Cybersecurity researchers have identified an active phishing campaign targeting users in India as part of a suspected cyber espionage operation. The campaign delivers a multi-stage backdoor designed to provide long-term access, continuous surveillance, and data exfiltration from infected systems.
According to the eSentire Threat Response Unit (TRU), the attackers are distributing phishing emails that impersonate the Income Tax Department of India. These emails attempt to lure recipients into downloading a malicious ZIP archive by presenting it as an official tax penalty or inspection notice.
Multi-Stage Infection Chain
Once opened, the ZIP archive reveals multiple hidden files, with only one visible executable named “Inspection Document Review.exe.” This executable is used to sideload a malicious DLL embedded within the archive. The DLL performs anti-debugging checks and contacts an external server to retrieve the next stage of the attack.
The downloaded shellcode uses a Component Object Model based technique to bypass User Account Control prompts and gain administrative privileges. To evade detection, the malware alters its own Process Environment Block to disguise itself as the legitimate Windows “explorer.exe” process.
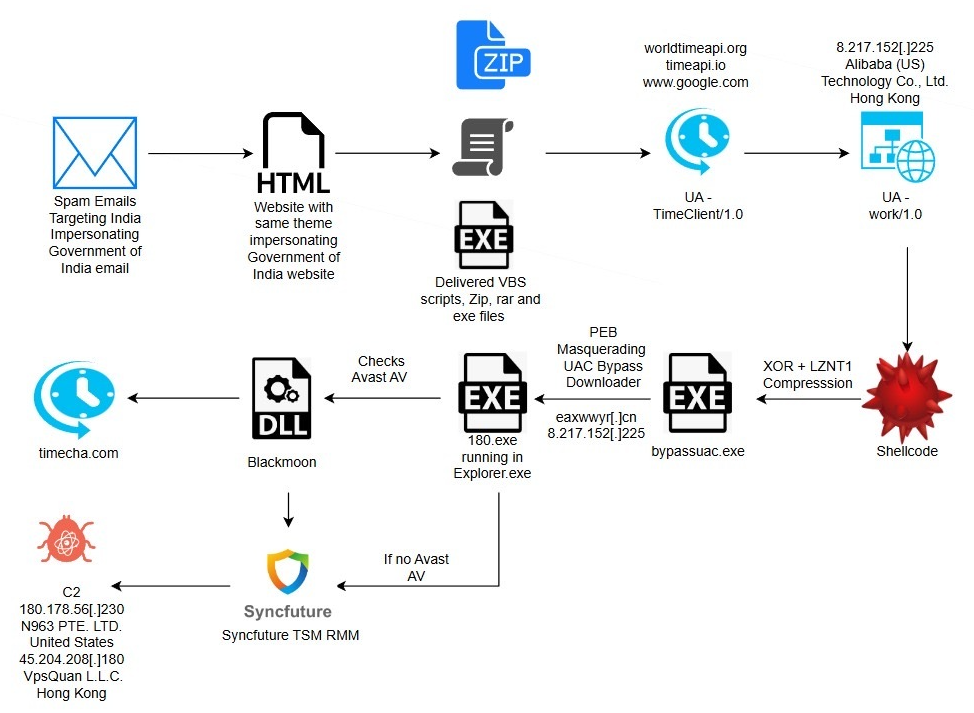
The attack then retrieves an additional payload named “180.exe” from the domain eaxwwyr[.]cn. This file is a 32-bit Inno Setup installer that dynamically adjusts its behavior based on the presence of Avast Free Antivirus on the compromised system.
Antivirus Evasion and Blackmoon Deployment
If Avast is detected, the malware simulates mouse movements to navigate the antivirus interface and silently add malicious files to the exclusion list without disabling the security software. This behavior is linked to a DLL assessed to be a variant of the Blackmoon banking trojan, also known as KRBanker.
Blackmoon has previously been associated with attacks against organizations in South Korea, the United States, and Canada, with its earliest sightings dating back to September 2015.
Abuse of Legitimate Enterprise Software
One of the files excluded from antivirus scanning is “Setup.exe,” a legitimate utility from SyncFutureTec Company Limited. This program drops another executable, “mysetup.exe,” which researchers assess to be SyncFuture TSM, a commercial Terminal Security Management tool developed by Nanjing Zhongke Huasai Technology Co., Ltd.
By repurposing this legitimate enterprise tool, the attackers gain powerful remote monitoring and management capabilities. These include remote system control, detailed user activity logging, and centralized data theft operations.
Additional components deployed during the infection include batch scripts that create custom directories, modify access control lists, alter desktop permissions, and perform cleanup operations. An executable named “MANC.exe” coordinates multiple services and enables extensive system logging.
Security researchers noted that the campaign demonstrates a high level of technical sophistication by combining anti-analysis techniques, privilege escalation, DLL sideloading, commercial tool abuse, and antivirus evasion. While no specific threat actor has been formally attributed to the activity, the overall tradecraft indicates deliberate espionage-oriented objectives.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.