Security researchers have disclosed a critical zero-day flaw in Cloudflare’s Web Application Firewall that allowed attackers to bypass security rules and directly access origin servers that were supposed to be fully protected.
The issue was identified by researchers from FearsOff, who discovered that HTTP requests sent to the /.well-known/acme-challenge/ path could reach backend servers even when customers had configured their WAF to block all incoming traffic.
This directory is commonly used by the Automatic Certificate Management Environment protocol, which automates SSL and TLS certificate issuance. Under the HTTP-01 validation method, Certificate Authorities verify domain ownership by requesting a one-time token from a specific file located under the ACME challenge path. This mechanism is designed to allow limited access for certificate validation only, not unrestricted access to the origin server.
How the Bypass Worked
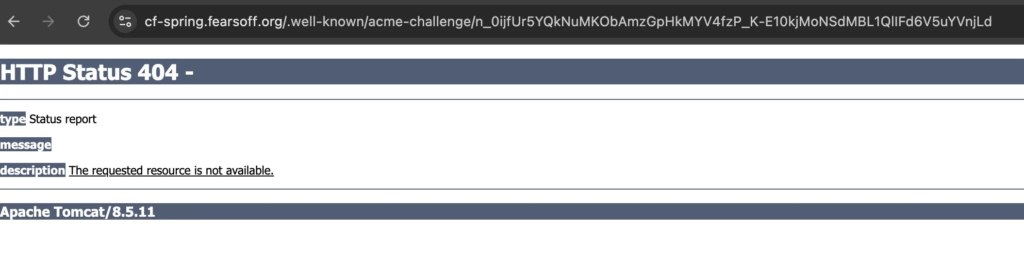
During testing, FearsOff observed that WAF rules were completely ignored for requests targeting the ACME challenge path. Instead of receiving Cloudflare block pages, these requests were forwarded directly to the origin servers, which responded with application-generated errors such as framework-level 404 pages.
To rule out misconfiguration, the researchers set up controlled test environments using PHP, Spring, and Next.js frameworks. Standard requests were correctly blocked, but ACME path requests consistently reached the backend applications.
The root cause was traced to Cloudflare’s edge logic for handling ACME HTTP-01 challenges. To prevent certificate issuance failures, Cloudflare temporarily disables certain security features when serving validation tokens for its managed certificates. However, a logic error caused WAF evaluation to be skipped entirely when the requested token did not match an active Cloudflare-managed certificate order.
As a result, a narrowly scoped exception intended for certificate validation became a universal bypass affecting all hosts behind Cloudflare protection.
Security Impact
The bypass enabled several real-world attack scenarios. On Spring and Tomcat applications, attackers could exploit servlet path traversal techniques to access sensitive actuator endpoints, exposing environment variables, database credentials, API keys, and cloud secrets.
Next.js applications running server-side rendering leaked internal operational data that was never meant to be publicly accessible. PHP applications with local file inclusion flaws became directly exploitable, allowing attackers to read files from the server’s filesystem.
In addition, account-level WAF rules that relied on custom headers for access control were completely ignored when requests were made through the ACME challenge path.
Disclosure and Fix
FearsOff responsibly reported the vulnerability through Cloudflare’s HackerOne bug bounty program on October 9, 2025. Cloudflare validated the issue within days and deployed a permanent fix on October 27, 2025.
The fix ensures that security features are disabled only when a request matches a valid ACME HTTP-01 challenge token for the specific hostname. All other requests, including those to the ACME path, are now subject to full WAF evaluation.
Cloudflare has confirmed that no customer action is required and stated that there is no evidence the flaw was exploited maliciously prior to the fix.
Why It Matters
This incident highlights how small logic exceptions in infrastructure-level services can undermine otherwise strong security guarantees. It also reinforces the importance of treating certificate management paths as sensitive attack surfaces, rather than assuming they are safe by default.
Organizations relying on managed security platforms should continue to monitor vendor advisories closely and recognize that even trusted control paths can become vectors for high-impact bypasses when architectural assumptions fail.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


