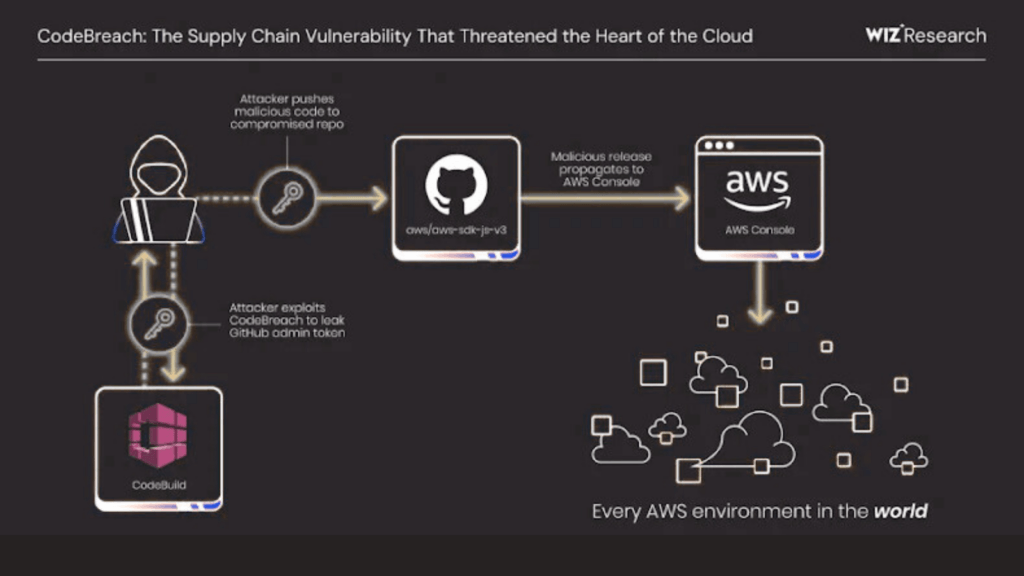
Cloud security researchers have revealed that a critical misconfiguration in AWS CodeBuild could have allowed attackers to fully compromise Amazon Web Services owned GitHub repositories, including the widely used AWS JavaScript SDK. The issue created a potential pathway for large scale supply chain attacks that could have impacted countless AWS customers.
The vulnerability, named CodeBreach by cloud security firm Wiz, was responsibly disclosed to AWS on August 25, 2025, and fully remediated in September 2025. Researchers Yuval Avrahami and Nir Ohfeld warned that successful exploitation could have enabled attackers to inject malicious code into trusted AWS repositories, potentially affecting applications across the entire AWS ecosystem, including the AWS Management Console.
How the CodeBreach Issue Occurred
According to Wiz, the issue stemmed from weaknesses in AWS CodeBuild continuous integration pipelines. These weaknesses could have allowed unauthenticated attackers to breach the build environment, leak high privilege credentials such as GitHub administrator tokens, and use them to modify source code directly.
AWS CodeBuild supports webhook filters to ensure that only trusted GitHub events can trigger build jobs. These filters are commonly configured to allow builds only from specific branches or from trusted GitHub actor IDs. This design is intended to prevent untrusted pull requests from gaining access to sensitive build processes.
However, several AWS managed open source repositories implemented these webhook filters incorrectly.
Affected AWS GitHub Repositories
The misconfiguration impacted the following AWS maintained repositories that were configured to run builds on pull requests:
- aws-sdk-js-v3
- aws-lc
- amazon-corretto-crypto-provider
- awslabs/open-data-registry
These projects used an ACTOR_ID based filter but failed to include proper regular expression anchors. As a result, the filter did not enforce an exact match and allowed actor IDs that merely contained the trusted ID as part of a longer number.
Exploitation Path and Privilege Escalation
GitHub assigns numeric user IDs sequentially. Wiz researchers discovered that newly created GitHub accounts would regularly receive IDs that mathematically overlapped trusted maintainer IDs. By repeatedly creating automated bot accounts through GitHub Apps, attackers could predictably generate a matching actor ID within days.
Once such an ID was obtained, an attacker could trigger AWS CodeBuild jobs and extract sensitive credentials from the build environment. In the case of the aws-sdk-js-v3 project, this included a Personal Access Token belonging to an automation account with full administrative access to the repository.
With this level of access, attackers could push malicious code directly to the main branch, approve pull requests, and extract repository secrets, effectively enabling a supply chain compromise.
AWS Response and Mitigation
AWS confirmed that the issue was caused by repository specific misconfigurations rather than a flaw in the CodeBuild service itself. The company stated that all affected configurations have been corrected and additional safeguards have been implemented.
AWS also rotated exposed credentials and hardened build pipelines that store GitHub tokens or other secrets in memory. Importantly, the company reported that there is no evidence that CodeBreach was exploited in the wild prior to remediation.
Security Lessons for CI CD Environments
Security experts emphasize that untrusted contributions should never be allowed to trigger privileged CI CD pipelines. Recommended safeguards include anchoring regular expressions in webhook filters, generating unique Personal Access Tokens for each build project, limiting token permissions to the minimum required, and using unprivileged service accounts for CI integrations.
Wiz researchers noted that CI CD systems remain an attractive target due to their complexity and access to high value credentials. A small configuration mistake can have ecosystem wide consequences.
Growing Scrutiny of CI CD Pipeline Security
This incident adds to a growing list of CI CD security concerns. Previous research has demonstrated how insecure GitHub Actions workflows triggered by pull_request_target can leak privileged tokens and enable unauthorized access across multiple open source projects.
Security analysts have repeatedly warned that workflows handling untrusted code must apply strict validation. Failure to do so can result in remote code execution, secret exfiltration, and persistent repository compromise.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.