Recorded Future’s Insikt Group has uncovered that the North Korean-linked PurpleBravo campaign targeted 3,136 IP addresses connected to potential victims across multiple industries, including artificial intelligence, cryptocurrency, financial services, IT services, marketing, and software development.
The campaign, also known under aliases such as CL-STA-0240, DeceptiveDevelopment, DEV#POPPER, Famous Chollima, Gwisin Gang, Tenacious Pungsan, UNC5342, Void Dokkaebi, and WaterPlum, has been active since late 2023 and operated across Europe, South Asia, the Middle East, and Central America.
Scope of the Campaign
The identified IP addresses are primarily concentrated in South Asia and North America. The 20 affected organizations are based in:
- Belgium, Bulgaria, Costa Rica, India, Italy, Netherlands, Pakistan, Romania, U.A.E., Vietnam
“Job-seeking candidates in several cases executed malicious code on corporate devices, creating organizational exposure beyond the individual target,” the report stated.

Attack Methods
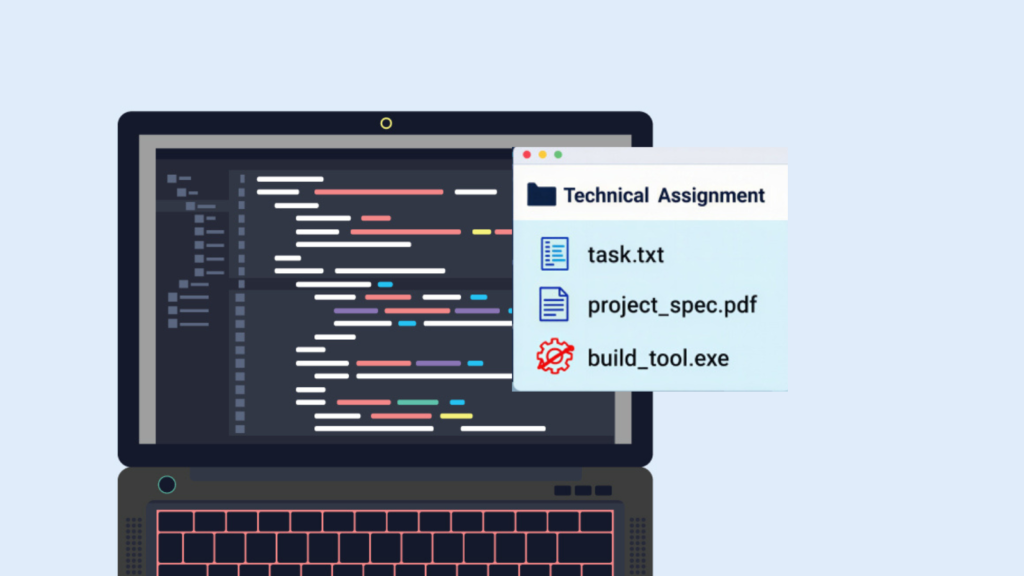
PurpleBravo has abused trusted developer workflows to achieve cyber espionage and financial theft. Recent activity involves:
- Malicious Microsoft Visual Studio Code (VS Code) projects used as backdoor delivery vectors
- Fake LinkedIn personas claiming to be developers or recruiters from Odesa, Ukraine
- Multiple malicious GitHub repositories delivering malware families such as BeaverTail
The threat actors also operate two distinct sets of command-and-control (C2) servers:
- BeaverTail – a JavaScript infostealer and loader
- GolangGhost / FlexibleFerret / WeaselStore – a Go-based backdoor leveraging HackBrowserData
C2 infrastructure is hosted across 17 providers and administered via Astrill VPN, with IP ranges traced to China.
Supply-Chain Risk and Broader Context
PurpleBravo activities overlap with another North Korean campaign, Wagemole (aka PurpleDelta), where actors seek unauthorized IT employment under stolen identities. Despite being separate operations, both campaigns share infrastructure, VPN usage, and operational tactics.
A critical observation is that job candidates approached with fictitious offers often complete coding assessments on company-issued devices, inadvertently compromising their employers. This highlights the supply-chain risk posed by North Korean IT threats to organizations handling outsourced work or maintaining large customer bases.
“While the North Korean IT worker employment threat has been widely publicized, the PurpleBravo supply-chain risk deserves equal attention so organizations can prepare, defend, and prevent sensitive data leakage to North Korean threat actors,” Recorded Future emphasized.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.