Cybersecurity researchers have uncovered a new malicious campaign attributed to a China linked threat actor tracked as UAT 8099. The activity, observed between late 2025 and early 2026, targeted vulnerable Microsoft Internet Information Services servers across multiple Asian countries.
The campaign was identified by Cisco Talos, which reported that the attacks primarily focused on IIS servers in Thailand and Vietnam, although affected systems were also found in India, Pakistan, and Japan. The full scale of the operation has not yet been determined.
According to Talos researcher Joey Chen, the threat actor relied on web shells and PowerShell scripts to deploy additional tools, including GotoHTTP, enabling persistent remote access to compromised IIS servers.
Previous Activity and Attribution Assessment
UAT 8099 was first documented by Cisco Talos in October 2025. At that time, the group was linked to attacks against IIS servers in countries including India, Thailand, Vietnam, Canada, and Brazil. Those earlier intrusions were associated with search engine optimization fraud campaigns carried out through malware known as BadIIS.
The threat cluster is believed to be of Chinese origin, with activity traced back to at least April 2025. Researchers also noted overlaps with a separate BadIIS campaign named WEBJACK, previously reported by WithSecure in November 2025. Shared tooling, command and control infrastructure, and victim targeting patterns support the connection.
Shift in Tactics and Regional Focus
The latest campaign demonstrates a noticeable evolution in operational strategy. While the group continues to use web shells, SoftEther VPN, and EasyTier to manage infected servers, Cisco Talos observed a stronger regional focus, particularly on Southeast Asia.
Researchers also noted increased use of red team tools and legitimate utilities, which helps the attackers evade detection and maintain long term persistence on compromised systems.
Attack Chain and Tool Deployment
The intrusion process typically begins with UAT 8099 gaining access to an IIS server by exploiting known vulnerabilities or misconfigured file upload features. Once inside, the attackers perform a series of actions to establish control and deploy malware:
- System discovery and reconnaissance commands to collect host information
- Deployment of VPN tools and creation of a hidden user account named admin$ to maintain persistence
- Installation of tools such as Sharp4RemoveLog to erase Windows event logs, CnCrypt Protect to conceal malicious files, OpenArk64 to disable security processes, and GotoHTTP for remote server control
- Deployment of the BadIIS malware using the newly created account
As security products increasingly detect the admin$ account, the threat actor introduced additional checks. If the account name is blocked, the attackers create an alternative hidden account named mysql$. In some cases, multiple hidden accounts are established to ensure uninterrupted access.
Use of GotoHTTP for Remote Control
Another notable change in this campaign is the method used to launch GotoHTTP. The tool is executed through a Visual Basic Script that is downloaded via a PowerShell command after a web shell has been installed. This layered approach adds complexity and reduces the likelihood of detection.
Region Specific BadIIS Malware Variants
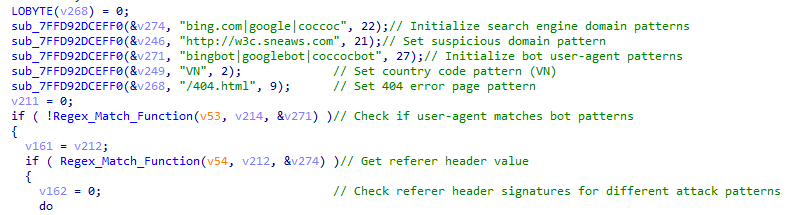
The attackers deployed two newly modified BadIIS variants designed for specific geographic targets. The BadIIS IISHijack variant primarily targets IIS servers in Vietnam, while the BadIIS asdSearchEngine variant focuses on systems in Thailand or users with Thai language settings.
The core objective remains SEO manipulation. The malware inspects incoming web requests to determine whether the visitor is a search engine crawler. If so, the crawler is redirected to SEO fraud websites. If the visitor is a regular user and the Accept Language header indicates Thai, the malware injects HTML content containing a malicious JavaScript redirect into the server response.
Multiple BadIIS asdSearchEngine Variants Identified
Cisco Talos identified three distinct variants within the BadIIS asdSearchEngine family:
- Multiple extension exclusion variant, which ignores requests containing certain file extensions to reduce performance impact and avoid visual disruption
- HTML template loading variant, which dynamically generates web pages using disk based or embedded templates filled with randomized content
- Dynamic page and directory index variant, which targets dynamic pages and directory indexes where SEO injections are most effective
Talos assessed that this selective targeting helps maximize SEO impact while minimizing suspicious server errors and log generation.
Ongoing Development and Linux Variant Updates
Researchers also observed signs that UAT 8099 is actively refining a Linux version of BadIIS. An ELF binary uploaded to VirusTotal in October 2025 included proxy, injector, and SEO fraud capabilities, while narrowing its focus to search engine crawlers from Google, Microsoft Bing, and Yahoo.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


