Cybersecurity researchers have revealed a previously unknown and highly sophisticated Linux malware framework known as VoidLink, which is purpose built to maintain long term, covert access to cloud based infrastructures. The malware specifically targets Linux systems that form the backbone of modern cloud services and containerized environments.
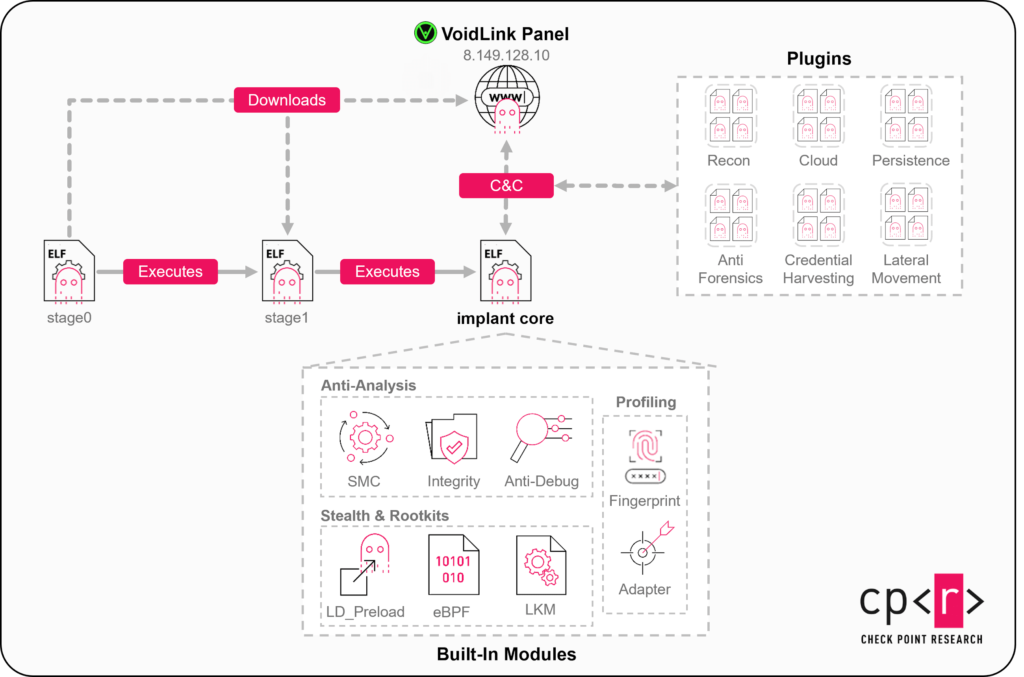
According to a recent analysis published by Check Point Research, VoidLink was first identified in December 2025 and has been actively developed since then. The framework is composed of custom loaders, implants, rootkits, and a large collection of modular plugins that allow attackers to dynamically expand or alter functionality as operational goals evolve.
Modular Design Built for Cloud Persistence
Researchers state that VoidLink is engineered for stability and persistence in cloud native environments. Its architecture is centered around a proprietary Plugin API, which bears conceptual similarities to the Beacon Object Files approach used by Cobalt Strike. More than 30 plugin modules are available by default, enabling flexible post exploitation workflows.
This development highlights a broader shift in attacker focus, moving away from Windows centric malware toward Linux systems that now power critical cloud platforms. Based on tooling complexity, infrastructure awareness, and development patterns, VoidLink is assessed to be associated with China aligned threat actors.
Cloud and Container Awareness
VoidLink features a cloud first implant written in the Zig programming language. It is capable of identifying major cloud providers, including Amazon Web Services, Google Cloud, Microsoft Azure, Alibaba Cloud, and Tencent Cloud. The malware can also determine whether it is operating inside Docker containers or Kubernetes pods and adjust its behavior accordingly.
In addition, the framework can harvest credentials linked to cloud platforms and widely used source code management systems such as Git. This targeting strongly suggests an intent to compromise software developers or DevOps environments, potentially enabling data theft or supply chain attacks.
Extensive Post Exploitation Capabilities
VoidLink includes a broad set of advanced features that elevate it beyond typical Linux malware. These capabilities include rootkit style techniques using LD_PRELOAD, loadable kernel modules, and eBPF to conceal processes depending on kernel version. The framework also supports in memory plugins, allowing new functions to be loaded without touching disk.
Command and control communication is supported over multiple channels, including HTTP, HTTPS, WebSocket, ICMP, and DNS tunneling. Compromised hosts can also form peer to peer or mesh style networks, increasing resilience and operational flexibility.
