Google has announced the disruption of IPIDEA, widely recognized as one of the largest residential proxy networks in operation. The takedown involved legal actions to seize dozens of domains used to control infected devices and route proxy traffic, rendering IPIDEA’s main website (www.ipidea.io) inaccessible.
IPIDEA previously promoted itself as a leading IP proxy provider, claiming over 6.1 million daily updated IP addresses and 69,000 new IP addresses each day.
“Residential proxy networks have become a pervasive tool for everything from espionage to large-scale cybercrime,” said John Hultquist, chief analyst at Google Threat Intelligence Group (GTIG).
“By routing traffic through consumers’ home internet connections, attackers can hide in plain sight while infiltrating corporate networks. Taking down IPIDEA disrupted a global marketplace selling access to millions of hijacked devices.”
Global Threat Actor Usage
According to GTIG, as of January 2026, over 550 threat groups were leveraging IPIDEA’s infrastructure, spanning motivations from cybercrime and APT operations to information operations. Adversaries from China, North Korea, Iran, and Russia were reported exploiting the network for activities including SaaS account attacks, on-premises intrusions, and password spraying.
In a separate analysis, Synthient revealed that malware distributed via residential proxies like IPIDEA was being used by the AISURU/Kimwolf botnet to control IoT devices behind firewalls. Many infected devices were off-brand Android TV boxes with pre-installed apps or games containing proxy-enabling malware. Users were sometimes lured by advertisements promising “easy cash” for sharing unused bandwidth.
How IPIDEA Operated
GTIG explains that residential proxy networks require code on consumer devices to enroll them as exit nodes. Devices may either be preloaded with proxy software or compromised when users install trojanized applications. In some cases, users knowingly installed proxy-enabled apps for passive income.
IPIDEA also became linked to several botnets, including China-based BADBOX 2.0. In July 2025, Google filed a lawsuit against 25 unnamed individuals or entities in China for operating the botnet and associated proxy infrastructure.
The network was not a single entity but a collection of proxy brands under a single operator’s control:
- Ipidea (ipidea[.]io)
- 360 Proxy (360proxy[.]com)
- 922 Proxy (922proxy[.]com)
- ABC Proxy (abcproxy[.]com)
- Cherry Proxy (cherryproxy[.]com)
- Door VPN (doorvpn[.]com)
- Galleon VPN (galleonvpn[.]com)
- IP 2 World (ip2world[.]com)
- Luna Proxy (lunaproxy[.]com)
- PIA S5 Proxy (piaproxy[.]com)
- PY Proxy (pyproxy[.]com)
- Radish VPN (radishvpn[.]com)
- Tab Proxy (tabproxy[.]com)
SDKs and Monetization Model
Operators of IPIDEA also controlled SDKs designed for developers to integrate into Android, Windows, iOS, and WebOS apps. When embedded, these SDKs transformed user devices into proxy nodes while maintaining app functionality. Key SDKs included:
- Castar SDK (castarsdk[.]com)
- Earn SDK (earnsdk[.]io)
- Hex SDK (hexsdk[.]com)
- Packet SDK (packetsdk[.]com)
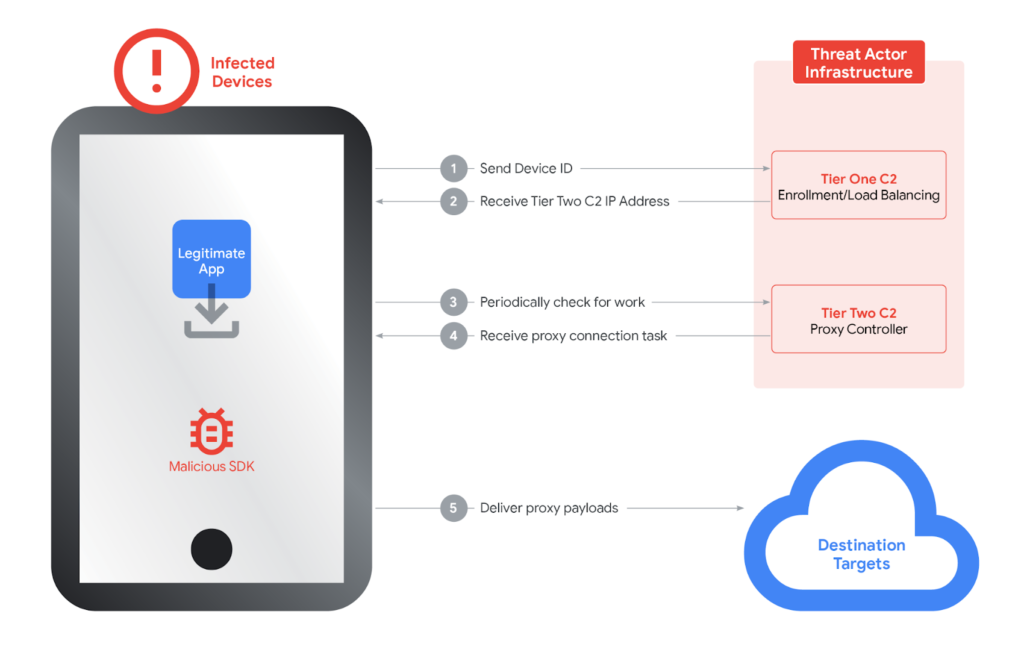
These SDKs shared command-and-control infrastructure, using a two-tier system where infected devices first contact a Tier One server to obtain Tier Two nodes for proxying traffic. Google identified around 7,400 Tier Two servers associated with the network.
VPNs and Trojanized Applications
Some free VPN services, including Galleon VPN, Radish VPN, and Aman VPN (defunct), were also leveraged to join the proxy network through Hex or Packet SDKs. Analysis revealed 3,075 unique Windows binaries and over 600 Android apps had communicated with Tier One domains, some masquerading as legitimate software like OneDriveSync or Windows Update.
Industry Response and Mitigation
A spokesperson for IPIDEA’s parent company claimed that its growth strategy had been “relatively aggressive” and acknowledged some promotional activity in questionable venues, but denied involvement in illegal conduct.
To counter the threat, Google has updated Google Play Protect to warn users about apps containing IPIDEA code. Certified Android devices will automatically remove malicious apps and block future installations.
“Even when proxy providers claim ignorance or patch vulnerabilities, enforcement is difficult due to murky ownership, reseller agreements, and the diversity of affected applications,” GTIG said.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


