A Russia aligned cyber threat group tracked as UAC-0184 has been observed abusing the Viber messaging platform to conduct targeted attacks against Ukrainian military and government organizations. The activity was detailed in a new technical report released by the 360 Threat Intelligence Center.
Researchers stated that the group has maintained a high operational tempo throughout 2025, focusing on intelligence collection against sensitive Ukrainian state institutions. The actor is also tracked under the name Hive0156 and is known for using conflict related lures to make its campaigns appear credible to victims.
Previously, the group relied heavily on phishing emails containing war themed content to deliver Hijack Loader, a malware component that later facilitates the deployment of Remcos RAT. The group was first publicly documented by CERT-UA in early January 2024. Over time, its tactics evolved to include the use of encrypted messaging platforms such as Signal and Telegram. The latest research shows that Viber has now been added to this delivery arsenal.
In the newly observed attack chain, Viber messages are used as the initial intrusion vector. Victims receive malicious ZIP archives that contain multiple Windows shortcut files, also known as LNK files. These files are disguised as legitimate Microsoft Word and Excel documents to trick recipients into opening them.
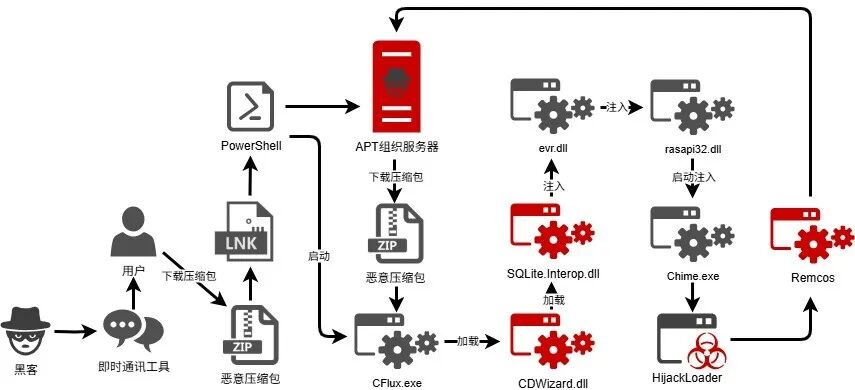
Once executed, the LNK files display a decoy document to reduce suspicion. At the same time, they silently trigger a PowerShell script in the background that downloads a second archive named “smoothieks.zip” from a remote server. This archive is responsible for reconstructing and launching Hijack Loader directly in memory.
The deployment process uses multiple evasion techniques, including DLL side loading and module stomping, to bypass detection by security solutions. Hijack Loader then surveys the infected system to identify installed security products such as Kaspersky, Avast, BitDefender, AVG, Emsisoft, Webroot, and Microsoft solutions. This is achieved by calculating CRC32 hashes associated with known security software components.
Beyond persistence through scheduled tasks, the loader actively attempts to weaken static signature based defenses. It then proceeds to execute Remcos RAT by injecting it into the legitimate Windows process “chime.exe.” Once active, Remcos grants attackers extensive control over the compromised endpoint, allowing them to execute commands, monitor user activity, deploy additional payloads, and exfiltrate sensitive data.
According to the 360 Threat Intelligence Center, Remcos is often marketed as legitimate remote system management software. However, its extensive surveillance and control capabilities have made it a popular choice among cyber espionage groups. Through its graphical control panel, attackers can conduct both automated batch operations and precise manual actions against infected systems.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.