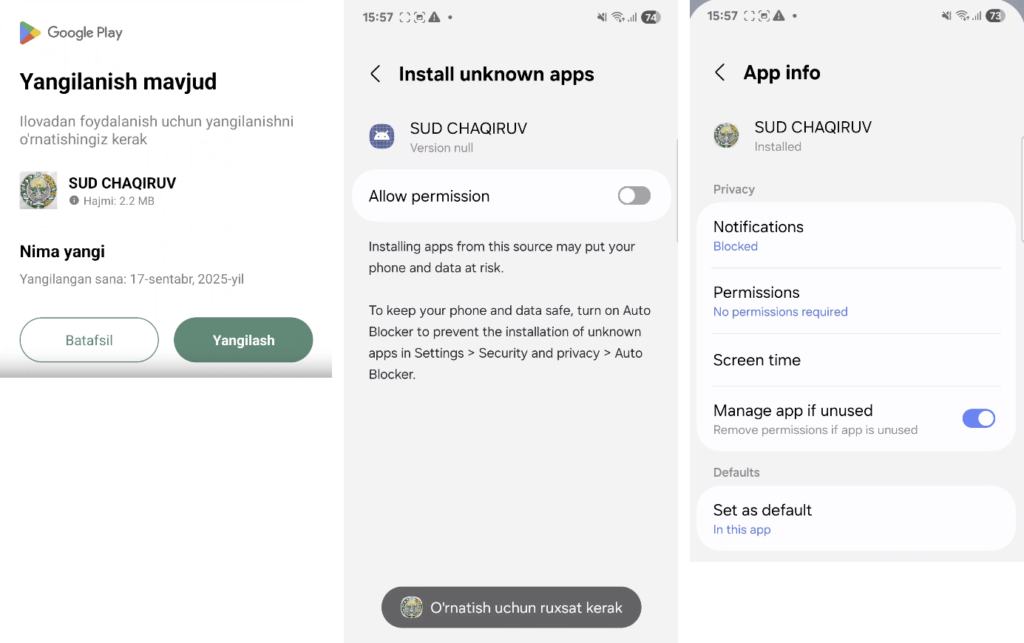
According to an analysis published by Group-IB, attackers have shifted away from distributing obvious malicious APK files. Instead, they now rely on dropper applications that appear legitimate but contain encrypted malicious payloads. These payloads are deployed locally after installation, even when the device is offline, making detection significantly harder.
The primary malware involved in this campaign is known as Wonderland, previously tracked as WretchedCat. The Android threat enables real time bidirectional command and control communication, allowing attackers to issue commands instantly. Its capabilities include SMS theft, execution of arbitrary USSD requests, and impersonation of trusted apps such as Google Play, along with disguises like video files, photos, or digital wedding invitations.
Financially Motivated Operations and Telegram Coordination
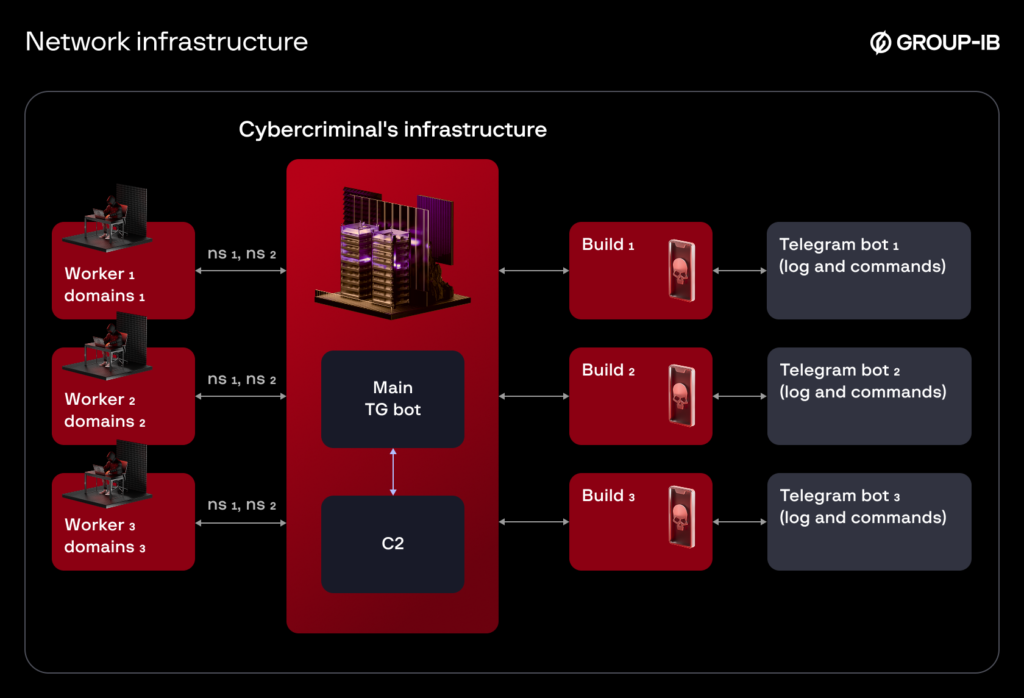
Group-IB attributes the campaign to a financially driven threat actor known as TrickyWonders. The group heavily relies on Telegram to coordinate operations, manage infrastructure, and distribute malware. First identified in November 2023, the operation also uses two known dropper families designed to hide Wonderland’s encrypted payload, MidnightDat first seen in August 2025, and RoundRift first observed in October 2025.
