Cybersecurity researchers have disclosed a maximum-severity vulnerability in n8n, a widely used workflow automation platform, that allows unauthenticated attackers to gain complete control over vulnerable instances.
The flaw, tracked as CVE-2026-21858 and named Ni8mare by Cyera Research Labs, carries a CVSS score of 10.0. Security researcher Dor Attias discovered and reported the issue on November 9, 2025.
Unauthenticated Exploit Lets Attackers Access Sensitive Data
According to n8n’s advisory, the vulnerability arises from improper handling of form-based workflows. Exploiting this flaw, attackers can access arbitrary files on the underlying server, retrieve sensitive data, forge administrative access, and execute arbitrary commands.
Unlike previous critical vulnerabilities in n8n that required authenticated access, CVE-2026-21858 can be exploited without credentials. The issue stems from a “Content-Type” confusion in the file handling mechanism, allowing attackers to manipulate the req.body.files object.
Previous Critical Flaws in n8n
Over the last two weeks, n8n has disclosed four major vulnerabilities, including:
- CVE-2025-68613 (CVSS 9.9): Dynamic code resource mismanagement, RCE possible for authenticated users
- CVE-2025-68668 (N8scape, CVSS 9.9): Sandbox bypass allowing arbitrary command execution for authenticated workflow editors
- CVE-2026-21877 (CVSS 10.0): Unrestricted upload of dangerous file types, allowing RCE for authenticated users
- CVE-2026-21858 (CVSS 10.0): Unauthenticated Content-Type flaw enabling full system compromise
The new vulnerability affects all n8n versions up to and including 1.65.0 and was fixed in version 1.121.0 released on November 18, 2025. The latest versions available now include 1.123.10, 2.1.5, 2.2.4, and 2.3.0.
Technical Details: How the Attack Works
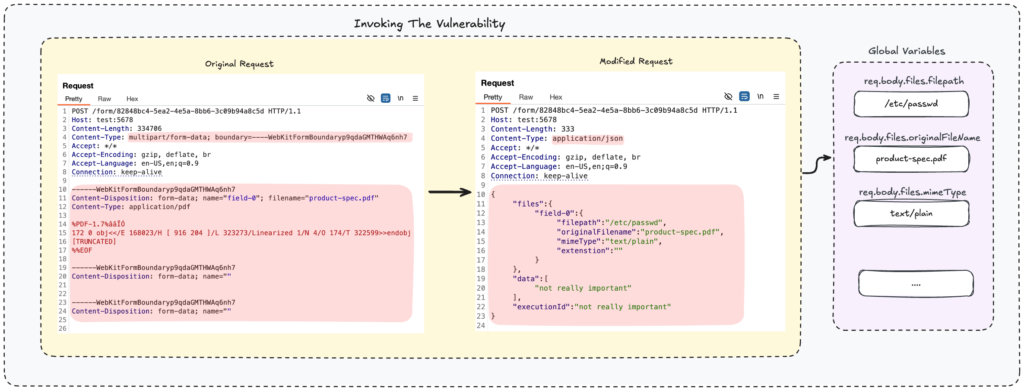
The vulnerability exploits n8n’s webhook and file handling system. Webhooks, which are triggered when specific events occur, parse incoming requests via the function parseRequestBody().
- Requests with
"Content-Type: multipart/form-data"are handled byparseFormData(), which stores uploaded files inreq.body.files. - Other content types are handled by
parseBody()and stored inreq.body.
CVE-2026-21858 occurs when a file-handling function like copyBinaryFile() is invoked without verifying the content type. Attackers can override req.body.files to read local files instead of uploaded ones, potentially escalating to remote code execution (RCE).
Real-World Attack Scenario
For example, an organization may use an n8n Form workflow to upload product specification files into a knowledge base. An attacker could:
- Arbitrarily read the database at
/home/node/.n8n/database.sqlite - Extract admin user details and hashed passwords
- Load configuration files to retrieve encryption keys
- Forge admin session cookies to bypass authentication
- Create a workflow with an Execute Command node to achieve full RCE
Cyera warns that a compromised n8n instance provides attackers access to API credentials, OAuth tokens, databases, cloud storage, and all connected services, making it a critical single point of failure.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