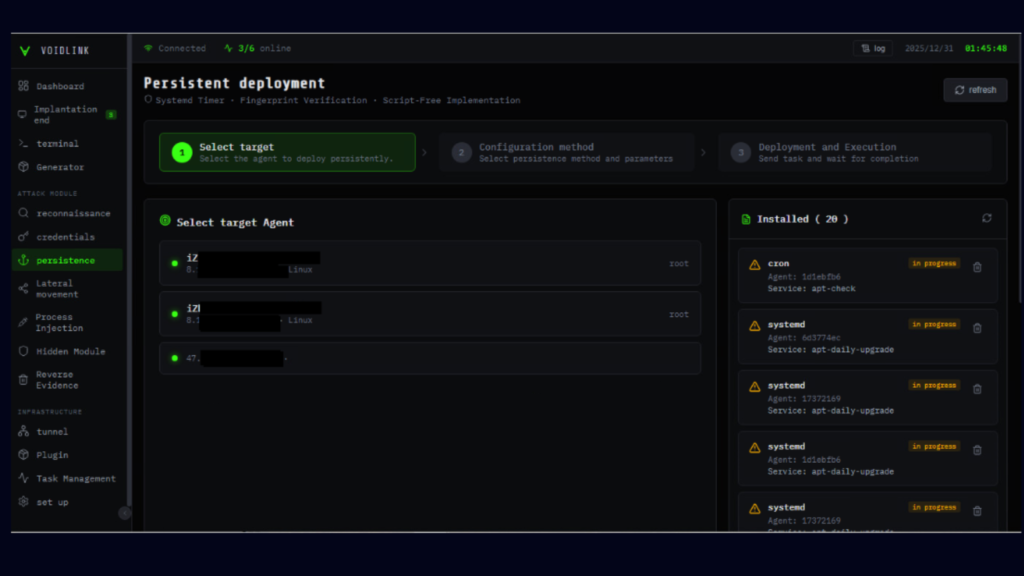
A Chinese language web based control panel allows attackers to manage infected systems, deploy custom builds in real time, control files and tasks, and execute all stages of the attack lifecycle. This includes reconnaissance, persistence, lateral movement, and defense evasion through log and artifact removal.
Plugin Ecosystem and Anti Detection Features
The framework supports at least 37 plugins covering anti forensics, reconnaissance, container exploitation, privilege escalation, lateral movement, and persistence. Anti forensic modules can erase or manipulate logs, modify shell history, and alter file timestamps to obstruct investigation.
VoidLink also includes advanced anti analysis mechanisms. It detects debugging tools and monitoring software, and it can remove itself entirely if tampering is detected. A self modifying code feature allows sensitive code sections to be decrypted only at runtime and re encrypted afterward, bypassing memory scanning defenses.
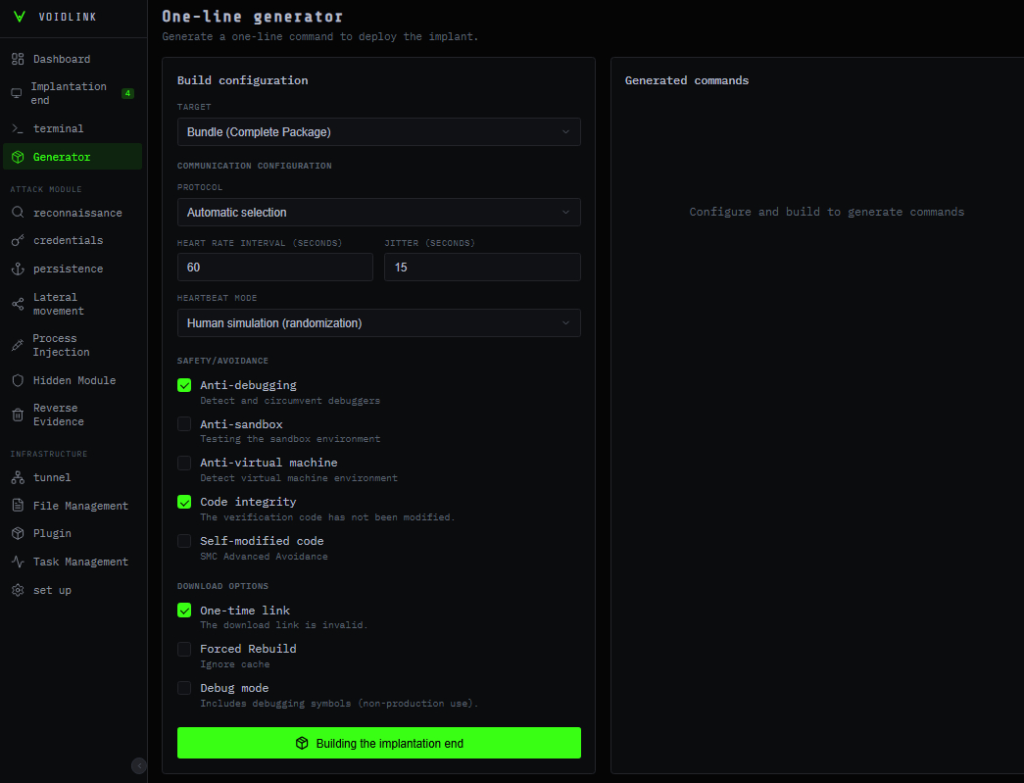
Additionally, the malware evaluates installed security controls on the compromised system to generate a risk profile. Based on this assessment, it dynamically selects evasion strategies, such as throttling scans or limiting activity in high risk environments.
Check Point researchers described VoidLink as significantly more advanced than most Linux threats observed in the wild, noting the attackers’ expertise across multiple programming languages, including Go, Zig, C, and modern web frameworks. Combined with deep knowledge of operating system internals, VoidLink represents a serious and evolving threat to cloud and container ecosystems.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.