Threat actors with links to China have been connected to a new wave of cyber espionage operations aimed at government and law enforcement institutions across Southeast Asia during 2025.
Check Point Research has attributed the activity to a previously undocumented threat cluster named Amaranth-Dragon, which researchers say shows notable overlaps with the APT41 ecosystem. Countries targeted in these campaigns include Cambodia, Thailand, Laos, Indonesia, Singapore, and the Philippines.
According to Check Point, many of the observed operations were carefully timed around sensitive political moments, government decisions, and regional security developments. By aligning malicious lures with real world events familiar to their targets, the attackers increased the likelihood of engagement and successful compromise.
The company described the campaigns as narrowly focused and tightly controlled, suggesting a strategic objective centered on long term persistence and geopolitical intelligence gathering rather than large scale disruption.
A defining characteristic of Amaranth-Dragon’s operations is the emphasis on stealth. The attack infrastructure was configured to communicate only with victims located in specific target countries, significantly reducing exposure and detection outside the intended regions.
The attackers were observed exploiting CVE-2025-8088, a now patched vulnerability in RARLAB WinRAR that allows arbitrary code execution when specially crafted archive files are opened. Exploitation activity was detected approximately eight days after the vulnerability was publicly disclosed in August 2025.
Check Point researchers stated that the group distributed malicious RAR files designed to trigger the vulnerability, enabling arbitrary code execution and establishing persistence on infected systems. The speed with which the exploit was operationalized highlights the group’s technical readiness and maturity.
While the exact initial infection method has not been conclusively identified, the highly targeted nature of the campaigns and the use of context specific lures related to political, economic, and military developments strongly point to spear phishing emails. These emails likely delivered malicious archive files hosted on trusted cloud services such as Dropbox to reduce suspicion and bypass traditional security controls.
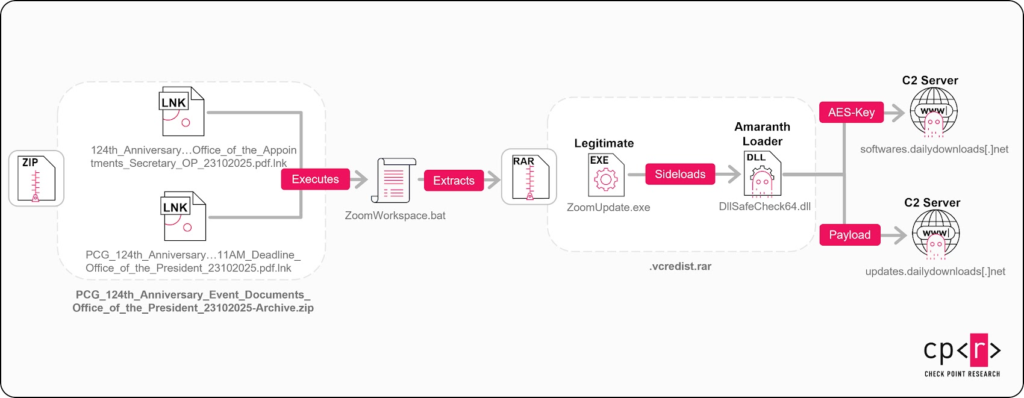
The malicious archive typically contains multiple files, including a harmful DLL known as Amaranth Loader, which is executed using DLL side loading, a technique frequently associated with Chinese threat actors. The loader shares similarities with tools like DodgeBox, DUSTPAN, also known as StealthVector, and DUSTTRAP, which have previously been linked to APT41 operations.
Check Point noted that Amaranth-Dragon’s connection to APT41 is supported by similarities in malware tooling, development patterns, and operational behavior. Chinese threat groups are known to share tools, techniques, and infrastructure, making such overlaps significant.
The researchers added that development practices, including executing malicious code through newly created threads inside export functions, closely resemble established APT41 methods. Compilation timestamps, campaign scheduling, and infrastructure management also suggest a disciplined and well resourced team operating within the UTC+8 time zone.
Mustang Panda Delivers New PlugX Variant in Parallel Campaign
The disclosure coincides with findings from Dream Research Labs, which uncovered a separate espionage campaign conducted by another China aligned group tracked as Mustang Panda. The campaign targeted individuals involved in diplomacy, elections, and international coordination between December 2025 and mid January 2026 and has been named PlugX Diplomacy.
According to the researchers, the operation did not rely on exploiting software vulnerabilities. Instead, it leveraged impersonation and trust by distributing files disguised as diplomatic summaries or policy documents linked to the United States. Simply opening the files was sufficient to initiate infection.
These documents ultimately led to the deployment of a customized PlugX malware variant called DOPLUGS, which has been observed in the wild since at least late December 2022. The malware enables covert data collection and long term persistence.
The attack chain typically begins with a malicious ZIP attachment themed around official meetings, elections, or international forums. Inside the archive is a single Windows shortcut file that launches a PowerShell command, which extracts and drops a TAR archive onto the system.
Dream Research Labs explained that the embedded PowerShell logic searches for the ZIP file, reads it as raw data, and extracts a payload from a fixed byte offset. The extracted data is written to disk using an obfuscated method and unpacked with the native tar.exe utility, demonstrating consistent abuse of living off the land binaries.
The TAR archive contains three components, a legitimate signed executable linked to AOMEI Backupper that is vulnerable to DLL search order hijacking, an encrypted data file holding the PlugX payload, and a malicious DLL that is side loaded to activate the malware.
When executed, the legitimate application displays a decoy PDF to the victim, masking the background installation of DOPLUGS on the compromised system.
Dream Research Labs concluded that the alignment between real diplomatic events and the timing of malicious lures indicates that similar campaigns are likely to continue as geopolitical tensions evolve. Organizations operating in government, diplomatic, and policy related sectors are advised to treat malicious LNK files and DLL hijacking through legitimate executables as persistent and high risk threats.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


