Russian state-sponsored threat actors linked to APT28, also known as BlueDelta, have been identified running an ongoing credential-harvesting operation aimed at energy research and policy-related organizations across multiple regions.
According to findings, the campaign primarily targeted individuals connected to a Turkish energy and nuclear research body, employees of a European policy think tank, and organizations operating in North Macedonia and Uzbekistan. APT28 is widely assessed to operate under Russia’s military intelligence service, the Main Directorate of the General Staff of the Armed Forces of the Russian Federation (GRU).
Security researchers noted that the attackers used Turkish-language phishing lures and region-specific content to increase trust among carefully selected professional audiences. These tactics indicate a focused interest in sectors related to energy research, defense collaboration, and government communication, all of which align with long-standing Russian intelligence priorities.
The activity, observed in February and September 2025, relied on fake authentication pages designed to closely resemble legitimate platforms such as Microsoft Outlook Web Access (OWA), Google login portals, and Sophos VPN interfaces.
One notable aspect of the operation is the redirection technique. After victims unknowingly submit their credentials on the malicious pages, they are redirected to the legitimate service websites. This approach reduces suspicion and helps the attackers avoid triggering immediate security alerts.
The infrastructure supporting the campaign made extensive use of legitimate online services, including Webhook[.]site, InfinityFree, Byet Internet Services, and ngrok, which were leveraged to host phishing pages, collect stolen credentials, and manage traffic redirections.
To further enhance authenticity, the attackers distributed legitimate PDF documents as bait. These included a Gulf Research Center publication analyzing the June 2025 Iran–Israel conflict, as well as a July 2025 Mediterranean policy briefing released by the climate-focused think tank ECCO.
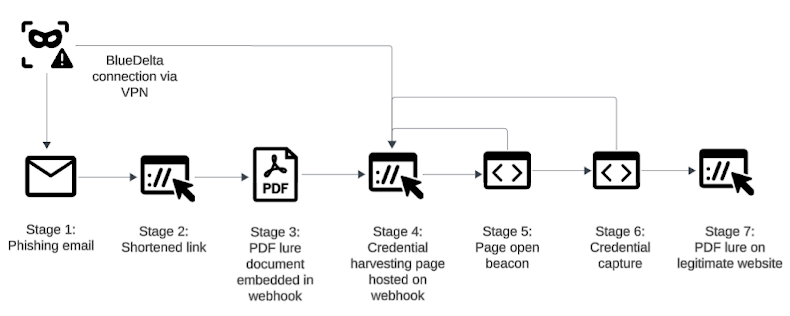
The attack sequence typically began with a phishing email containing a shortened link. When clicked, the link redirected users to a webhook-hosted page that briefly displayed a decoy document for a few seconds before forwarding the victim to a spoofed Microsoft OWA login page. Embedded JavaScript then silently transmitted entered credentials to an attacker-controlled endpoint before redirecting the user back to the real document source.
Researchers also identified three additional APT28 campaigns in 2025:
- A June 2025 operation that used a fake Sophos VPN password reset page hosted on InfinityFree, targeting an unnamed European Union think tank
- A September 2025 campaign that warned users about expired passwords and redirected victims to legitimate portals associated with a military organization in North Macedonia and an IT firm in Uzbekistan
- An April 2025 campaign that deployed a counterfeit Google password reset page hosted on Byet Internet Services, with stolen credentials exfiltrated via an ngrok endpoint
Analysts concluded that APT28’s repeated misuse of legitimate hosting platforms reflects a deliberate strategy to maintain low-cost, disposable infrastructure. This persistent focus on credential theft highlights the GRU’s continued reliance on phishing as an effective method for gathering intelligence and sustaining long-term access to sensitive networks.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


