A newly discovered security vulnerability in SmarterTools SmarterMail email software is being actively exploited in real world attacks only two days after a fix was released. The rapid exploitation has raised concerns about patch awareness, disclosure practices, and the exposure of email infrastructure to credential takeover and remote code execution.
Authentication Bypass Identified and Patched
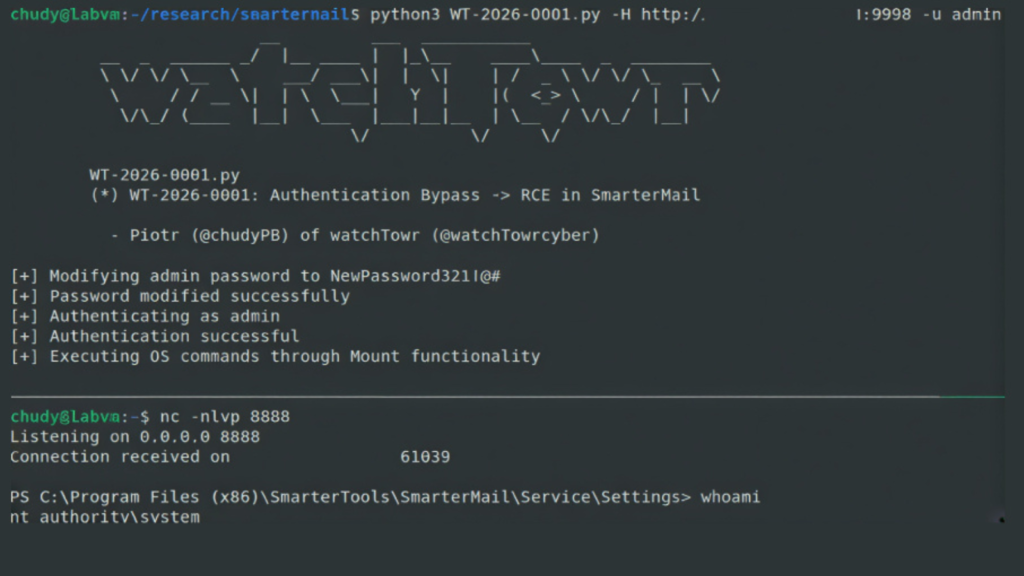
The flaw, initially without a CVE identifier, was tracked by watchTowr Labs as WT-2026-0001. SmarterTools released a fix on January 15, 2026, with Build 9511, following responsible disclosure by watchTowr Labs on January 8, 2026.
The issue allows an authentication bypass that enables any user to reset the SmarterMail system administrator password. This can be done by sending a specially crafted HTTP request to the /api/v1/auth/force-reset-password endpoint.
Researchers Piotr Bazydlo and Sina Kheirkhah from watchTowr Labs explained that the vulnerability is particularly dangerous because the compromised administrator account can use built in features to execute operating system commands directly on the host system.
Root Cause and Exploitation Logic
The flaw resides in the function SmarterMail.Web.Api.AuthenticationController.ForceResetPassword. The endpoint is accessible without authentication and relies on a boolean flag named IsSysAdmin to determine how the request is processed.
When the IsSysAdmin flag is set to true, the application logic performs several actions in sequence:
It retrieves the configuration for the supplied username
It creates a new system administrator entry using the provided password
It updates the existing administrator account with the new password
This design flaw allows an attacker to reset an administrator password simply by knowing a valid admin username and crafting a malicious HTTP request. No meaningful security controls prevent this privileged operation.
Direct Path to Remote Code Execution
The authentication bypass also enables full remote code execution. Once administrative access is obtained, attackers can execute operating system commands using built in SmarterMail functionality.
This can be achieved by navigating to the Settings section, creating a new storage volume, and entering an arbitrary command into the Volume Mount Command field. The command is then executed by the underlying operating system, resulting in a SYSTEM level shell.
Evidence of Active Exploitation
watchTowr Labs decided to publicly disclose the issue after a post appeared on the SmarterTools Community Portal. A user reported losing access to their administrator account, with logs showing that the force reset password endpoint was used on January 17, 2026, only two days after the patch was released.
This strongly suggests that attackers reverse engineered the patch to identify and weaponize the vulnerability. The situation was worsened by vague release notes for Build 9511, which only referenced “IMPORTANT: Critical security fixes” without technical detail.
Vendor Response and Transparency Concerns
SmarterTools CEO Tim Uzzanti addressed customer concerns by stating that limited disclosure in release notes is intended to reduce the risk of giving attackers actionable information. He also announced a policy change to notify customers by email whenever a new CVE is discovered and again when a fix is released.
Uzzanti noted that in more than 23 years, SmarterTools has dealt with only a small number of CVEs, which were historically communicated through release notes and critical fix references. It remains unclear whether SmarterMail administrators received such an email notification for this issue.
SmarterTools has been contacted for further comment, and updates are expected if a response is provided.
CVE Assignment and Additional Findings
Following publication, the vulnerability was assigned CVE-2026-23760 with a CVSS score of 9.3. Huntress confirmed that it has observed active exploitation of the privileged account takeover flaw, which can lead directly to remote code execution.
Huntress also reported that a previous critical SmarterMail vulnerability, CVE-2025-52691 with a CVSS score of 10.0, is now under mass exploitation. Attackers are using it to deploy basic web shells and suspected malware loaders written to startup directories to maintain persistence after system reboots.
According to Huntress, all IP addresses exploiting CVE-2026-23760 appear to be associated with virtual infrastructure located in the United States, although the true origin of the attacks remains unknown. There is currently no evidence linking either vulnerability to a specific threat actor.
Urgent Mitigation Advice
Given the severity of CVE-2026-23760, confirmed active exploitation, and parallel abuse of CVE-2025-52691, organizations are strongly urged to update SmarterMail to the latest available version immediately. Security teams should also review older deployments for indicators of compromise and unauthorized administrative changes.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.