Microsoft has issued a warning that threat actors are exploiting misconfigured email routing and weak spoofing protections to carry out phishing attacks that appear to originate from within an organization’s own domain.
According to the Microsoft Threat Intelligence team, attackers are abusing these routing weaknesses to deliver phishing emails that impersonate internal communications. These messages are often linked to phishing as a service platforms, including Tycoon 2FA, and are designed to steal user credentials.
Surge in Internal Spoofing Attacks Since Mid 2025
Microsoft stated that although this attack technique is not new, there has been a noticeable increase in its usage since May 2025. The campaigns have been opportunistic in nature, targeting organizations across multiple industries and business sectors.
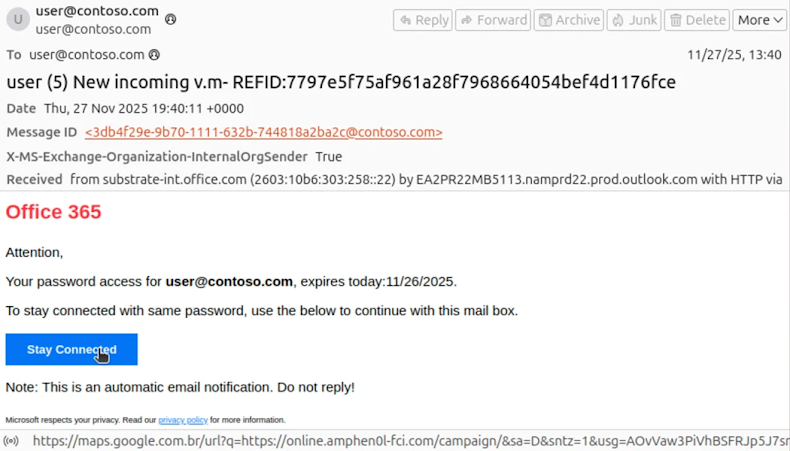
Phishing messages observed in these campaigns use a variety of themes, including fake voicemails, shared document notifications, human resources communications, password reset alerts, and account expiration warnings. In several cases, attackers have also leveraged this method to conduct financial fraud against targeted organizations.
If successful, these attacks can result in stolen credentials that may later be used for data theft, unauthorized access, or business email compromise incidents.
How Misconfigured Routing Creates a Security Gap
The issue primarily affects organizations that rely on complex email routing setups without enforcing strict spoof protection policies. One common example involves mail exchanger records being routed through on premises Exchange servers or third party services before reaching Microsoft 365.
This configuration can introduce a security gap that attackers exploit to send spoofed messages that appear to come from the organization’s own domain. Microsoft noted that most phishing campaigns using this approach rely on the Tycoon 2FA phishing toolkit.
In October 2025 alone, Microsoft blocked more than 13 million malicious emails associated with this platform.
Phishing as a Service Fuels Large Scale Abuse
Phishing as a service platforms provide ready to use tools that make it easy for cybercriminals to launch phishing campaigns. These services offer customizable templates, hosting infrastructure, and mechanisms to bypass multi factor authentication using adversary in the middle techniques.
This ease of use allows even low skill attackers to conduct large scale credential harvesting operations.
Financial Scams Disguised as Internal Communications
Microsoft also identified phishing emails designed to trick organizations into paying fraudulent invoices. These messages often impersonate well known services such as DocuSign or claim to originate from internal human resources departments regarding salary or benefits changes.
In financial scam scenarios, the emails are crafted to resemble conversations involving company executives, accounting teams, or external vendors. To make the scheme appear legitimate, the emails typically include multiple attachments, such as:
A fake invoice requesting payment of thousands of dollars
A fraudulent IRS W 9 form containing personal details
A counterfeit bank letter allegedly issued by an employee of the online bank
Attackers may also use clickable links, QR codes, or embedded content to redirect recipients to phishing pages. One of the most convincing aspects of these emails is that the sender and recipient addresses often appear identical, reinforcing the illusion of an internal message.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


