Cybersecurity researchers have uncovered two previously undocumented cyber campaigns targeting Indian government entities, attributed to a threat actor believed to be operating from Pakistan.
The campaigns, identified by Zscaler ThreatLabz in September 2025, have been named Gopher Strike and Sheet Attack. According to researchers Sudeep Singh and Yin Hong Chang, the operations show overlaps with known Pakistan-linked APT activity, particularly APT36. However, analysts assess with medium confidence that the observed behavior may belong to a new subgroup or a separate threat actor operating alongside known entities.
Use of Trusted Platforms for Command and Control
The Sheet Attack campaign is characterized by its abuse of legitimate cloud services such as Google Sheets, Firebase, and email infrastructure for command-and-control communication. By blending malicious traffic into trusted platforms, the attackers significantly reduce the likelihood of detection.
In contrast, Gopher Strike relies on carefully crafted phishing emails to initiate infection. These emails deliver PDF files that display a blurred document overlaid with a fake pop-up message urging recipients to install an update for Adobe Acrobat Reader DC.
Targeted Payload Delivery Through Server-Side Filtering
The embedded fake update prompt includes a “Download and Install” button. When clicked, it triggers the download of a malicious ISO file, but only if two conditions are met. The request must originate from an IP address located in India, and the User-Agent must indicate a Windows operating system.
Zscaler notes that these server-side checks are designed to block automated analysis tools, ensuring the malware is delivered exclusively to intended victims.
GOGITTER Downloader and Persistent Access
The ISO file contains a Golang-based downloader dubbed GOGITTER. Once executed, it checks for the existence of a Visual Basic Script file in several locations, including public user folders and the AppData directory. If absent, the script is created and configured to fetch new commands from two hard-coded command-and-control servers every 30 seconds.
To maintain persistence, GOGITTER creates a scheduled task that executes the VBScript every 50 minutes. The malware also searches for a ZIP archive named adobe_update.zip in the same directories. If the archive is missing, it is downloaded from a private GitHub repository located at github[.]com/jaishankai/sockv6, an account created in June 2025.
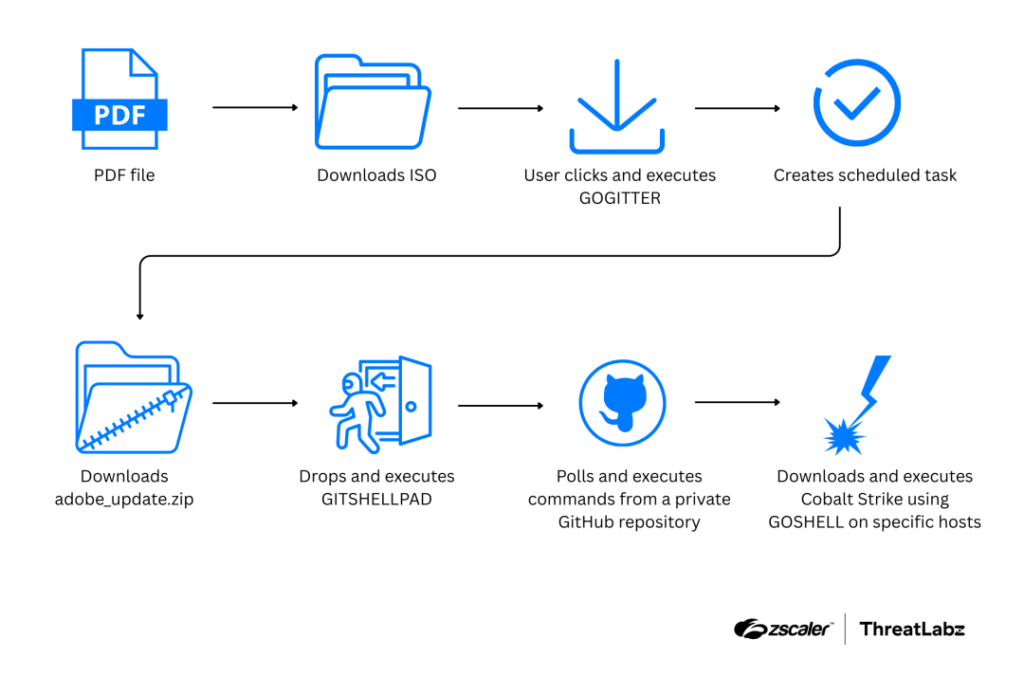
After successful execution, the malware sends a beacon request to the domain adobe-acrobat[.]in, likely signaling successful infection. The ZIP archive is then extracted, and an executable named edgehost.exe is launched.
GitHub-Based Backdoor Operations
The executed payload deploys GITSHELLPAD, a lightweight Golang backdoor that uses private GitHub repositories for command-and-control. The backdoor polls a file named command.txt every 15 seconds to retrieve instructions from the attackers.
Supported commands include directory navigation, background command execution, file uploads and downloads, and command execution with output capture. Execution results are saved to result.txt and uploaded back to the GitHub repository. Once completed, the command file is removed to limit forensic traces.
Deployment of Cobalt Strike via GOSHELL
Zscaler also observed the attackers downloading RAR archives using cURL after initial access. These archives contain system reconnaissance tools and a custom Golang loader named GOSHELL, which ultimately deploys Cobalt Strike Beacon after multiple decoding stages.
To evade antivirus detection, GOSHELL’s executable size is artificially inflated to nearly one gigabyte by inserting junk data into the PE overlay. Additionally, the loader executes only on systems with hostnames that match a hard-coded allowlist. All auxiliary tools are removed from the system after use to reduce visibility.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


