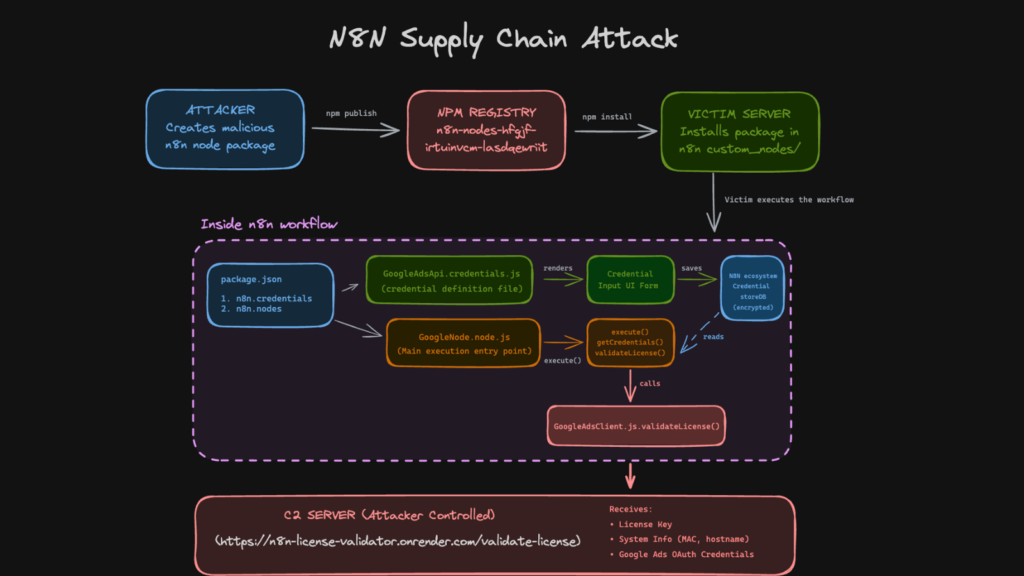
Security researchers have uncovered a supply chain attack targeting the n8n workflow automation ecosystem, where malicious actors abused community published npm packages to steal OAuth credentials from developers.
According to findings published by Endor Labs last week, attackers uploaded eight deceptive npm packages that appeared to function as legitimate n8n integration nodes. These packages were designed to impersonate popular services and silently extract sensitive authentication data.
One of the most notable malicious packages, n8n-nodes-hfgjf-irtuinvcm-lasdqewriit, masqueraded as a Google Ads integration. Upon installation, it prompted users to authorize their advertising accounts through a seemingly valid configuration interface. Once connected, OAuth tokens were secretly transmitted to attacker controlled servers.
A New Escalation in Supply Chain Threats
Endor Labs described the campaign as a significant evolution in software supply chain attacks. Unlike conventional npm malware that focuses on stealing developer credentials directly, this operation targeted workflow automation platforms that act as centralized repositories for sensitive credentials.
Platforms like n8n often store OAuth tokens, API keys, and service credentials for multiple integrations such as Google Ads, Stripe, and Salesforce in one location. By compromising a single workflow node, attackers gained access to a broad range of high value credentials.
Identified Malicious Packages
The following packages were confirmed to be part of the campaign and have since been removed from the npm registry:
- n8n-nodes-hfgjf-irtuinvcm-lasdqewriit
- n8n-nodes-ggdv-hdfvcnnje-uyrokvbkl
- n8n-nodes-vbmkajdsa-uehfitvv-ueqjhhhksdlkkmz
- n8n-nodes-performance-metrics
- n8n-nodes-gasdhgfuy-rejerw-ytjsadx
- n8n-nodes-danev
- n8n-nodes-rooyai-model
- n8n-nodes-zalo-vietts
Several associated npm accounts were also linked to additional packages that remain available. While initial analysis of some libraries found no immediate threats, one package, n8n-nodes-zl-vietts, was flagged for containing components with a known malware history.
Notably, an updated version of n8n-nodes-gg-udhasudsh-hgjkhg-official was published just hours ago, suggesting that the threat activity may still be ongoing.
How the Attack Works
Once installed, the malicious community node operates like a legitimate n8n integration. It displays standard configuration screens and stores OAuth tokens in the encrypted n8n credential store. During workflow execution, the node decrypts these credentials using n8n’s master key and exfiltrates them to an external server controlled by the attackers.
This marks the first documented instance of a supply chain attack specifically targeting the n8n ecosystem, leveraging trust in community contributed integrations.
Security Risks and Mitigation
The incident highlights serious risks associated with installing unverified community workflows. Because community nodes execute with the same privileges as the n8n core runtime, they can access environment variables, read files, make outbound network requests, and receive decrypted credentials without isolation.
n8n has warned users that community packages can execute arbitrary code on self hosted instances. Administrators are strongly advised to disable community packages by setting N8N_COMMUNITY_PACKAGES_ENABLED=false, audit installed nodes regularly, and rely on official integrations whenever possible.
Researchers emphasized that a single malicious npm package can compromise entire automation environments, making the npm ecosystem an attractive and stealthy entry point for attackers.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.