North Korea-linked threat actor Konni has been observed launching a new cyber campaign that uses an AI-generated PowerShell backdoor to target blockchain developers and engineering teams. The operation highlights an increasing use of artificial intelligence to accelerate malware development while maintaining stealth.
According to Check Point Research, the phishing activity has targeted organizations and individuals in Japan, Australia, and India. This marks a notable expansion beyond Konni’s traditional focus areas, which previously included South Korea, Russia, Ukraine, and several European countries.
Konni has been active since at least 2014 and is primarily known for cyber espionage operations aligned with North Korean interests. The group is also tracked under multiple aliases, including Earth Imp, Opal Sleet, Osmium, TA406, and Vedalia.
Escalation in Tradecraft and Delivery Techniques
In November 2025, the Genians Security Center (GSC) reported that Konni had begun exploiting Google’s asset tracking service, Find Hub, to remotely reset Android devices and wipe user data. This development signaled a significant escalation in the group’s operational capabilities.
More recently, Konni has been distributing spear-phishing emails that contain malicious links disguised as legitimate advertising URLs associated with Google and Naver advertising platforms. This technique allows the attackers to bypass email security controls and deliver a remote access trojan known as EndRAT.
The campaign, dubbed Operation Poseidon by GSC, impersonates North Korean human rights organizations and South Korean financial institutions. Poorly secured WordPress websites are used both to host malicious files and to act as command-and-control infrastructure.
Phishing Lures and Malware Execution Chain
The phishing emails are designed to resemble financial notifications such as transaction confirmations or wire transfer requests. Victims are tricked into downloading ZIP archives hosted on compromised WordPress sites.
Each ZIP file contains a Windows shortcut (LNK) file that executes an AutoIt script disguised as a PDF document. This script delivers EndRAT, also known as EndClient RAT.
South Korean researchers noted that the campaign successfully evaded both email filtering systems and user awareness by abusing legitimate advertising redirection mechanisms within the Google ad ecosystem, including the use of ad.doubleclick[.]net redirect structures.
AI-Generated PowerShell Backdoor Targeting Developers
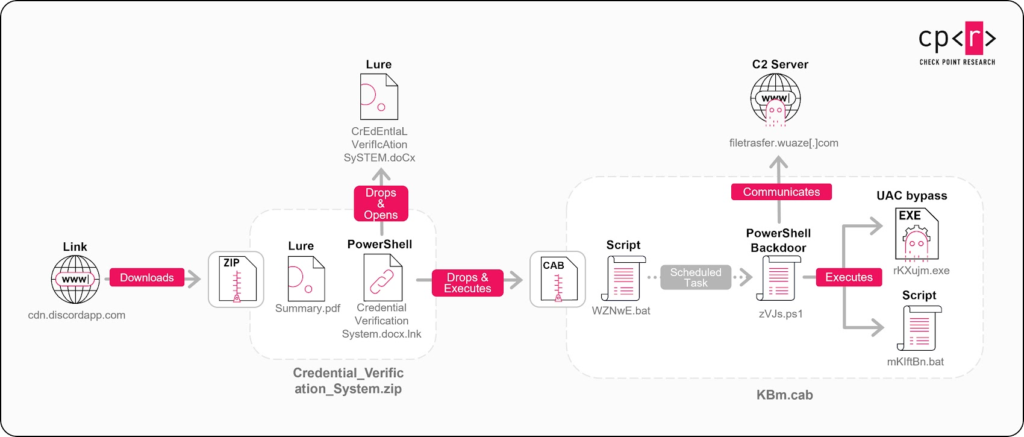
A separate campaign documented by Check Point reveals a more advanced attack chain aimed at blockchain developers. In this case, ZIP archives masquerading as project requirement documents are hosted on Discord’s content delivery network.
The ZIP file includes a decoy PDF and an LNK file that launches an embedded PowerShell loader. The loader drops a Microsoft Word lure document and a CAB archive while displaying the Word file as a distraction.
The CAB archive contains a PowerShell backdoor, two batch scripts, and an executable used for User Account Control bypass. The malware establishes persistence through scheduled tasks, performs anti-analysis checks, attempts privilege escalation using the FodHelper technique, and configures Microsoft Defender exclusions. It ultimately deploys SimpleHelp, a legitimate remote management tool, to maintain long-term access.
Check Point researchers believe the PowerShell backdoor was created with the assistance of AI tools, citing its modular design, clear documentation, and human-readable source code comments.
Instead of targeting individual users, the attackers appear focused on compromising development environments, where access can cascade across multiple projects and services. The use of AI-assisted tooling suggests an effort to streamline development while relying on established social engineering tactics.
Broader North Korea-Linked Campaigns
The findings align with other North Korea-attributed operations uncovered in recent months, including phishing campaigns that deploy MoonPeak malware, attacks using Visual Studio Code tunnels for remote access, and supply chain compromises delivering malware families such as TigerRAT, StarshellRAT, JelusRAT, and GopherRAT.
Researchers note that Konni and related groups have demonstrated flexible objectives over time, ranging from financial theft to intelligence collection, adapting their tactics to support shifting strategic priorities.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


