Security researchers have disrupted a major botnet operation after null-routing traffic linked to more than 550 command-and-control servers tied to the AISURU and Kimwolf botnets. The takedown was carried out by Black Lotus Labs, the threat intelligence arm of Lumen Technologies, and began in early October 2025.
These botnets have rapidly grown into some of the largest active malicious networks, abusing millions of compromised devices to power distributed denial-of-service attacks and residential proxy services.
What Are AISURU and Kimwolf
AISURU and its Android-based variant Kimwolf are large-scale botnets capable of directing infected devices to perform coordinated malicious activities. Their primary uses include launching DDoS attacks and selling access to compromised devices as residential proxies.
Kimwolf came into the spotlight after QiAnXin XLab published a detailed technical analysis showing how the malware infects mostly unsanctioned Android TV streaming devices. These devices are compromised either through pre-installed shady applications or by directly delivering a software development kit called ByteConnect.
Massive Android Device Infection
The botnet has expanded aggressively by targeting Android devices with exposed Android Debug Bridge services. By tunneling through residential proxy networks, threat actors were able to compromise more than 2 million Android TV boxes, effectively turning them into proxy nodes.
A follow-up investigation by Synthient revealed that Kimwolf operators were actively selling proxy bandwidth, offering infected residential IP addresses in exchange for upfront payments.
Infrastructure and Proxy Abuse
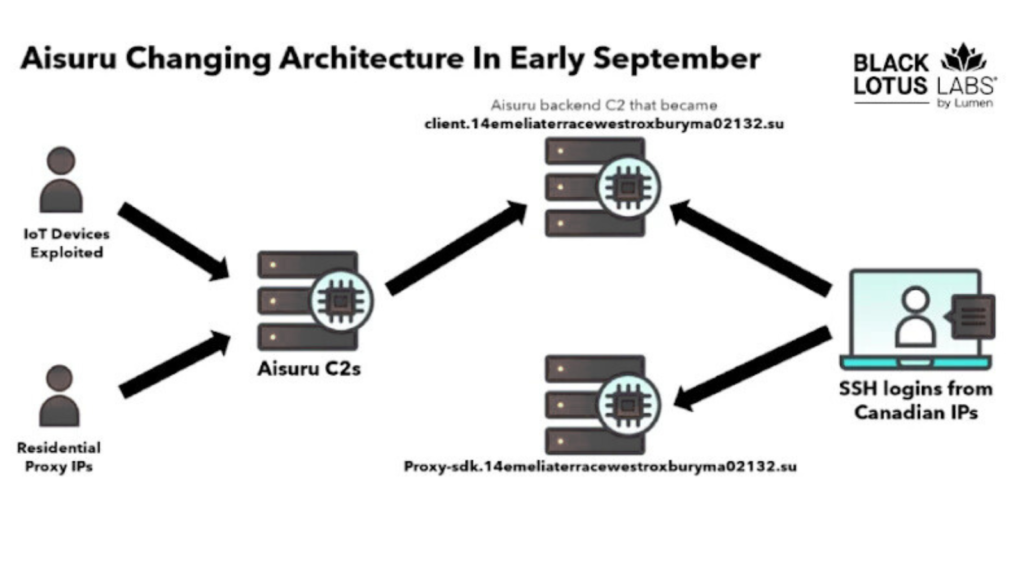
Black Lotus Labs identified suspicious residential SSH connections in September 2025 while analyzing AISURU backend infrastructure. These connections originated from multiple Canadian IP addresses and were used to access known proxy-related domains.
One of the domains involved briefly surpassed Google in Cloudflare’s top 100 domains list in November 2025, before being removed due to abuse concerns. Shortly after, researchers identified additional command servers hosted by a Utah-based provider called Resi Rack LLC, a company that markets itself as a premium game server hosting service.
This discovery aligned with reporting from independent journalist Brian Krebs, who uncovered Discord-based marketplaces where botnet-backed proxy services were being sold. The Resi Rack environment was reportedly linked to these operations for nearly two years.
Explosive Botnet Growth
Researchers observed a dramatic spike in Kimwolf activity in early October 2025. Within just seven days, the number of new bots increased by 300 percent, eventually reaching around 800,000 newly added devices by mid-month.
Nearly all of these infected devices were found listed for sale through a single residential proxy service, highlighting the commercial scale of the operation.
Exploitation of Proxy Services
Between October 20 and November 6, 2025, Kimwolf command servers were seen scanning PYPROXY and similar services for vulnerable endpoints. This activity exploited weaknesses in certain proxy platforms, allowing attackers to interact with internal networks behind residential proxy nodes.
Once a device was compromised, its public residential IP address was offered for rent. Threat actors could then use this access to scan local networks for other exposed devices, particularly Android systems with ADB enabled, enabling further spread of the botnet.
Null-Routing and Countermeasures
After Black Lotus Labs successfully null-routed one major command server in October 2025, the botnet operators quickly shifted infrastructure to a new IP address. This move triggered another spike in malicious traffic linked to malware hosting servers operating on infrastructure previously associated with AISURU.
Despite these evasive tactics, researchers were able to continue disrupting botnet operations by cutting off routing to newly identified control nodes.
Broader Proxy Abuse Trend
The disclosure coincides with another investigation by Chawkr, which uncovered a sophisticated proxy network of 832 compromised KeeneticOS routers operating across multiple Russian internet service providers.
All affected routers shared identical configurations and SSH fingerprints, suggesting automated mass exploitation using stolen credentials, embedded backdoors, or unpatched firmware flaws. These compromised routers functioned as residential proxy nodes, blending malicious traffic into normal household internet activity.
Why Residential Proxies Are Dangerous
Unlike datacenter or cloud-based IP addresses, residential endpoints are far harder to detect and block. Their clean reputation and legitimate classification allow attackers to evade traditional security filters and reputation-based defenses.
This trend shows how consumer devices, such as routers and Android TV boxes, are increasingly being weaponized as stealth infrastructure for large-scale cybercrime and multi-stage attacks.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.