Cybersecurity researchers at Palo Alto Networks Unit 42 have uncovered a previously unknown state-backed cyber espionage group that has compromised at least 70 government and critical infrastructure organizations across 37 countries within the last year.
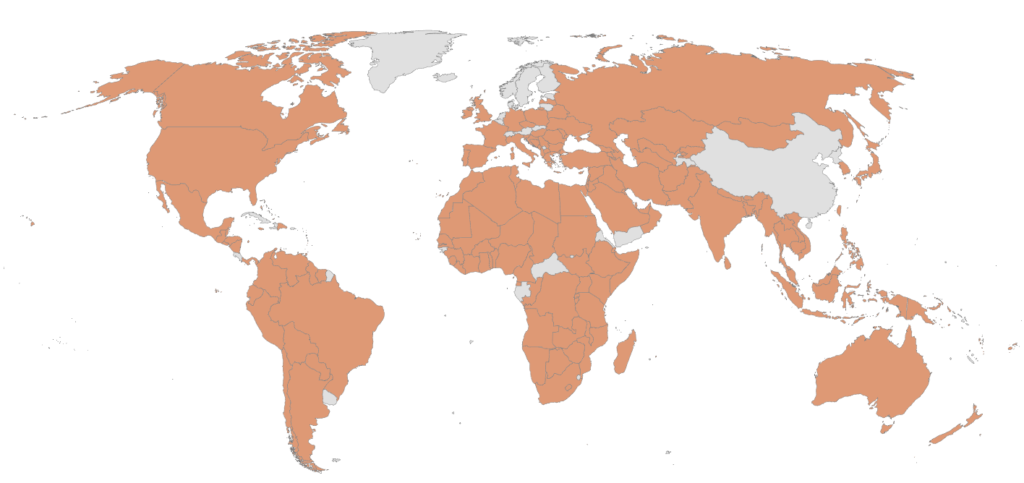
The threat actor, tracked as TGR-STA-1030, has also conducted widespread reconnaissance activities targeting government-related infrastructure in 155 countries between November and December 2025. The group appears to focus heavily on national security, economic policy, trade, diplomacy, and border control entities.
According to Unit 42, victims include multiple national law enforcement agencies, ministries of finance, and departments responsible for natural resources and international relations. Evidence suggests the group has been operational since early 2024.
Attribution and Operational Profile
While the attackers’ exact origin has not been officially confirmed, analysts assess the group to be of Asian origin. This assessment is based on several indicators, including regional infrastructure usage, language preferences, GMT+8 operational hours, and targeting patterns aligned with regional geopolitical interests.
Initial Access and Malware Delivery
The attack chain commonly begins with phishing emails that lure recipients into downloading a ZIP archive hosted on the New Zealand-based file-sharing service MEGA. The archive contains a malicious executable known as Diaoyu Loader, along with a zero-byte file named pic1.png.
Unit 42 reports that the malware uses a two-layer execution safeguard to evade automated sandbox detection. First, it checks whether the system has a horizontal screen resolution of at least 1440 pixels. Second, it verifies the presence of the pic1.png file in the same directory. If either condition fails, the malware terminates execution.
Before proceeding, the loader also checks for the presence of security products from vendors such as Avira, Bitdefender, Kaspersky, SentinelOne, and Symantec. The reason for focusing on this limited set of defenses remains unclear.
Payload Deployment and Tools
Once execution conditions are met, Diaoyu Loader retrieves three image files from a GitHub repository disguised as a WordPress project. These files are used to deliver a Cobalt Strike payload. The GitHub account associated with this activity has since been removed.
In addition to phishing, the group has attempted to exploit known vulnerabilities in widely used software platforms, including products from Microsoft, SAP, Atlassian, Ruijieyi Networks, Commvault, and Eyou Email System. Researchers found no evidence of zero-day exploits being used.
Advanced Tooling and Persistence
TGR-STA-1030 employs a broad arsenal of tools to maintain access and control over compromised networks. These include command-and-control frameworks such as Cobalt Strike, Sliver, Havoc, SparkRAT, and VShell, along with web shells like Behinder, Godzilla, and neo-reGeorg.
The group also uses tunneling tools such as GOST, FRPS, and IOX to move laterally and conceal traffic. Notably, researchers identified a Linux kernel rootkit named ShadowGuard, which leverages eBPF technology to hide processes, files, and directories labeled “swsecret” from standard system monitoring tools.
Long-Term Espionage Operations
Unit 42 observed that the attackers often retain access to compromised environments for extended periods, sometimes lasting several months. This persistence indicates a clear focus on long-term intelligence collection rather than short-term disruption.
The group frequently rents infrastructure from legitimate virtual private server providers and uses additional relay servers to mask connections to their command-and-control systems.
Global Security Implications
Researchers warn that TGR-STA-1030 remains an active and evolving threat, particularly to government ministries and organizations involved in strategic economic partnerships.
Although the campaign appears to be espionage-focused, its scale, persistence, and technical sophistication raise serious concerns for national security and the stability of critical services worldwide.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


