A severe security vulnerability has been identified in Grist-Core, the open-source self-hosted variant of the Grist relational spreadsheet-database, which could allow remote code execution (RCE).
The flaw, cataloged as CVE-2026-24002 with a CVSS score of 9.1, has been dubbed Cellbreak by Cyera Research Labs.
“One malicious formula can turn a spreadsheet into a Remote Code Execution (RCE) beachhead,” said security researcher Vladimir Tokarev, who discovered the issue. “This sandbox escape allows formula authors to execute OS commands or host-runtime JavaScript, blurring the line between ‘cell logic’ and host execution.”
Cellbreak is a Pyodide sandbox escape, similar to the vulnerability that affected n8n (CVE-2025-68668, CVSS score: 9.9, aka N8scape). The flaw has been patched in Grist version 1.7.9, released on January 9, 2026.
According to Grist maintainers, “A security review identified a vulnerability in the Pyodide sandboxing method used in Grist. Check your Admin Panel under the sandboxing section. If it displays ‘gvisor,’ your instance is safe. If it shows ‘pyodide,’ you should upgrade immediately.”
The root cause lies in Grist’s Python formula execution, which runs untrusted formulas inside Pyodide, a Python distribution that executes code directly in the browser using WebAssembly (WASM). While this is intended to isolate code, the blocklist-based approach enables attackers to escape the sandbox and execute commands on the host server.
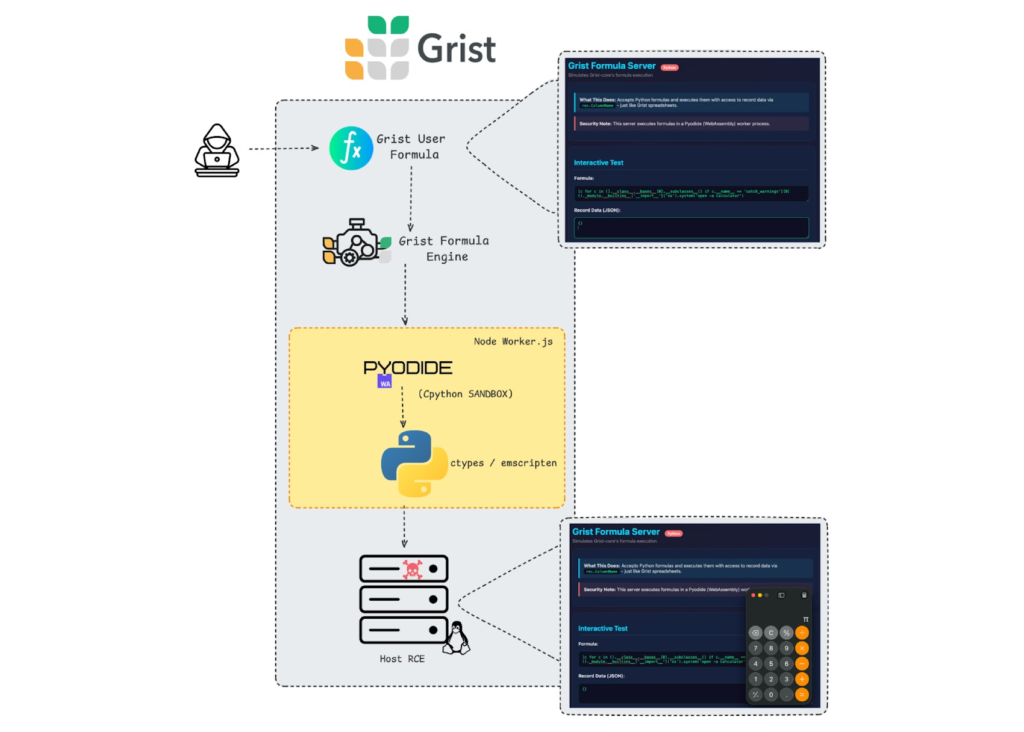
Tokarev explained, “The sandbox design allows traversal through Python’s class hierarchy and exposes ctypes, providing access to Emscripten runtime functions that should never be reachable from a formula. This allows host command execution, JavaScript execution in the host runtime, filesystem access, and exposure of sensitive data.”
When GRIST_SANDBOX_FLAVOR is set to Pyodide, opening a malicious spreadsheet could allow attackers to execute arbitrary processes, retrieve database credentials, read sensitive files, and exploit lateral movement opportunities.
Grist has mitigated the issue by defaulting Pyodide formula execution to the Deno JavaScript runtime. However, operators who explicitly set GRIST_PYODIDE_SKIP_DENO=1 reintroduce the risk.
Recommended actions for users:
- Update to the latest Grist version (1.7.9 or later)
- For temporary mitigation, set GRIST_SANDBOX_FLAVOR=gvisor
Tokarev emphasized, “A single sandbox escape can turn data logic into host execution. Grist-Core demonstrates why sandboxing must be capability-based and defense-in-depth, rather than relying on fragile blocklists. The cost of failure is a data-plane breach, not just a bug.”
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


