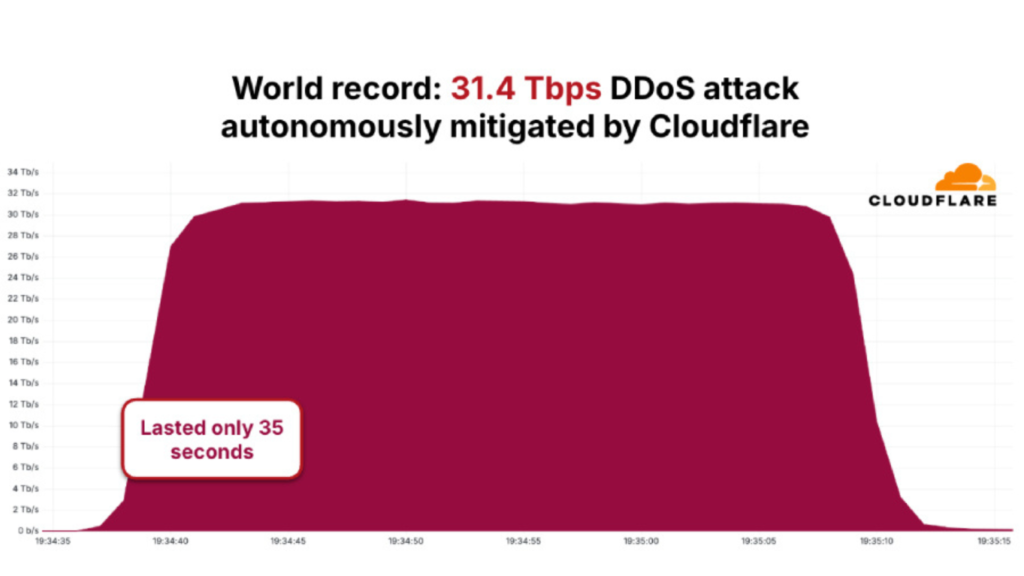
Cybersecurity researchers have attributed a record-breaking distributed denial-of-service attack to the AISURU and Kimwolf botnet, which generated traffic peaks of 31.4 terabits per second and lasted approximately 35 seconds, making it one of the largest DDoS attacks ever recorded.
Cloudflare confirmed that the attack occurred in November 2025 and was automatically detected and mitigated by its systems. The company said the incident is part of a wider surge in hyper-volumetric HTTP DDoS attacks observed throughout the fourth quarter of 2025.
Part of a Broader DDoS Surge in Late 2025
AISURU and Kimwolf have also been linked to a large-scale campaign tracked as “The Night Before Christmas,” which began on December 19, 2025. According to Cloudflare, attacks during this campaign averaged:
- 3 billion packets per second
- 4 terabits per second
- 54 million requests per second
At peak intensity, some attacks reached 9 billion packets per second, 24 terabits per second, and 205 million requests per second.
“DDoS attacks surged by 121 percent in 2025,” said Cloudflare researchers Omer Yoachimik and Jorge Pacheco. “On average, 5,376 attacks were automatically mitigated every hour. In total, 47.1 million DDoS attacks were recorded during the year.”
Network-Layer Attacks Dominate the Threat Landscape
Cloudflare reported mitigating 34.4 million network-layer DDoS attacks in 2025, a sharp increase from 11.4 million in 2024. In Q4 2025 alone, network-layer attacks accounted for 78 percent of all observed DDoS activity.
Overall, DDoS incidents rose:
- 31 percent compared to Q3 2025
- 58 percent compared to the full year of 2024
Hyper-volumetric attacks also climbed significantly, increasing from 1,304 incidents in Q3 2025 to 1,824 in Q4 2025. By comparison, only 717 such attacks were recorded in Q1 2025. The size of these attacks grew by more than 700 percent relative to late 2024.

Millions of Compromised Android Devices Power the Botnet
Researchers estimate that AISURU and Kimwolf control over 2 million Android devices, many of which are low-cost, off-brand Android TV systems. These devices are frequently routed through residential proxy networks, most notably IPIDEA, to disguise attack origins.
In January 2026, Google disrupted IPIDEA’s operations and initiated legal action to dismantle domains used for command-and-control and proxy traffic routing. Google also partnered with Cloudflare to block IPIDEA’s domain resolution, significantly impairing its infrastructure.
“As part of the Google-led disruption effort, Cloudflare suspended access to numerous accounts and domains abusing our services,” Cloudflare told The Hacker News. “These actors were distributing malware and offering access to illicit residential proxy networks.”
Trojanized Apps and Covert Proxy Enrollment
IPIDEA is believed to have compromised devices using:
- At least 600 trojanized Android applications embedding proxy SDKs
- More than 3,000 trojanized Windows binaries disguised as OneDriveSync tools or Windows updates
The Beijing-based operation also promoted VPN and proxy apps that silently converted Android devices into proxy exit nodes without user consent.
Investigators further noted that IPIDEA operates over a dozen residential proxy brands posing as legitimate services. Despite their different branding, all offerings connect back to a centralized backend infrastructure controlled by the same operators.
Most Targeted Sectors and Regions
Cloudflare identified several notable trends during Q4 2025:
- Telecommunications and service providers were the most targeted sector
- Other heavily targeted industries included IT services, gambling, gaming, and software
- The most attacked countries were China, Hong Kong, Germany, Brazil, the United States, the United Kingdom, Vietnam, Azerbaijan, India, and Singapore
On the source side, Bangladesh overtook Indonesia as the largest origin of DDoS traffic. Other major source countries included Ecuador, Argentina, Hong Kong, Ukraine, Vietnam, Taiwan, Singapore, and Peru.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.