Cybersecurity researchers have uncovered a sustained and carefully targeted spear‑phishing operation that abused the npm package ecosystem as a delivery platform for credential theft.
According to findings published by Socket, the campaign involved the upload of 27 malicious npm packages using six different publisher aliases. Rather than infecting systems directly, the attackers repurposed npm package hosting and content delivery networks as resilient phishing infrastructure.
Researchers stated that the campaign primarily targeted sales and commercial employees working at organizations closely linked to critical infrastructure sectors across the United States and allied countries.
“A five‑month operation transformed 27 npm packages into durable hosting for browser‑based phishing lures that impersonate document‑sharing portals and Microsoft sign‑in pages,” Socket researchers Nicholas Anderson and Kirill Boychenko said. The operation targeted 25 organizations across manufacturing, industrial automation, plastics, and healthcare industries.
Identified Malicious npm Packages
The following package names were associated with the phishing campaign:
adril7123
ardril712
arrdril712
androidvoues
assetslush
axerification
erification
erificatsion
errification
eruification
hgfiuythdjfhgff
homiersla
houimlogs22
iuythdjfghgff
iuythdjfhgff
iuythdjfhgffdf
iuythdjfhgffs
iuythdjfhgffyg
jwoiesk11
modules9382
onedrive-verification
sarrdril712
scriptstierium11
secure-docs-app
sync365
ttetrification
vampuleerl
How the Phishing Infrastructure Operated
Unlike traditional malicious packages that require installation, these npm packages were designed to act as hosting containers. They delivered client‑side HTML and JavaScript phishing pages that mimicked secure document‑sharing services.
Victims who interacted with the lures were redirected to Microsoft login pages with their email addresses already prefilled, increasing the likelihood of successful credential theft.
Using npm package CDNs provided attackers with a significant advantage. It allowed them to leverage legitimate infrastructure that is more resistant to takedown efforts. Even when individual packages were removed, attackers could quickly rotate publisher identities and upload new packages with minimal disruption.
Anti‑Analysis and Evasion Techniques
The malicious packages contained multiple client‑side defenses to evade detection. These included bot filtering, sandbox evasion, and checks requiring mouse movement or touch interaction before redirecting victims to attacker‑controlled credential harvesting endpoints.
The JavaScript code was heavily obfuscated or minified to complicate automated inspection. Researchers also identified the use of hidden honeypot form fields that remain invisible to real users but are commonly filled by automated crawlers. This mechanism acted as an additional filter to block security scanners.

Socket noted that domains embedded within the packages overlapped with adversary‑in‑the‑middle phishing infrastructure commonly associated with Evilginx, an open‑source phishing framework.
Relationship to Previous npm Phishing Campaigns
This is not the first instance of npm being abused for phishing operations. In October 2025, Socket disclosed a separate campaign named Beamglea, which involved 175 malicious packages designed for credential harvesting. Researchers assessed the newly identified activity as distinct, despite similarities in operational goals.
“This campaign follows a similar playbook but introduces different delivery mechanics,” Socket explained. Instead of simple redirect scripts, the attackers deployed fully self‑contained phishing workflows that executed directly within the browser.
Targeted Individuals and Geographic Reach
The malicious packages were found to hard‑code 25 specific email addresses, belonging to individuals working in sales, account management, and business development roles. The victims were spread across manufacturing, industrial automation, plastics, polymer supply chains, and healthcare sectors.
Affected regions included Austria, Belgium, Canada, France, Germany, Italy, Portugal, Spain, Sweden, Taiwan, Turkey, the United Kingdom, and the United States.
While the source of the email addresses remains unknown, researchers suspect the attackers gathered the information from public trade show websites such as Interpack and K‑Fair, combined with open‑source intelligence.
In several cases, the targeted individuals were based outside their company headquarters, reinforcing the attackers’ focus on regional commercial teams rather than centralized IT departments.
Defensive Measures and Industry Impact
To mitigate risks from similar threats, security teams are advised to enforce strict dependency verification, monitor unusual CDN requests originating outside development environments, and deploy phishing‑resistant multi‑factor authentication. Organizations should also monitor post‑authentication activity for signs of compromise.
Socket added that the findings coincide with a broader increase in destructive malware across npm, PyPI, NuGet Gallery, and Go module ecosystems. These threats increasingly rely on delayed execution, remote kill switches, and runtime code retrieval using standard utilities like wget and curl.
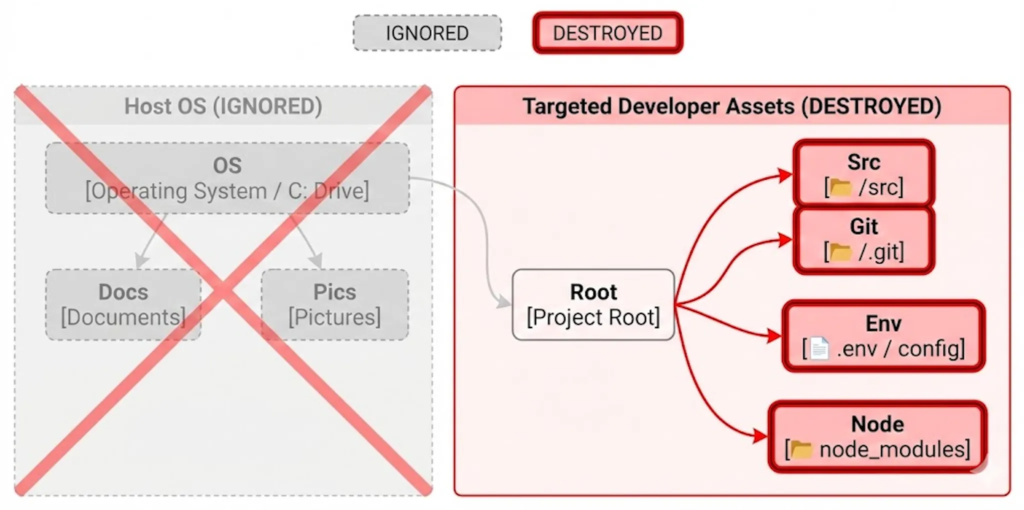
“Instead of mass file destruction, these packages operate with surgical precision,” researcher Kush Pandya said. “They target Git repositories, source directories, configuration files, and CI outputs, often executing automatically through lifecycle hooks without direct user interaction.”
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.