Cybersecurity authorities have linked the notorious Black Cat gang to an ongoing SEO poisoning campaign that targets popular software searches, tricking users into downloading malicious backdoors capable of stealing sensitive information.
Fraudulent Sites Target Popular Software
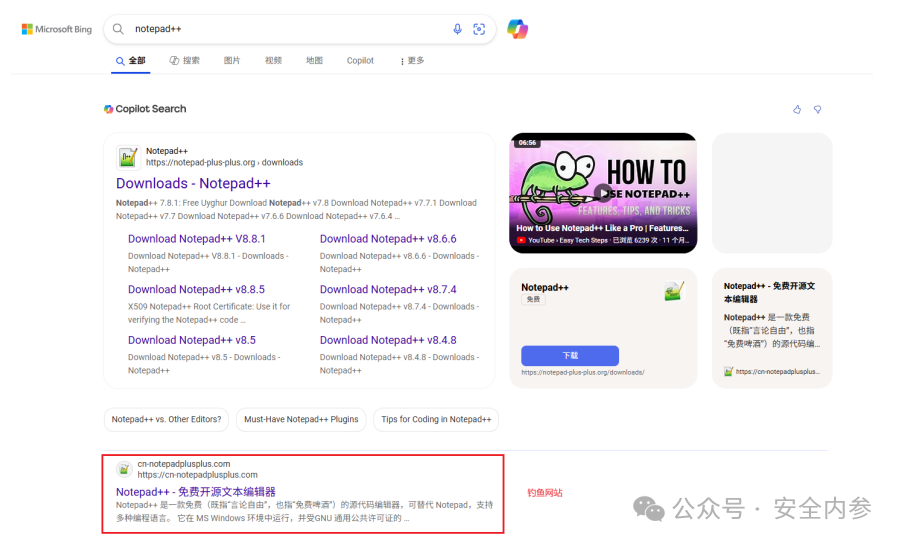
According to reports by CNCERT/CC and Beijing Weibu Online (ThreatBook), the threat actors manipulate search engine results on platforms like Microsoft Bing, pushing fake websites to the top of queries for software such as Google Chrome, Notepad++, QQ International, and iTools.
Once users visit these high-ranking phishing pages, they are presented with crafted download pages that bundle legitimate-looking software with malware. When installed, the malicious program silently deploys a backdoor, allowing attackers to exfiltrate sensitive data from the victim’s system.
Black Cat has been active since at least 2022, using these tactics to steal data and gain remote control of infected hosts. In 2023, the group reportedly impersonated the cryptocurrency trading platform AICoin, stealing over $160,000 in digital assets.
Latest Targets and Methods
Recent campaigns have targeted Notepad++ users, directing them to a phishing domain “cn-notepadplusplus[.]com”. Other domains associated with Black Cat include “cn-obsidian[.]com,” “cn-winscp[.]com,” and “notepadplusplus[.]cn.” The inclusion of “cn” indicates a focus on Chinese users searching for these tools online.
Clicking the fake download link redirects users to a GitHub-like URL (“github.zh-cns[.]top”), where a ZIP archive containing an installer is downloaded. This installer creates a desktop shortcut, which in turn side-loads a malicious DLL that launches the backdoor.
The malware communicates with a hard-coded server (“sbido[.]com:2869“), allowing attackers to:
- Steal web browser data
- Log keystrokes
- Extract clipboard contents
- Harvest other sensitive information from the compromised host
Scope of the Campaign
CNCERT/CC and ThreatBook reported that approximately 277,800 systems in China were compromised between July and December 2025, with the peak daily infections reaching 62,167 hosts.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.