Distribution methods include fake Google Play Store web pages, advertising campaigns on Facebook, fraudulent dating app profiles, and direct messaging through Telegram. In many cases, attackers abuse stolen Telegram sessions belonging to Uzbek users, which are purchased from dark web marketplaces, to send malicious APK files directly to victims’ contacts.
Once installed, the malware intercepts SMS messages and one time passwords, enabling attackers to drain funds from victims’ bank cards. Additional features include harvesting contact lists, hiding security notifications, suppressing OTP alerts, and sending SMS messages to spread laterally.
To initiate infection, victims are manipulated into enabling installation from unknown sources. This is achieved through fake update prompts instructing users to install an update in order to access the app’s features.
Group-IB noted that when permissions are granted, attackers attempt to hijack the victim’s phone number and gain access to the associated Telegram account. If successful, the compromised account is then used to further propagate the malware, creating a continuous infection loop.
Advanced Obfuscation and Resilient Infrastructure
Wonderland reflects a broader evolution in Android malware targeting Uzbekistan. Earlier threats such as Ajina.Banker relied on mass spam campaigns, while newer families like Qwizzserial used basic disguise techniques. In contrast, Wonderland employs heavy obfuscation, anti analysis mechanisms, and dropper based delivery to evade security checks.
The malware’s bidirectional command and control transforms it from a passive SMS stealer into an actively managed remote agent capable of executing commands on demand. Researchers also observed a highly dynamic infrastructure, with command servers rotating domains frequently. Each domain is used only for a limited number of builds, reducing the effectiveness of blacklist based defenses.
Malicious APK files are generated through a dedicated Telegram bot and distributed by individuals referred to as workers, who receive a share of the stolen funds. Each APK build is tied to its own command and control domain, ensuring that takedown efforts do not disrupt the entire operation. The criminal ecosystem also includes developers, group owners, and vbivers who verify stolen card data, highlighting a structured and mature fraud model.
Emergence of New Android Malware Families
The disclosure coincides with the appearance of other advanced Android malware families, including Cellik, Frogblight, and NexusRoute, which demonstrate how mobile cybercrime is becoming increasingly accessible and scalable.
Cellik, advertised on underground forums for subscription based pricing, offers extensive surveillance features such as live screen streaming, keylogging, camera and microphone access, notification interception, credential stealing overlays, and data wiping. A particularly concerning capability is its one click APK builder, which allows attackers to embed the malicious payload inside legitimate Google Play apps.
According to Daniel Kelley of iVerify, attackers can browse the Google Play catalogue and select legitimate apps, which are then repackaged into weaponized APKs with minimal effort.
Frogblight, tracked by Kaspersky, targets users in Turkey through SMS phishing messages posing as court notifications. Once installed, the malware steals banking credentials via WebViews, collects SMS messages, call logs, installed app lists, and file system data. Researchers believe Frogblight is being prepared for distribution under a malware as a service model, based on the discovery of a centralized web control panel.
In India, Android users have been targeted by NexusRoute, a malware campaign that uses phishing sites impersonating government services. These sites redirect victims to malicious APK files hosted on GitHub repositories and GitHub Pages while harvesting personal and financial data.
Security firm CYFIRMA reported that NexusRoute abuses accessibility services and launcher settings to gain persistent control. The malware is capable of SMS interception, SIM profiling, contact theft, call log harvesting, file access, screenshot capture, microphone activation, GPS tracking, and financial credential theft.
Investigators linked the campaign to a broader underground development ecosystem, suggesting a professionally maintained and large scale fraud and surveillance operation. Experts warn that these campaigns demonstrate how Android malware is rapidly advancing in sophistication, automation, and operational scale.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


