A renewed wave of GoBruteforcer activity has been observed targeting databases linked to cryptocurrency and blockchain projects. The campaign aims to hijack vulnerable servers and enroll them into a botnet capable of brute forcing user credentials for services such as FTP, MySQL, PostgreSQL, and phpMyAdmin on Linux based systems.
Campaign Drivers and Initial Findings
According to an analysis published by Check Point Research, the current surge in attacks is being fueled by two primary factors. The first is the widespread reuse of AI generated server deployment examples that replicate common usernames and weak default credentials. The second is the continued exposure of legacy web stacks, particularly XAMPP installations, which often leave FTP services and administrative panels accessible with minimal security hardening.
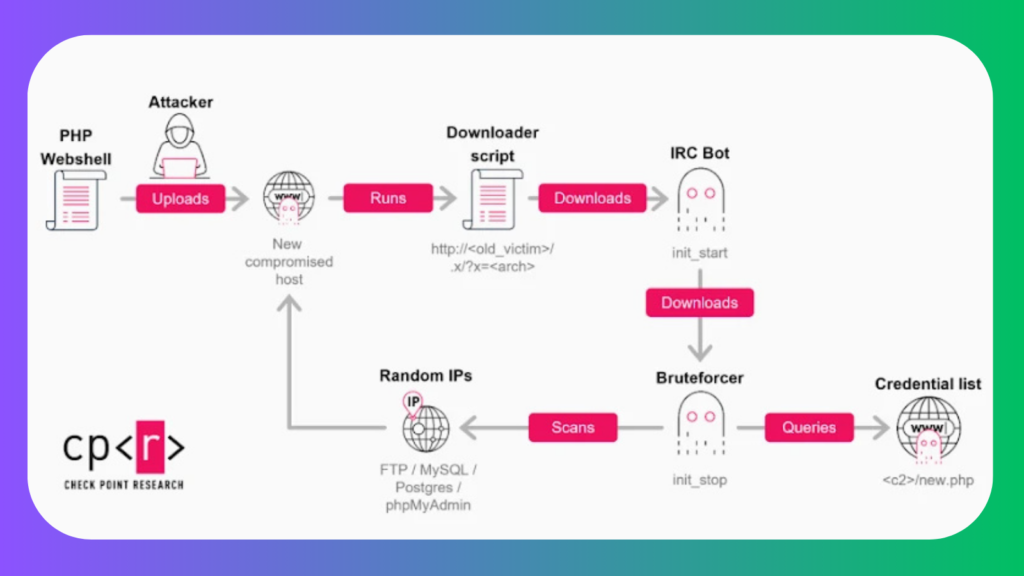
GoBruteforcer, also known as GoBrut, was first documented by Palo Alto Networks Unit 42 in March 2023. At the time, researchers detailed its ability to target Unix like operating systems across x86, x64, and ARM architectures. The malware deploys an IRC based bot and a web shell, enabling remote access and the retrieval of brute force modules to scan for additional vulnerable systems and expand the botnet.
Evolution of the Malware
Further research by Black Lotus Labs at Lumen Technologies in September 2025 revealed that a portion of infected systems controlled by the SystemBC malware family were also participating in the GoBruteforcer botnet.
Check Point later identified a more advanced Golang based version of the malware in mid 2025. This iteration includes a heavily obfuscated IRC bot rewritten for cross platform compatibility, enhanced persistence mechanisms, process masking techniques, and dynamically updated credential lists.
Abuse of Common and AI Learned Credentials
The credential sets used by the attackers combine widely used usernames and passwords such as myuser with simple password patterns, as well as admin style credentials. These combinations are not random. Many of them appear in official database tutorials, vendor documentation, and online guides that have been incorporated into large language model training data. As a result, AI generated deployment examples often reproduce the same insecure defaults.
Additional usernames specifically target cryptocurrency environments, including names like cryptouser, appcrypto, and crypto, while others are tailored for phpMyAdmin and content management systems, such as root, wordpress, and wpuser.
Check Point noted that attackers typically reuse a small but stable password pool per campaign, frequently rotating usernames and niche credential sets to pursue different targets. FTP brute force attempts rely on a hardcoded list of credentials embedded directly into the malware binary, pointing toward common web hosting stacks and default service accounts.
Infection Chain and Botnet Capabilities
In observed attacks, an exposed FTP service on servers running XAMPP serves as the initial entry point. Once access is gained, attackers upload a PHP web shell, which is then used to download and execute an updated IRC bot via a shell script tailored to the system architecture.
After infection, compromised hosts can serve multiple roles within the botnet. These include launching brute force attacks against FTP, MySQL, PostgreSQL, and phpMyAdmin services across the internet, hosting and distributing payloads to other compromised systems, or acting as IRC style control nodes and backup command and control infrastructure for resilience.
Focus on Blockchain Projects
Further investigation revealed that at least one compromised host was used to stage a module designed to iterate through a list of TRON blockchain addresses. The module queried balances through the tronscanapi service to identify wallets with non zero funds. This behavior strongly suggests a targeted effort against blockchain and cryptocurrency projects.
Check Point emphasized that GoBruteforcer reflects a persistent and widespread security issue, where exposed infrastructure, weak credentials, and automation combine to enable large scale compromise. While the botnet itself is technically simple, its operators benefit from the abundance of misconfigured services still accessible online.
Related Internet Wide Scanning Activity
The disclosure coincides with findings from GreyNoise, which reported systematic scanning activity aimed at identifying misconfigured proxy servers that could expose access to commercial large language model services.
One campaign exploited server side request forgery vulnerabilities to target Ollama model pull functionality and Twilio SMS webhook integrations between October 2025 and January 2026. Based on the use of ProjectDiscovery OAST infrastructure, this activity is believed to originate from security researchers or bug bounty hunters.
A second campaign, beginning on December 28, 2025, involved high volume enumeration of exposed or misconfigured LLM endpoints linked to providers such as Alibaba, Anthropic, DeepSeek, Google, Meta, Mistral, OpenAI, and xAI. The scanning activity originated from two specific IP addresses and generated tens of thousands of sessions within days.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.