Security researchers have disclosed high-severity vulnerabilities in the popular open-source AI framework Chainlit that could allow attackers to steal sensitive data and potentially move laterally inside affected environments.
The issues were identified by Zafran Security and collectively named ChainLeak. According to the researchers, the flaws can be abused to leak cloud API keys, access sensitive server files, and perform server-side request forgery (SSRF) attacks against internal services hosting AI applications.
Chainlit is widely used to build conversational AI chatbots. Data from the Python Software Foundation shows the framework has been downloaded more than 220,000 times in a single week, with total downloads exceeding 7.3 million, highlighting the potential impact of the flaws.
Vulnerability Details
The two vulnerabilities affect the /project/element update flow and are tracked as follows:
CVE-2026-22218 (CVSS 7.1)
An arbitrary file read vulnerability that allows an authenticated attacker to access any file readable by the Chainlit service. The issue stems from missing validation of user-controlled fields, enabling attackers to read sensitive files into their own session.
CVE-2026-22219 (CVSS 8.3)
An SSRF vulnerability that occurs when Chainlit is configured with the SQLAlchemy data layer backend. It allows attackers to make arbitrary HTTP requests from the Chainlit server to internal services or cloud metadata endpoints and store the responses.
Zafran researchers Gal Zaban and Ido Shani warned that these two issues can be chained together to escalate privileges and compromise entire environments.
“Once an attacker gains arbitrary file read access on the server, the AI application’s security quickly begins to collapse,” the researchers said. “What initially looks like a limited flaw can become direct access to secrets and internal state.”
Real-World Impact
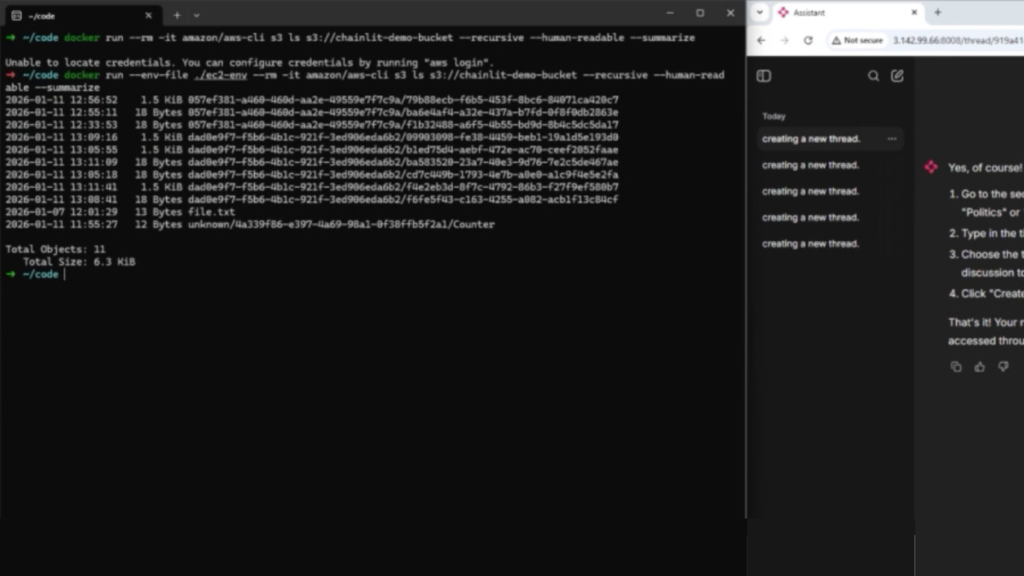
Using CVE-2026-22218, an attacker could read /proc/self/environ to extract environment variables containing API keys, credentials, and internal paths. In deployments using SQLAlchemy with an SQLite backend, database files could also be exposed.
When combined with CVE-2026-22219, the risk increases further. If Chainlit runs on an AWS EC2 instance with IMDSv1 enabled, attackers could exploit the SSRF flaw to query the metadata service at 169.254.169.254, retrieve role credentials, and move laterally within the cloud environment.

Patch and Mitigation
The vulnerabilities were responsibly disclosed on November 23, 2025, and fixed in Chainlit version 2.9.4, released on December 24, 2025. Users are strongly advised to upgrade immediately.
Zafran emphasized that as AI frameworks become core infrastructure, traditional software vulnerabilities are increasingly embedded directly into AI systems, often introducing poorly understood attack surfaces.
Related Disclosure: Microsoft MarkItDown MCP Server
The Chainlit findings coincide with a separate disclosure by BlueRock involving an SSRF flaw in Microsoft’s MarkItDown Model Context Protocol (MCP) server, dubbed MCP fURI.
The vulnerability allows attackers to supply arbitrary URIs to the convert_to_markdown tool, enabling access to HTTP and file resources without restriction. When running on AWS EC2 with IMDSv1, attackers could query instance metadata, obtain role credentials, and gain access to the AWS account.
BlueRock’s analysis of over 7,000 MCP servers found that 36.7% may be exposed to similar SSRF risks.
Recommended mitigations include migrating to IMDSv2, blocking private IP access, restricting metadata service access, and enforcing strict allowlists to prevent data exfiltration.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.