Cybersecurity experts have uncovered a new phishing campaign targeting the European hospitality industry, where hotel staff are deceived through fake Booking.com emails that lead to malicious software installation. The operation, tracked under the name PHALT#BLYX, relies on deceptive ClickFix style techniques combined with fake system error messages.
Researchers from cybersecurity firm Securonix reported that the campaign was detected in late December 2025 and is designed to ultimately deploy a remote access trojan known as DCRat on victim systems.
Phishing Emails Masquerade as Booking.com Alerts
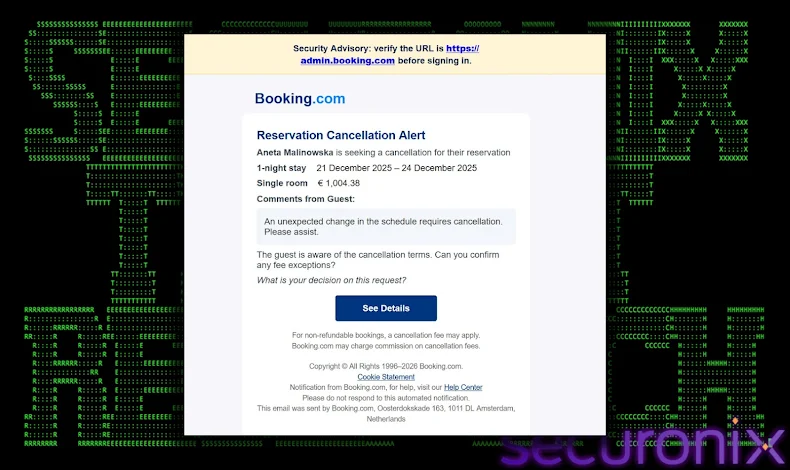
The attack begins with phishing emails that impersonate Booking.com and claim that a hotel reservation has been unexpectedly canceled. These emails encourage recipients to verify the cancellation by clicking an embedded link. Once clicked, the link redirects victims to a counterfeit website that closely mimics Booking.com branding, such as domains resembling legitimate booking services.
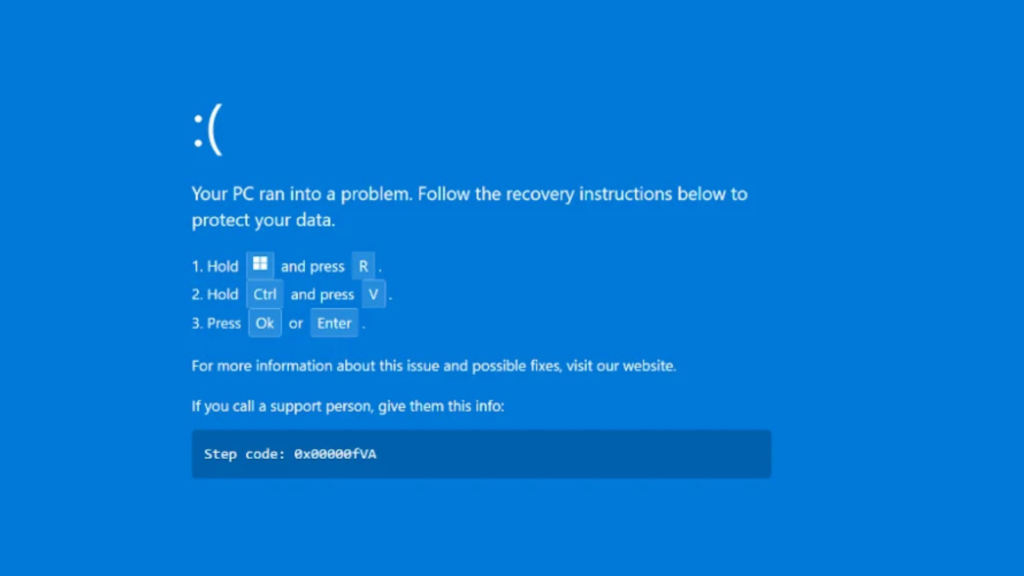
To increase credibility, the fake website displays a CAPTCHA page before redirecting users to a fabricated Blue Screen of Death (BSoD) error. Victims are presented with misleading recovery instructions that urge them to open the Windows Run dialog, paste a command, and press Enter.
In reality, following these steps triggers the execution of a malicious PowerShell command, silently initiating the malware delivery process.
Multi Stage Payload Delivery Using Trusted Windows Tools
The PowerShell command downloads an MSBuild project file named v.proj from a remote server and executes it using the legitimate Windows utility MSBuild.exe. This technique allows the attackers to abuse trusted system binaries, helping the malware evade detection.
The embedded payload configures Microsoft Defender Antivirus exclusions, establishes persistence by placing files in the Startup folder, and downloads the DCRat malware from the same remote location before launching it.
If the malware is executed with administrator privileges, it can disable security protections entirely. When elevated permissions are not available, the malware repeatedly triggers Windows User Account Control prompts in rapid succession, attempting to pressure the user into granting access.
As an added layer of deception, the PowerShell script opens the legitimate Booking.com administration page in the user’s default browser. This distraction creates the illusion that the previous steps were part of a normal process.
DCRat Capabilities and Threat Implications
DCRat, also known as Dark Crystal RAT, is a commercially available .NET based remote access trojan. It supports a modular plugin architecture that allows attackers to expand its functionality after infection. Once active, it can collect sensitive information, log keystrokes, execute commands remotely, and deploy additional payloads such as cryptocurrency miners.
Security analysts highlighted that this campaign demonstrates advanced living off the land techniques, where attackers misuse legitimate system tools to establish persistence and maintain long term access within compromised environments.
According to Securonix, the phishing emails include room charge details in Euros, indicating a focused campaign against European organizations. Additionally, the presence of Russian language artifacts within the MSBuild project file suggests possible links to Russian threat actors associated with DCRat activity.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.