Cybersecurity researchers have uncovered a large scale web skimming operation that has remained active since January 2022, silently harvesting payment card data from compromised online checkout pages. The campaign targets organizations connected to major global payment networks, including American Express, Diners Club, Discover, JCB, Mastercard, and UnionPay.
According to a newly published report by Silent Push, enterprise level businesses that rely on these payment providers are the most likely victims of the operation.
Magecart Style Digital Skimming Attacks
The campaign falls under the category of digital skimming attacks, a form of client side compromise where attackers inject malicious JavaScript into legitimate e commerce websites and payment portals. When customers enter their payment information during checkout, the injected code quietly captures sensitive details without raising visible alarms.
Such attacks are commonly grouped under the Magecart umbrella, a term originally associated with cybercriminal groups that exploited Magento based stores before expanding to a wide range of platforms and technologies.
Silent Push identified the activity while investigating a suspicious domain connected to Stark Industries, a bulletproof hosting provider that has since been sanctioned. The infrastructure has reportedly been rebranded as THE[.]Hosting and is now operated by the Dutch entity WorkTitans B.V., a move researchers believe was intended to bypass sanctions.
Obfuscated JavaScript and Anti Detection Techniques
The domain cdn-cookie[.]com was found hosting heavily obfuscated JavaScript files, such as recorder.js and tab-gtm.js. These scripts are embedded into vulnerable web stores and function as credit card skimmers.
To avoid detection, the malicious code actively checks the Document Object Model for the presence of an element named wpadminbar. This element appears on WordPress sites when administrators or authorized users are logged in.
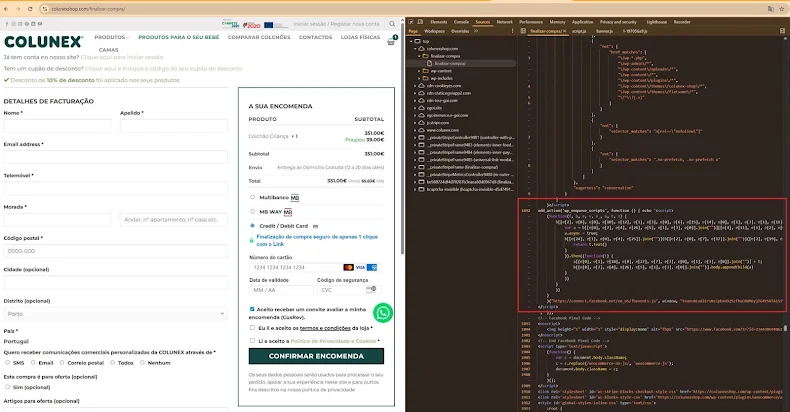
If wpadminbar is detected, the skimmer immediately triggers a self removal routine, erasing itself from the page to avoid being spotted by site owners. The script also re attempts execution whenever the page DOM changes, which naturally occurs as users interact with checkout forms.
Fake Stripe Forms and Data Theft
The skimmer includes specialized logic for Stripe based payment flows. If Stripe is selected and a browser localStorage value called wc_cart_hash is not present, the malware creates this flag and sets it to false, signaling that the victim has not yet been skimmed.
The skimmer then replaces the legitimate Stripe payment form with a visually convincing fake version through user interface manipulation. Victims unknowingly enter their credit card number, expiration date, and CVC into the fraudulent form.
After submission, the page displays a payment error message, making it appear as though the transaction failed due to incorrect input. In reality, the entered data has already been stolen.
Data Exfiltration and Cleanup
Beyond credit card details, the skimmer also collects additional personal data, including customer names, email addresses, phone numbers, and shipping information. This data is transmitted via HTTP POST requests to the remote server lasorie[.]com.
Once exfiltration is complete, the malware removes the fake payment form, restores the legitimate Stripe interface, and sets wc_cart_hash to true. This prevents the skimmer from targeting the same victim again and helps reduce suspicion.
Silent Push noted that the threat actor demonstrates deep technical knowledge of WordPress internals, leveraging even lesser known platform features to maintain stealth and persistence throughout the attack chain.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


