Security researchers have identified a new evasion technique used by the GootLoader JavaScript malware, in which attackers rely on malformed ZIP files created by combining hundreds of compressed archives into a single payload to avoid analysis and detection.
According to Expel security researcher Aaron Walton, the threat actor deliberately creates corrupted ZIP archives as an anti analysis tactic. Most third party extraction tools fail to open the file, while the default Windows ZIP extractor continues to process it without issues.
This behavior prevents automated security pipelines from inspecting the contents, while still allowing victims to open the archive using built in Windows tools and execute the malicious JavaScript file inside.
GootLoader is commonly distributed through SEO poisoning and malvertising campaigns, targeting users searching for legal document templates. These searches redirect victims to compromised WordPress websites that host malicious ZIP downloads. The malware has remained active in real world attacks since at least 2020 and is known for delivering secondary payloads such as ransomware.
In late October 2025, researchers observed a renewed wave of activity featuring advanced delivery techniques. These included the use of custom WOFF2 fonts with glyph substitution to disguise file names, along with abuse of the WordPress comment submission endpoint at /wp-comments-post.php to serve ZIP payloads when users click download buttons.
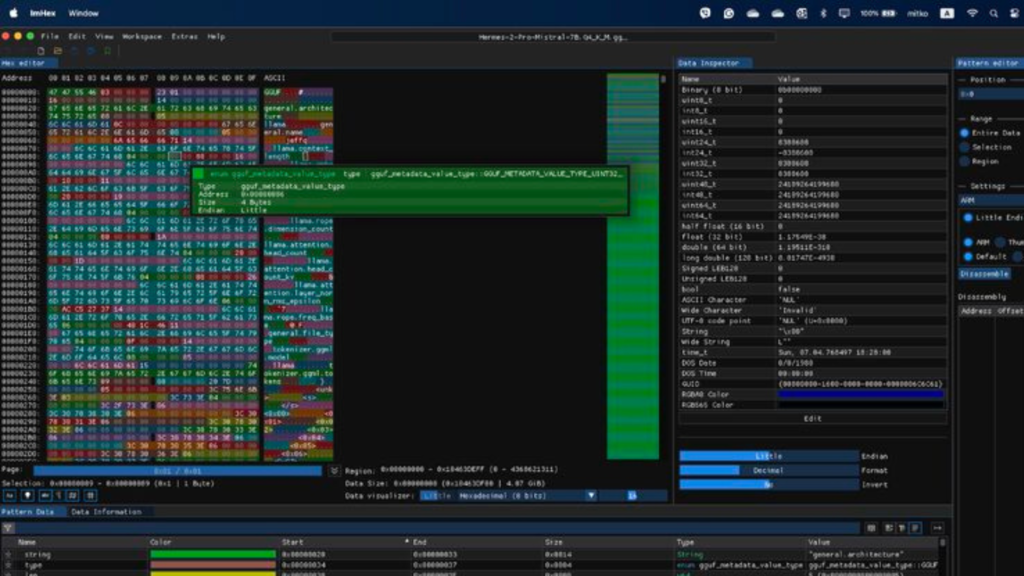
Recent analysis shows the delivery method has evolved further through multiple obfuscation layers:
- Combining 500 to 1,000 ZIP archives into a single malformed file
- Truncating the End of Central Directory record to remove critical structural bytes
- Randomizing non essential fields such as disk number values to confuse extraction tools

Walton explained that the random archive structure and constantly changing metadata represent a defense evasion technique known as hashbusting. Each victim receives a unique ZIP file, making hash based detection ineffective. This technique is also applied to the JavaScript payload contained inside the archive.
The infection chain begins with the ZIP file being delivered as an XOR encoded blob. On the client side, the data is decoded and repeatedly appended until it reaches a specific size. This process helps the malware bypass network level security controls that look for standard ZIP signatures.
When a victim double clicks the downloaded archive, Windows File Explorer opens the ZIP folder directly. Launching the JavaScript file executes it through wscript.exe from a temporary directory without fully extracting the contents.
The malware then creates a shortcut file in the Windows Startup folder to maintain persistence. It proceeds to run a second JavaScript file using cscript.exe, which launches PowerShell commands to advance the infection. In earlier campaigns, these PowerShell scripts collected system details and communicated with remote command servers.
To reduce exposure to GootLoader infections, organizations are advised to restrict execution of wscript.exe and cscript.exe for downloaded files when not required. Security teams can also enforce Group Policy settings to ensure JavaScript files open in Notepad by default rather than executing automatically.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.